Template:Networking rutos manual routing: Difference between revisions
No edit summary |
No edit summary |
||
| (5 intermediate revisions by 2 users not shown) | |||
| Line 370: | Line 370: | ||
---- | ---- | ||
To create a new BGP instance, look to the Add New Instance section under BGP instances; type in a custom name for the BGP instance and click the 'Add' button or you can | To create a new BGP instance, look to the Add New Instance section under BGP instances; type in a custom name for the BGP instance and click the 'Add' button or you can `Edit` a general instance: | ||
[[File:Networking_rutos_manual_routing_dynamic_routes_bgp_bgp_instance_edit.png|border|class=tlt-border]] | [[File:Networking_rutos_manual_routing_dynamic_routes_bgp_bgp_instance_edit.png|border|class=tlt-border]] | ||
Below is an example of the BGP Instance section: | |||
[[File:Networking_rutos_manual_routing_dynamic_routes_bgp_bgp_instance_v2.png|border|class=tlt-border]] | [[File:Networking_rutos_manual_routing_dynamic_routes_bgp_bgp_instance_v2.png|border|class=tlt-border]] | ||
| Line 426: | Line 426: | ||
</table> | </table> | ||
====BGP Peers==== | |||
---- | ---- | ||
<b>BGP Peers</b> are routers in the same BGP Peer Group that can redistribute routes among other BGP Peers. Below is an example of the BGP Peers section, which is empty by default. | <b>BGP Peers</b> are routers in the same BGP Peer Group that can redistribute routes among other BGP Peers. Below is an example of the BGP Peers section, which is empty by default. | ||
| Line 508: | Line 508: | ||
</table> | </table> | ||
====BGP Peer Groups==== | |||
---- | ---- | ||
A <b>BGP Peer Group</b> is a collection of routers that use the BGP protocol to dynamically redistribute routes among peers (other routers). The figure below is an example of the BGP Peer Groups section, which is empty by default. | A <b>BGP Peer Group</b> is a collection of routers that use the BGP protocol to dynamically redistribute routes among peers (other routers). The figure below is an example of the BGP Peer Groups section, which is empty by default. | ||
| Line 536: | Line 536: | ||
<td>Remote AS</td> | <td>Remote AS</td> | ||
<td>integer [1..65535]; default: <b>none</b></td> | <td>integer [1..65535]; default: <b>none</b></td> | ||
<td> | <td>Remote autonomous system number.</td> | ||
</tr> | </tr> | ||
<tr> | <tr> | ||
<td>Neighbor address</td> | <td>Neighbor address</td> | ||
<td>ip4; default: <b>none</b></td> | <td>ip4; default: <b>none</b></td> | ||
<td> | <td>IPv4 address(es) of a remote BGP Neighbor.</td> | ||
</tr> | </tr> | ||
<tr> | <tr> | ||
| Line 551: | Line 551: | ||
<td>Advertisement interval</td> | <td>Advertisement interval</td> | ||
<td>integer; default: <b>none</b></td> | <td>integer; default: <b>none</b></td> | ||
<td> | <td>BGP advertisement frequency (in seconds).</td> | ||
</tr> | </tr> | ||
<tr> | <tr> | ||
| Line 585: | Line 585: | ||
</table> | </table> | ||
==== | ====Access List Filters==== | ||
---- | ---- | ||
The <b> | The <b>Access List Filters</b> section is used to configure special filters that restrict or allow access to specified networks for BGP Peers. Below is an example of the Access List Filters section which is empty by default. You can add a new filter by clicking the 'Add' button | ||
[[File: | [[File:Networking_rutos_manual_routing_dynamic_routes_bgp_access_list_filters_add_button.png|border|class=tlt-border]] | ||
An | An Access List Filter configuration for BGP should look similar to this: | ||
[[File: | [[File:Networking_rutos_manual_routing_dynamic_routes_bgp_access_list_filters_configuration.png|border|class=tlt-border]] | ||
<table class="nd-mantable"> | <table class="nd-mantable"> | ||
| Line 603: | Line 603: | ||
<tr> | <tr> | ||
<td>Peer</td> | <td>Peer</td> | ||
<td>bgp peer; default: <b> | <td>bgp peer; default: <b>none</b></td> | ||
<td>Applies the filter rule for the specified peer.</td> | <td>Applies the filter rule for the specified peer.</td> | ||
</tr> | </tr> | ||
<tr> | <tr> | ||
<td>Action</td> | |||
<td>Permit {{!}} Deny; default: <b>Permit</b></td> | |||
<td>When BGP traffic matches this rule, the device will take the action specified in this field, which is to either allow or block traffic.</td> | |||
</tr> | |||
<tr> | |||
<td>Network</td> | |||
<td>ip/netmask {{!}} Any; default: <b>Any</b></td> | |||
<td>Matches traffic destined or originating from (depends on 'Direction' selection) to the network specified in this field.</td> | |||
</tr> | </tr> | ||
<tr> | <tr> | ||
<td>Direction</td> | <td>Direction</td> | ||
<td>Inbound {{!}} Outbound; default: <b>Inbound</b></td> | <td>Inbound {{!}} Outbound; default: <b>Inbound</b></td> | ||
<td> | <td>Matches network traffic direction, which can either be traffic destined to this device (Inbound) or traffic originating from this device (Outbound).</td> | ||
</tr> | </tr> | ||
<tr> | <tr> | ||
<td>Enable</td> | <td>Enable</td> | ||
<td>off {{!}} on; default: <b>off</b></td> | <td>off {{!}} on; default: <b>off</b></td> | ||
<td>Turns an | <td>Turns an Access filter on or off.</td> | ||
</tr> | </tr> | ||
</table> | </table> | ||
==== | ====Route Maps==== | ||
---- | ---- | ||
A <b>Route Maps</b> allow you to configure a filtering criteria by defining a set of rules or match statements with a permit or deny condition. It includes a series of match statements to determine if a route matches the criteria defined in the statement and then apply the permit or deny rule accordingly. | |||
[[File:Networking_rutos_manual_routing_dynamic_routes_bgp_route_maps.png|border|class=tlt-border]] | |||
To create a new Route Maps, look to the Add New Instance section under Route Maps; type in a custom name for the Route Map and click the 'Add' button: | |||
[[File: | [[File:Networking_rutos_manual_routing_dynamic_routes_bgp_route_maps_add_button.png|border|class=tlt-border]] | ||
The newly added Route Map configuration should look similar to this: | |||
[[File: | [[File:Networking_rutos_manual_routing_dynamic_routes_bgp_route_maps_added.png|border|class=tlt-border]] | ||
<table class="nd-mantable"> | <table class="nd-mantable"> | ||
| Line 640: | Line 649: | ||
</tr> | </tr> | ||
<tr> | <tr> | ||
<td> | <td>Drag-cursor</td> | ||
<td | <td>- (interactive button)</td> | ||
<td> | <td>Changes the priority(metric) of the route maps.</td> | ||
</tr> | </tr> | ||
<tr> | <tr> | ||
<td>Action</td> | <td>Action</td> | ||
<td>Permit {{!}} Deny; default: <b>Permit</b></td> | <td>Permit {{!}} Deny; default: <b>Permit</b></td> | ||
<td> | <td>IPv4 address of this remote BGP Neighbor.</td> | ||
</tr> | </tr> | ||
<tr> | <tr> | ||
<td>Enable</td> | <td>Enable</td> | ||
<td>off {{!}} on; default: <b>off</b></td> | <td>off {{!}} on; default: <b>off</b></td> | ||
<td>Turns | <td>Turns this Route Map on or off.</td> | ||
</tr> | </tr> | ||
</table> | </table> | ||
To see more settings for a Route Maps, click the 'Edit' button next to it: | |||
To | |||
[[File: | [[File:Networking_rutos_manual_routing_dynamic_routes_bgp_route_maps_edit_button.png|border|class=tlt-border]] | ||
The full Route Maps configuration page should look similar to this: | |||
[[File: | [[File:Networking_rutos_manual_routing_dynamic_routes_bgp_route_maps_edit.png|border|class=tlt-border]] | ||
<table class="nd-mantable"> | <table class="nd-mantable"> | ||
| Line 705: | Line 698: | ||
<td>ip4 with mask; default: <b>none</b></td> | <td>ip4 with mask; default: <b>none</b></td> | ||
<td>Sets a metric value for determining the preferred path into an AS.</td> | <td>Sets a metric value for determining the preferred path into an AS.</td> | ||
</tr> | |||
</table> | |||
====Route Map Filters==== | |||
---- | |||
The <b>Route Map Filters</b> section is used to configure special filters that changes direction for BGP Peers. Below is an example of the Route Map Filters section which is empty by default. You can add a new filter by clicking the 'Add' button | |||
[[File:Networking_rutos_manual_routing_dynamic_routes_bgp_route_maps_filters_add_button.png|border|class=tlt-border]] | |||
An Route Map Filters configuration for BGP should look similar to this: | |||
[[File:Networking_rutos_manual_routing_dynamic_routes_bgp_route_maps_filters_configuration.png|border|class=tlt-border]] | |||
<table class="nd-mantable"> | |||
<tr> | |||
<th>Field</th> | |||
<th>Value</th> | |||
<th>Description</th> | |||
</tr> | |||
<tr> | |||
<td>Peer</td> | |||
<td>bgp peer; default: <b>none</b></td> | |||
<td>Applies the filter rule for the specified peer.</td> | |||
</tr> | |||
<tr> | |||
<td>Route map</td> | |||
<td>route map; default: <b>none</b></td> | |||
<td>Route map filter to apply.</td> | |||
</tr> | |||
<tr> | |||
<td>Direction</td> | |||
<td>Inbound {{!}} Outbound; default: <b>Inbound</b></td> | |||
<td>If direction is Inbound, the access list is applied to input routes. If direction is Outbound the access list is applied to advertised routes.</td> | |||
</tr> | |||
<tr> | |||
<td>Enable</td> | |||
<td>off {{!}} on; default: <b>off</b></td> | |||
<td>Turns an Route Map filter on or off.</td> | |||
</tr> | </tr> | ||
</table> | </table> | ||
| Line 1,192: | Line 1,223: | ||
The <b>Interfaces</b> section is used to define which existing network interfaces can participate in NHRP communication. Below is an example of the NHRP Interfaces section which is empty by default. | The <b>Interfaces</b> section is used to define which existing network interfaces can participate in NHRP communication. Below is an example of the NHRP Interfaces section which is empty by default. | ||
[[File: | [[File:Networking_rutos_manual_routing_dynamic_routes_nhrp_interfaces.png|border|class=tlt-border]] | ||
To create a new NHRP Interface, look to the Add New Interface section; enter a custom name and click the 'Add' button. | To create a new NHRP Interface, look to the Add New Interface section; enter a custom name and click the 'Add' button. | ||
[[File: | [[File:Networking_rutos_manual_routing_dynamic_routes_nhrp_interfaces_add_button.png|border|class=tlt-border]] | ||
The newly added NHRP interface will appear in the Interfaces list and should look similar to this: | The newly added NHRP interface will appear in the Interfaces list and should look similar to this: | ||
[[File: | [[File:Networking_rutos_manual_routing_dynamic_routes_nhrp_interfaces_begin_to_edit.png|border|class=tlt-border]] | ||
To see more settings for an NHRP Interface, click the 'Edit' button next to it: | |||
[[File:Networking_rutos_manual_routing_dynamic_routes_nhrp_interfaces_edit_button.png|border|class=tlt-border]] | |||
[[File: | You should redirected to a windows that looks similar to this: | ||
[[File:Networking_rutos_manual_routing_dynamic_routes_nhrp_interfaces_interface_configuration.png|border|class=tlt-border]] | |||
<table class="nd-mantable"> | <table class="nd-mantable"> | ||
| Line 1,234: | Line 1,269: | ||
<tr> | <tr> | ||
<td>NHS</td> | <td>NHS</td> | ||
<td> | <td>Dynamic {{!}} custom(ip4); default: <b>none</b></td> | ||
<td>IP address of a Next-Hop server.</td> | <td>IP address of a Next-Hop server.</td> | ||
</tr> | </tr> | ||
| Line 1,263: | Line 1,298: | ||
The <b>NHRP Mappings Configuration</b> section is used to configure (map) associations between NHRP router IP address and NBMAs. Below is an example of the NHRP Mappings Configuration section which is empty by default. To add a new configuration, simply click the 'Add' button: | The <b>NHRP Mappings Configuration</b> section is used to configure (map) associations between NHRP router IP address and NBMAs. Below is an example of the NHRP Mappings Configuration section which is empty by default. To add a new configuration, simply click the 'Add' button: | ||
[[File: | [[File:Networking_rutos_manual_routing_dynamic_routes_nhrp_interfaces_nhrp_mappings_configuration_add_button.png|border|class=tlt-border]] | ||
The newly added configuration should appear in the NHRP Mappings Configuration list and look similar to this: | The newly added configuration should appear in the NHRP Mappings Configuration list and look similar to this: | ||
[[File: | [[File:Networking_rutos_manual_routing_dynamic_routes_nhrp_interfaces_nhrp_mappings_configuration_edit.png|border|class=tlt-border]] | ||
<table class="nd-mantable"> | <table class="nd-mantable"> | ||
| Line 1,274: | Line 1,309: | ||
<th>Value</th> | <th>Value</th> | ||
<th>Description</th> | <th>Description</th> | ||
</tr> | </tr> | ||
<tr> | <tr> | ||
| Line 1,289: | Line 1,314: | ||
<td>off {{!}} on; default: <b>off</b></td> | <td>off {{!}} on; default: <b>off</b></td> | ||
<td>Turns this mapping configuration on or off.</td> | <td>Turns this mapping configuration on or off.</td> | ||
</tr> | </tr> | ||
<tr> | <tr> | ||
<td> | <td>IP Address</td> | ||
<td>ip4; default: <b>none</b></td> | <td>ip4; default: <b>none</b></td> | ||
<td> | <td>Network ID of another NHRP router.</td> | ||
</tr> | </tr> | ||
<tr> | <tr> | ||
<td>NBMA</td> | <td>NBMA</td> | ||
<td>ip4; default: <b>none</b></td> | <td>ip4; default: <b>none</b></td> | ||
<td> | <td>IP address of a Next-Hop server.</td> | ||
</tr> | </tr> | ||
</table>|}} | </table>|}} | ||
[[Category:{{{name}}} Network section]] | [[Category:{{{name}}} Network section]] | ||
Revision as of 08:17, 17 April 2024
The information in this page is updated in accordance with firmware version .
Summary
The Routing page is used to set up static routes, routing tables and rules.
This manual page provides an overview of the Routing windows in {{{name}}} devices.
If you're having trouble finding this page or some of the parameters described here on your device's WebUI, you should turn on "Advanced WebUI" mode. You can do that by clicking the "Advanced" button, located at the top of the WebUI.
Static Routes
Routes ensure that network traffic finds its path to a specified host or network, both in local and remote network scenarios. Static routes are simply fixed routing entries in the routing table(s).
This section provides the possibility to configure custom static routes.
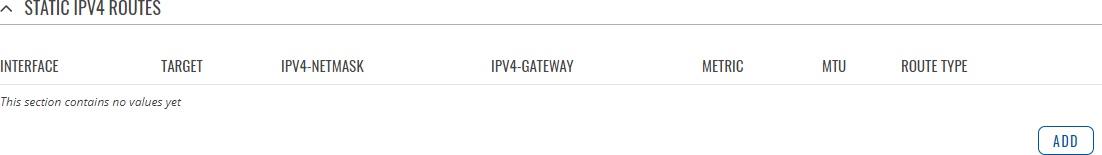
Static IPv4 Routes
The Static IPv4 Routes section displays a list of user defined static IPv4 routes and provides the possibility to add and configure new ones. The list is empty by default.
To add a new route and begin editing, simply click the 'Add' button. Refer to the table below for information on static route configuration fields.
| Field | Value | Description |
|---|---|---|
| Interface | network interface; default: lan | Network interface of the target network. |
| Target* | ip4; default: none | Destination network address. |
| IPv4-Netmask* | netmask; default: none | A netmask is used to divide an IP address into sub-networks (subnets). Combined together, the 'Netmask' and 'Target' values define the exact destination network or IP address to which this route applies. |
| IPv4-Gateway | ip4; default: none | A gateway can be any machine in a network that is capable of serving as an access point to another network. Traffic that matches this route will be directed over the IP address specified in this field. |
| Metric | integer [0..255]; default: none | The metric value acts as a measurement of priority. If a packet about to be routed matches two or more rules, the one with the lower metric is applied. |
| MTU | integer [64..9000]; default: 1500 | Sets the maximum transmission unit (MTU) size. It is the largest size of a protocol data unit (PDU) that can be transmitted in a single network layer transaction. |
| Route Type | unicast | local | broadcast | multicast | unreachable | prohibit | backhole | anycast | -- custom -- ; default: unicast | Selects route type. Each type specifies a different behavior for the route:
|
*Additional notes on 'Target' & 'Netmask' fields:
You can define a rule that applies to a single IP like this:
- Target: some IP
- Netmask: 255.255.255.255
Furthermore, you can create target/netmask combinations that apply to a range of IPs. Refer to the table below for examples.
| Target | Netmask | Network range |
|---|---|---|
| 192.168.2.0 | 255.255.255.240 | 192.168.2.0 - 192.168.2.15 |
| 192.168.2.240 | 255.255.255.240 | 192.168.2.240 - 192.168.2.255 |
| 192.168.2.161 | 255.255.255.0 | 192.168.2.0 - 192.168.55.255 |
| 192.168.0.0 | 255.255.0.0 | 192.168.0.0 - 192.168.255.255 |
| 192.168.2.161 | 255.255.255.255 | 192.168.2.161 |
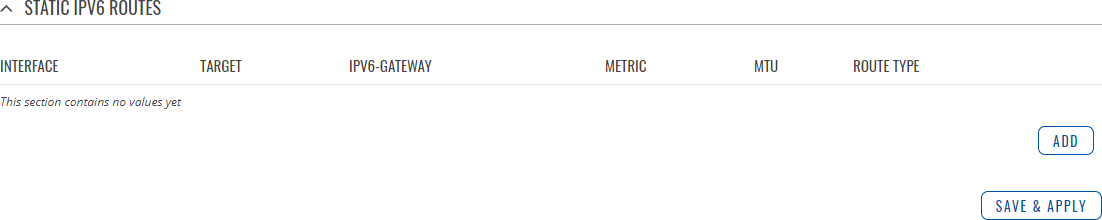
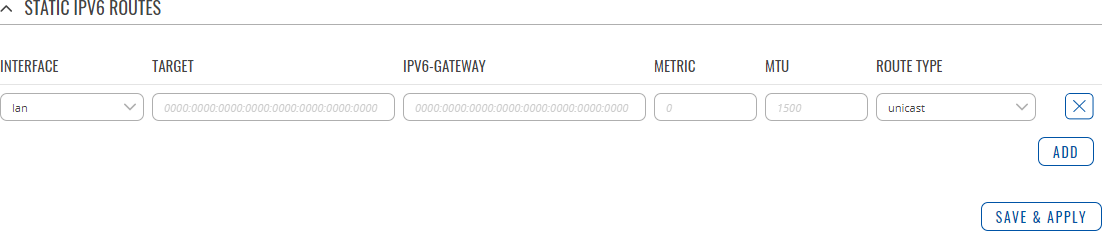
Static IPv6 Routes
The Static IPv6 Routes section displays a list of user defined static IPv6 routes and provides the possibility to add and configure new ones. The list is empty by default.
To add a new route and begin editing, simply click the 'Add' button. Refer to the table below for information on static route configuration fields.
| Field | Value | Description |
|---|---|---|
| Interface | network interface; default: lan | Network interface of the target network. |
| Target | ip6; default: none | Destination network address. |
| IPv6-Gateway | ip6; default: none | A gateway can be any machine in a network that is capable of serving as an access point to another network. Traffic that matches this route will be directed over the IP address specified in this field. |
| Metric | integer [0..255]; default: none | The metric value acts as a measurement of priority. If a packet about to be routed matches two or more rules, the one with the lower metric is applied. |
| MTU | integer [64..9000]; default: 1500 | Sets the maximum transmission unit (MTU) size. It is the largest size of a protocol data unit (PDU) that can be transmitted in a single network layer transaction. |
| Route Type | unicast | local | broadcast | multicast | unreachable | prohibit | backhole | anycast | -- custom -- ; default: unicast | Selects route type. Each type specifies a different behavior for the route:
|
Policy Based Routing
The Policy Based Routing section is used to configure policy-based routing infrastructures, which are usually used in more complex or specific networking scenarios.
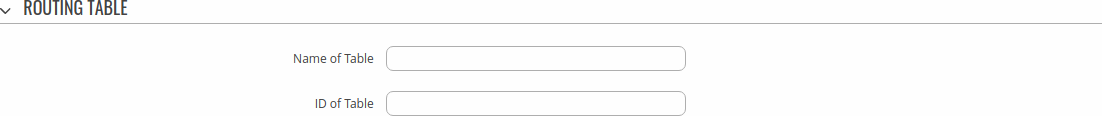
Routing Tables
Routing Tables store network routes. Tables are checked before every routing decision until a matching route is found. Having multiple tables allows the user to set up a policy routing infrastructure. Policy-based routing is a technique where routing decisions are based on policies (rule) set by the user.
The 'Routing Tables' section displays user created routing tables. By default, the list is empty.
To create a new table, look to the 'Add New Routing Table' section below. Enter an ID for the new table in the range of [1..252], enter a custom name and click the 'Add' button. The new table should appear in the 'Routing Tables' list. Click the 'Edit' button next to it to begin editing.
Refer to the table below for information on configuration fields for routing tables.
| Field | Value | Description |
|---|---|---|
| Name of Table | string; default: none | A custom name for the table. A table can be invoked by the both its ID or name. |
| ID of Table | integer [1..252]; default: none | Unique numerical identifier for the table. A table can be invoked by the both its ID or name. |
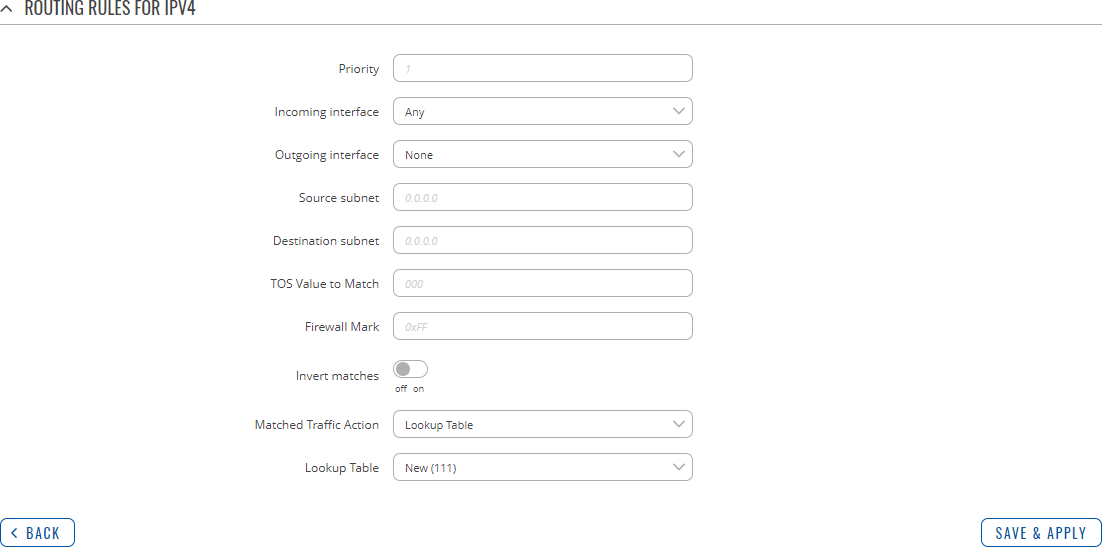
Routing Rules For IPv4
Routing Rules provide a way to route certain packets with exceptions, i.e., in accordance to a rule. 'Routing Rules For IPv4' displays user defined routing rules. It is empty by default. To create a new rule, click the 'Add' button and begin editing by clicking the 'Edit' button located to the right of the newly created rule.
Refer to table below for information on each configuration field.
| Field | Value | Description |
|---|---|---|
| Priority | integer [0..65535]; default: none | Controls the order of IP rules. Rules with a lower priority value will be checked first. |
| Incoming interface | network interface | Any; default: Any | Logical interface name for incoming traffic. Select 'Any' to make the rule apply to all network interfaces. |
| Outgoing interface | network interface | None; default: None | Logical interface name for incoming traffic. Select 'None' to ignore outgoing interface. |
| Source subnet | netmask; default: none | Source subnet to match the rule. |
| Destination subnet | netmask; default: none | Destination subnet to match the rule. |
| TOS Value to Match | integer [0..255]; default: none | The type of service (ToS) value to match in IP headers. |
| Firewall Mark | integer [0..255] | hex [0x00..0xFF]; default: none | Specifies the fwmark and optionally its mask to match. For example, 0xFF to match mark 255 or 0x0/0x1 to match any even mark value. |
| Invert matches | off | on; default: off | If enabled, the meaning of the match options (Firewall Mark, TOS Value, Source and Destination subnets) is inverted. |
| Matched Traffic Action | Lookup Table | Jump to rule | Routing Action; default: Lookup Table | When network traffic matches this rule, the device will take an action specified in this field:
|
| Lookup Table | routing table; default: none | Specifies a table for routing traffic that matches this rule. This field is visible only when 'Matched Traffic Action' is set to Lookup Table. |
| Jump to rule | rule priority number; default: none | Specifies a another rule to follow for traffic that matches this rule. This field is visible only when 'Matched Traffic Action' is set to Jump to rule. |
| Routing Action | Prohibit | Unreachable | Blackhole | Throw; default: Prohibit | When traffic matches this rule, the action specified in this field will be executed. This field is visible only when 'Matched Traffic Action' is set to Routing Action. |
[[Category:{{{name}}} Network section]]