Template:Networking RUTX configuration example cisco ipsec: Difference between revisions
(Created page with "==Introduction== In computing, Internet Protocol Security (IPsec) is a secure network protocol suite of IPv4 that authenticates and encrypts the packets of data sent over an...") |
|||
| (10 intermediate revisions by the same user not shown) | |||
| Line 15: | Line 15: | ||
==Configuration scheme== | ==Configuration scheme== | ||
[[File: | [[File:Networking_RUTXxx_configuration_example_ipsec_topology_v1.png|border|class=tlt-border|1100x1100px]] | ||
==RUTX configuration== | ==RUTX configuration== | ||
| Line 21: | Line 21: | ||
Connect to router's '''WebUI''', go to '''Services > VPN > IPsec'''. Enter a name for your IPsec instance, click '''ADD''' and when it appears in '''IPsec Configuration''' field, click '''Edit'''. | Connect to router's '''WebUI''', go to '''Services > VPN > IPsec'''. Enter a name for your IPsec instance, click '''ADD''' and when it appears in '''IPsec Configuration''' field, click '''Edit'''. | ||
[[File: | [[File:Networking_RUTXxx_configuration_example_rutx_ipsec_instance_v1.png]] | ||
Then apply the configuration presented below. | Then apply the configuration presented below. | ||
[[File: | [[File:Networking_RUTXxx_configuration_example_ipsec_rutx_settings_v1.png|border|class=tlt-border|1100x1100px]] | ||
# '''Enable''' instance. | # '''Enable''' instance. | ||
# | # Add '''Remote endpoint''' (the Public IP address of the Cisco router). | ||
# Write ''' | # Write '''Pre shared key''' (a shared password used for authentication between the peers. The value of this field must match on both instances). | ||
# | # Set '''Local identifier''' (device identifier for IPsec tunnel, write RUTX LAN IP address). | ||
# Set '''Remote identifier''' (remote address | # Set '''Remote identifier''' (remote device identifier for IPsec tunnel, write Cisco LAN IP address). | ||
# Write ''' | # Write '''Local subnet''' (an IP address/Subnet mask of the router on which the IPsec instance is configured). | ||
# Write '''Remote subnet''' (LAN IP address/Subnet mask of the Cisco router). | |||
Next step in configuring IPsec instance is '''Phase''' settings. For this example we | Next step in configuring IPsec instance is '''Phase''' settings. For this example we changed '''Encryption algorithm''' to '''3DES''' and added '''8h''' '''Lifetime'''. Match this configuration in both '''Phase 1''' and '''Phase 2''' settings. | ||
[[File: | [[File:Networking_RUTXxx_configuration_example_ipsec_rutx_phase1_v1.png|border|class=tlt-border|1100x1100px]] | ||
---- | ---- | ||
[[File: | [[File:Networking_RUTXxx_configuration_example_ipsec_rutx_phase2_v1.png|border|class=tlt-border|1100x1100px]] | ||
When you're finished with the configuration, click '''Save''' button and then you will be prompted back to IPsec window | When you're finished with the configuration, click '''Save''' button and then you will be prompted back to IPsec window. | ||
==Cisco configuration== | ==Cisco configuration== | ||
| Line 71: | Line 65: | ||
# Select '''Group: Group''' (5). | # Select '''Group: Group''' (5). | ||
When you are | When you are done with '''IPsec Profiles''', save settings, go to '''Site-to-Site''' settings and apply the following configuration: | ||
[[File:Networking_rutxxx_configuration_example_ipsec_cisco_s2s_v2.png|border|class=tlt-border]] | [[File:Networking_rutxxx_configuration_example_ipsec_cisco_s2s_v2.png|border|class=tlt-border]] | ||
| Line 97: | Line 91: | ||
If you've followed all the steps presented above, your configuration should be finished. But as with any other configuration, it is always wise to test the setup in order to make sure that it works properly. In order to test an IPsec connection, login to the RUTX WebUI and go to '''Services → CLI'''. Login with user name: '''root''' and the router's admin password. From there you should then be able to '''ping''' the opposite instance's LAN IP address. To use a ping command, type '''ping <ip_address>''' and press the "Enter" key on your keyboard: | If you've followed all the steps presented above, your configuration should be finished. But as with any other configuration, it is always wise to test the setup in order to make sure that it works properly. In order to test an IPsec connection, login to the RUTX WebUI and go to '''Services → CLI'''. Login with user name: '''root''' and the router's admin password. From there you should then be able to '''ping''' the opposite instance's LAN IP address. To use a ping command, type '''ping <ip_address>''' and press the "Enter" key on your keyboard: | ||
[[File: | [[File:Networking_RUTXxx_configuration_example_ipsec_ping_v1.png]] | ||
You can also test if LAN access is working the same way. Instead of pinging the opposite instance's LAN IP address, ping one of the end device's IPs. One common issue that can be encountered here is that the end devices '''might need their DHCP leases renewed'''. There are many methods of accomplishing this, but the easiest and most accessible way is to simply disconnect and reconnect the LAN cable to device or the router that it's connected to. | You can also test if LAN access is working the same way. Instead of pinging the opposite instance's LAN IP address, ping one of the end device's IPs. One common issue that can be encountered here is that the end devices '''might need their DHCP leases renewed'''. There are many methods of accomplishing this, but the easiest and most accessible way is to simply disconnect and reconnect the LAN cable to device or the router that it's connected to. | ||
If the ping requests are successful, congratulations, your setup works! If not, we suggest that you review all steps once more. | If the ping requests are successful, congratulations, your setup works! If not, we suggest that you review all steps once more. | ||
Latest revision as of 09:44, 2 April 2020
Introduction
In computing, Internet Protocol Security (IPsec) is a secure network protocol suite of IPv4 that authenticates and encrypts the packets of data sent over an IPv4 network. IPsec includes protocols for establishing mutual authentication between agents at the beginning of the session and negotiation of cryptographic keys to use during the session. IPsec can protect data flows between a pair of hosts (host-to-host), between a pair of security gateways (network-to-network), or between a security gateway and a host (network-to-host). Internet Protocol security (IPsec) uses cryptographic security services to protect communications over Internet Protocol (IP) networks. IPsec supports network-level peer authentication, data-origin authentication, data integrity, data confidentiality (encryption), and replay protection.
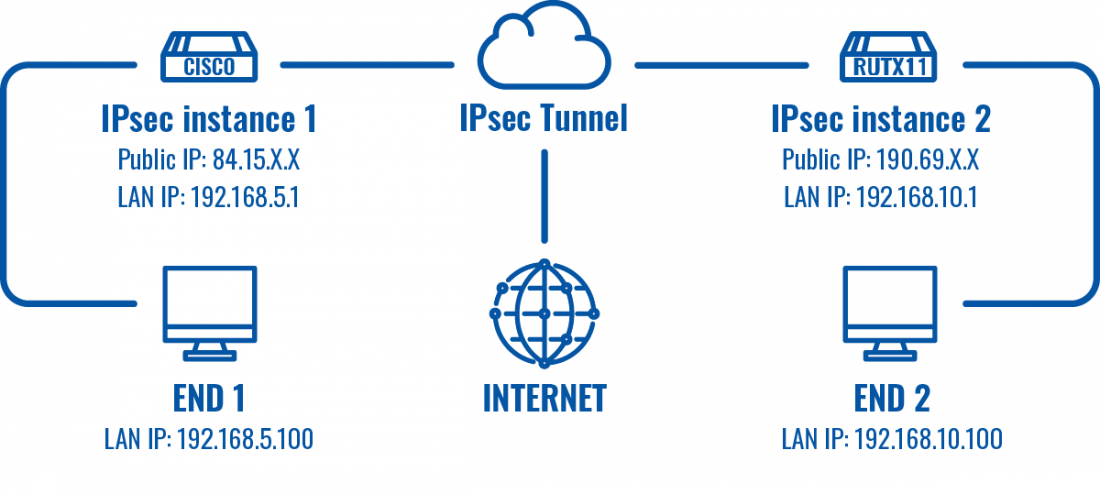
This article provides an extensive configuration example with details on how to create a tunnel connection between two IPsec instances, one of which is configured on RUTXxx router and the other one on Cisco device.
Prerequisites
- One RUTXxx router of any type
- One Cisco router (this configuration example was created using Cisco RV340W)
- At least one router must have a Public Static or Public Dynamic IP address
- At least one end device (PC, Laptop, Tablet, Smartphone) to configure the routers
- (Optional) A second end device to configure and test remote LAN access
Configuration scheme
RUTX configuration
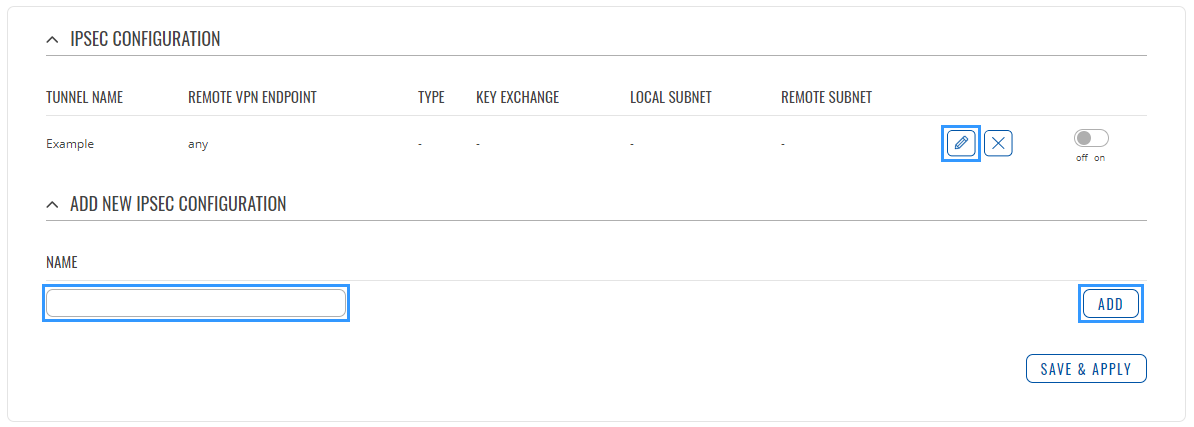
Connect to router's WebUI, go to Services > VPN > IPsec. Enter a name for your IPsec instance, click ADD and when it appears in IPsec Configuration field, click Edit.
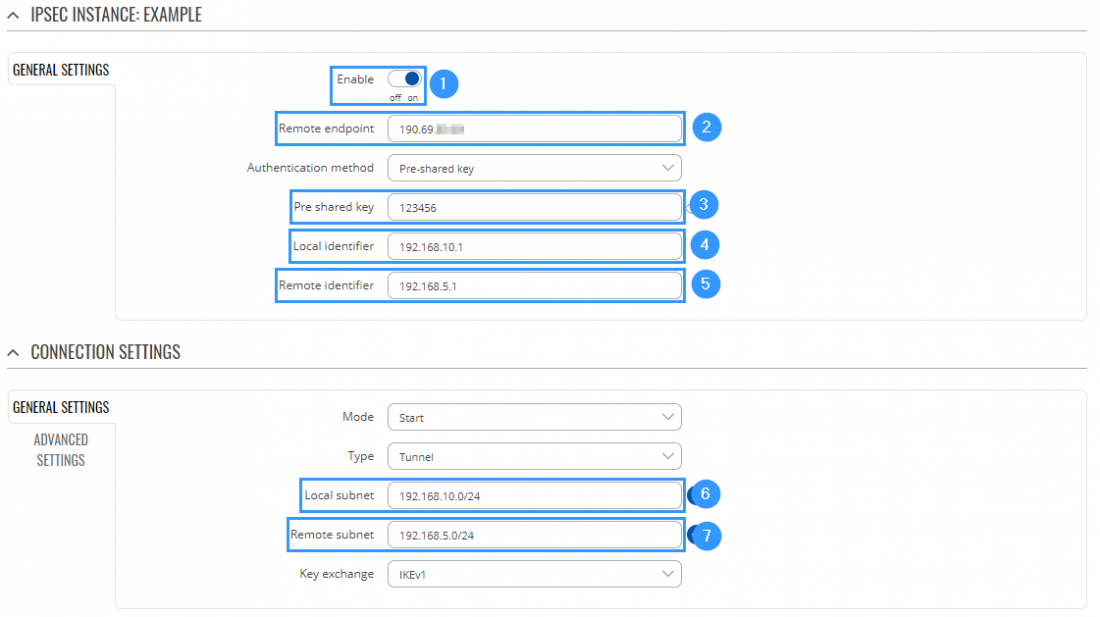
Then apply the configuration presented below.
- Enable instance.
- Add Remote endpoint (the Public IP address of the Cisco router).
- Write Pre shared key (a shared password used for authentication between the peers. The value of this field must match on both instances).
- Set Local identifier (device identifier for IPsec tunnel, write RUTX LAN IP address).
- Set Remote identifier (remote device identifier for IPsec tunnel, write Cisco LAN IP address).
- Write Local subnet (an IP address/Subnet mask of the router on which the IPsec instance is configured).
- Write Remote subnet (LAN IP address/Subnet mask of the Cisco router).
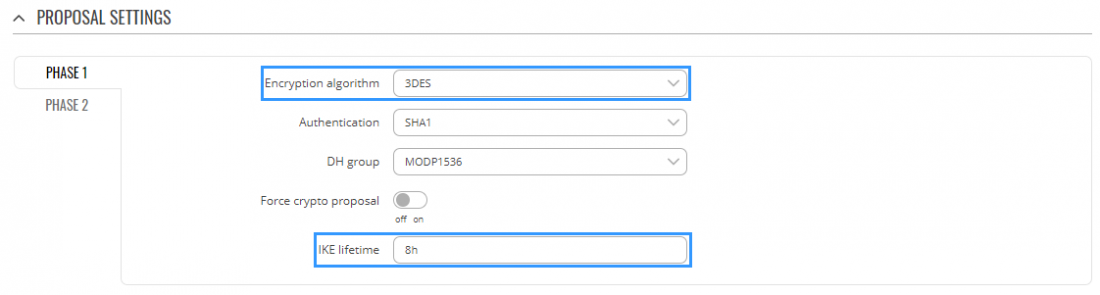
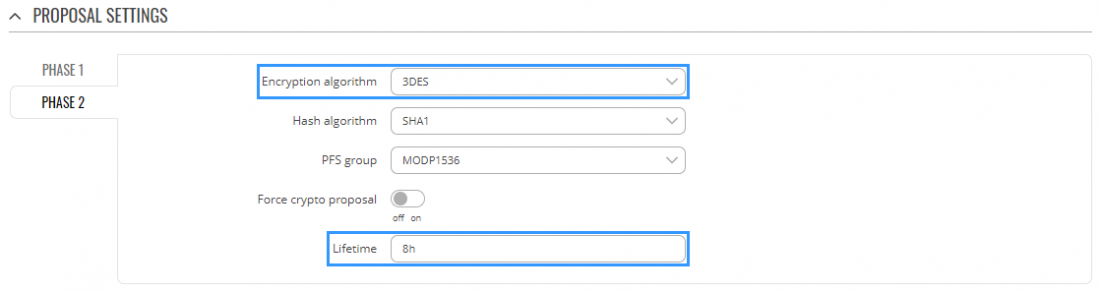
Next step in configuring IPsec instance is Phase settings. For this example we changed Encryption algorithm to 3DES and added 8h Lifetime. Match this configuration in both Phase 1 and Phase 2 settings.
When you're finished with the configuration, click Save button and then you will be prompted back to IPsec window.
Cisco configuration
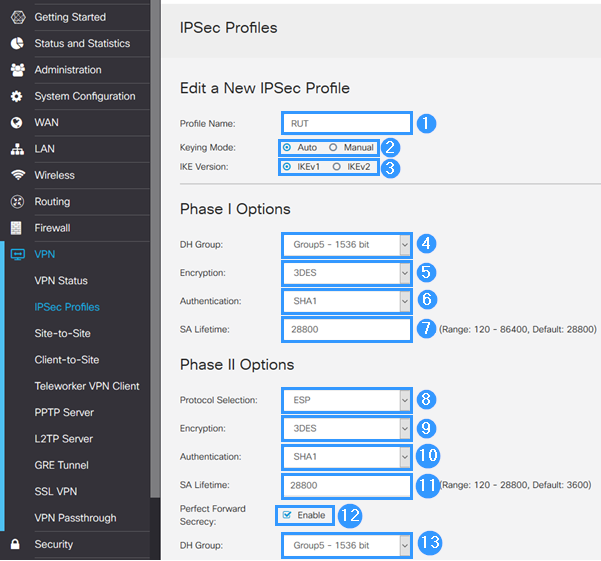
Connect to router's WebUI, go to VPN > IPsec Profiles and apply the following configuration.
- Add Profile Name (anything you want).
- Choose Keying Mode (Auto).
- Choose IKE version (IKEv1).
- Select DH Group (Group 5).
- Select Encryption (3DES).
- Choose Authentication (SHA1).
- Set SA Lifetime (28800).
- Choose protocol in Protocol Selection (ESP).
- Select Encryption (3DES).
- Select Authentication (SHA1).
- Set SA Lifetime (28800).
- Enable Perfect Forward Secrecy.
- Select Group: Group (5).
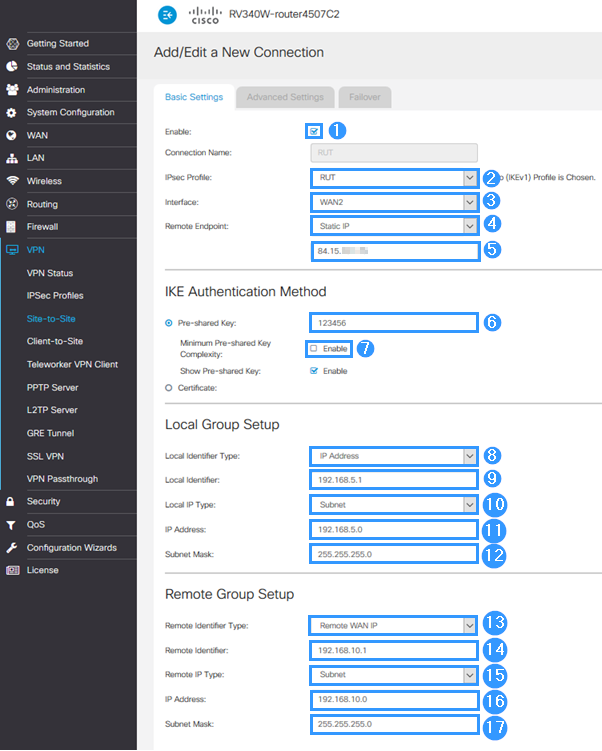
When you are done with IPsec Profiles, save settings, go to Site-to-Site settings and apply the following configuration:
- Enable it.
- Select IPsec Profile (RUTX).
- Set Interface (your internet source).
- Select Remote Endpoint (static IP).
- Write RUTX Public IP.
- Add Pre Shared Key (a shared password used for authentication between the peers. The value of this field must match on both instances).
- Disable Minimum Key complexity.
- Select Local Identifier Type (IP Address).
- Write Local Identifier (Cisco LAN IP address).
- Select Local IP Type (Subnet).
- Write IP Address (Cisco local network).
- Add Subnet Mask (network mask).
- Select Remote Identifier Type (Remote WAN IP).
- Write Remote Identifier (RUTX LAN IP).
- Select Remote IP Type (Subnet).
- Add IP Address (RUTX local network).
- Add Subnet Mask (RUTX local network mask).
Testing the setup
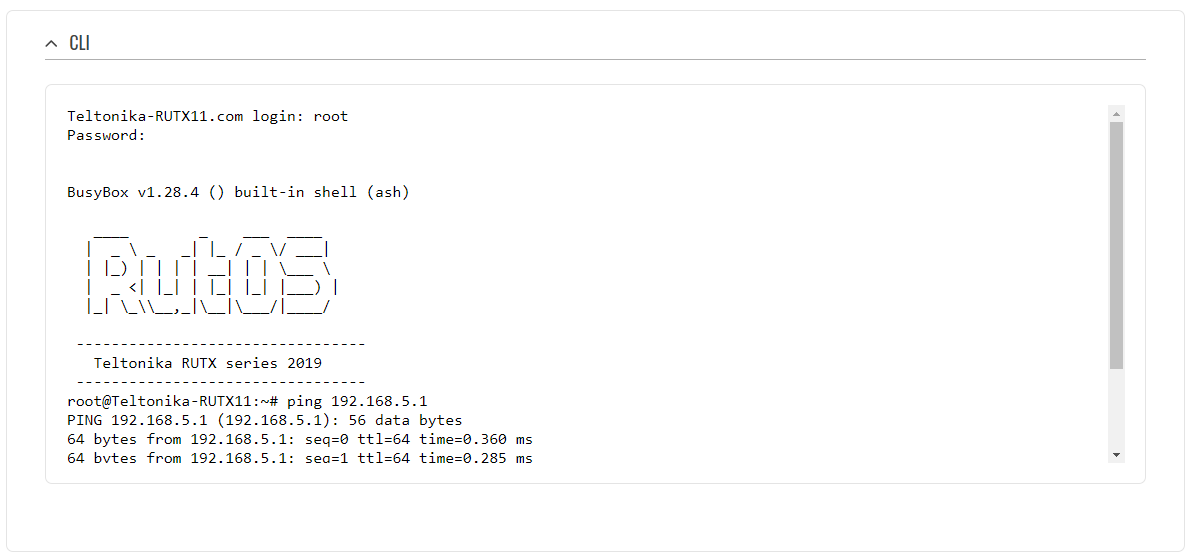
If you've followed all the steps presented above, your configuration should be finished. But as with any other configuration, it is always wise to test the setup in order to make sure that it works properly. In order to test an IPsec connection, login to the RUTX WebUI and go to Services → CLI. Login with user name: root and the router's admin password. From there you should then be able to ping the opposite instance's LAN IP address. To use a ping command, type ping <ip_address> and press the "Enter" key on your keyboard:
You can also test if LAN access is working the same way. Instead of pinging the opposite instance's LAN IP address, ping one of the end device's IPs. One common issue that can be encountered here is that the end devices might need their DHCP leases renewed. There are many methods of accomplishing this, but the easiest and most accessible way is to simply disconnect and reconnect the LAN cable to device or the router that it's connected to.
If the ping requests are successful, congratulations, your setup works! If not, we suggest that you review all steps once more.