Template:Networking rutos manual vpn: Difference between revisions
(prepare for release) |
Frozen light (talk | contribs) m (→OpenVPN Client) |
||
| (28 intermediate revisions by 5 users not shown) | |||
| Line 1: | Line 1: | ||
<!-- Template uses {{{name}}}, {{{series}}} --> | <!-- Template uses {{{name}}}, {{{series}}} --> | ||
{{Template:Networking_rutos_manual_fw_disclosure | {{Template:Networking_rutos_manual_fw_disclosure | ||
| fw_version = {{{series}}}_R_00. | | fw_version = {{{series}}}_R_00.07.01 | ||
| series = {{{series}}} | | series = {{{series}}} | ||
}} | }} | ||
{{#ifeq: {{{series}}} | RUT9 |<br><i><b>Note</b>: <b>[[{{{name}}} VPN (legacy WebUI)|click here]]</b> for the old style WebUI (FW version RUT9XX_R_00.06.08.3 and earlier) user manual page.</i>|}} | |||
{{#ifeq: {{{series}}} | RUT2 |<br><i><b>Note</b>: <b>[[{{{name}}} VPN (legacy WebUI)|click here]]</b> for the old style WebUI (FW version RUT2XX_R_00.01.14.1 and earlier) user manual page.</i>|}} | |||
==Summary== | ==Summary== | ||
| Line 22: | Line 21: | ||
<b>OpenVPN</b> is an open-source software application that implements virtual private network (VPN) techniques for creating secure point-to-point or site-to-site connections in routed or bridged configurations and remote access facilities. It is often regarded as being the most universal VPN protocol because of its flexibility, support of SSL/TLS security, multiple encryption methods, many networking features and compatibility with most OS platforms. | <b>OpenVPN</b> is an open-source software application that implements virtual private network (VPN) techniques for creating secure point-to-point or site-to-site connections in routed or bridged configurations and remote access facilities. It is often regarded as being the most universal VPN protocol because of its flexibility, support of SSL/TLS security, multiple encryption methods, many networking features and compatibility with most OS platforms. | ||
{{{name}}} devices run OpenVPN version <b>2. | {{{name}}} devices run OpenVPN version <b>2.5.2</b>. | ||
===OpenVPN | ===OpenVPN Client=== | ||
---- | ---- | ||
An <b>OpenVPN client</b> is an entity that initiates a connection to an OpenVPN server. To create a new client instance, go to the <i>Services → VPN → OpenVPN</i> section, select <i>Role: Client</i>, enter a custom name and click the 'Add' button. An OpenVPN client instance with the given name will appear in the "OpenVPN Configuration" list. | An <b>OpenVPN client</b> is an entity that initiates a connection to an OpenVPN server. To create a new client instance, go to the <i>Services → VPN → OpenVPN</i> section, select <i>Role: Client</i>, enter a custom name and click the 'Add' button. An OpenVPN client instance with the given name will appear in the "OpenVPN Configuration" list. | ||
To begin configuration, click the button that looks | To begin configuration, click the button that looks like a pencil next to the client instance. Refer to the figure and table below for information on the OpenVPN client's configuration fields: | ||
[[File: | [[File:Networking_trb2_vpn_openvpn_client_configuration_v2.png|border|class=tlt-border|]] | ||
<table class="nd-mantable"> | <table class="nd-mantable"> | ||
| Line 42: | Line 41: | ||
<td>off {{!}} on; default: <b>off</b></td> | <td>off {{!}} on; default: <b>off</b></td> | ||
<td>Turns the OpenVPN instance on or off.</td> | <td>Turns the OpenVPN instance on or off.</td> | ||
</tr> | |||
<tr> | |||
<td>Enable external Services</td> | |||
<td>off {{!}}<span style="color:#FF8000 ;"> on</span>; default: <b>off</b></td> | |||
<td>Turns the OpenVPN external Services on or off.</td> | |||
</tr> | |||
<tr> | |||
<td><span style="color:#FF8000 ;">VPN providers</span></td> | |||
<td>Express VPN {{!}} Nord VPN; default: <b>Nord VPN</b></td> | |||
<td>Represents a list of available VPN providers. </td> | |||
</tr> | |||
<tr> | |||
<td><span style="color:#FF8000 ;">VPN servers</span></td> | |||
<td>United Kingdom {{!}} USA {{!}} Australia {{!}} South Africa {{!}} Custom; default: <b>United Kingdom</b></td> | |||
<td>Represents a list of available VPN servers. </td> | |||
</tr> | </tr> | ||
<tr> | <tr> | ||
| Line 47: | Line 61: | ||
<td>off {{!}} on; default: <b>off</b></td> | <td>off {{!}} on; default: <b>off</b></td> | ||
<td>Enables or disables custom OpenVPN config from file.</td> | <td>Enables or disables custom OpenVPN config from file.</td> | ||
</tr> | |||
<tr> | |||
<td><span style="color:#FF8000 ;">Username</span></td> | |||
<td>string; default: <b>none</b></td> | |||
<td>Username used for authentication to the VPN server.</td> | |||
</tr> | |||
<tr> | |||
<td><span style="color:#FF8000 ;">Password</span></td> | |||
<td>string; default: <b>none</b></td> | |||
<td>Password used for authentication to the VPN server.</td> | |||
</tr> | </tr> | ||
<tr> | <tr> | ||
| Line 60: | Line 84: | ||
<tr> | <tr> | ||
<td>Protocol</td> | <td>Protocol</td> | ||
<td>UDP {{!}} TCP; default: <b>UDP</b></td> | <td>UDP {{!}} TCP{{#ifeq:{{{series}}}|RUTX| {{!}} UDP6 {{!}} TCP6}}; default: <b>UDP</b></td> | ||
<td>Transfer protocol used by the OpenVPN connection. | <td>Transfer protocol used by the OpenVPN connection. | ||
<ul> | <ul> | ||
| Line 75: | Line 99: | ||
<tr> | <tr> | ||
<td>LZO</td> | <td>LZO</td> | ||
<td> | <td>Yes {{!}} No {{!}} None; default: <b>None</b></td> | ||
<td>Turns LZO data compression on or off.</td> | <td>Turns LZO data compression on or off.</td> | ||
</tr> | </tr> | ||
| Line 161: | Line 185: | ||
<td>Extra OpenVPN options to be used by the OpenVPN instance.</td> | <td>Extra OpenVPN options to be used by the OpenVPN instance.</td> | ||
</tr> | </tr> | ||
<tr> | |||
<td>Certificate files from device</td> | |||
<td>off {{!}} on; default: <b>off</b></td> | |||
<td>Turn on this option if you want to select generated certificate files from device.</td> | |||
</tr> | |||
<tr> | <tr> | ||
<td><span style="color: red;">TLS</span>/<span style="color: #0054a6;">Password:</span> HMAC authentication algorithm</td> | <td><span style="color: red;">TLS</span>/<span style="color: #0054a6;">Password:</span> HMAC authentication algorithm</td> | ||
| Line 168: | Line 197: | ||
<tr> | <tr> | ||
<td><span style="color: red;">TLS</span>/<span style="color: #0054a6;">Password:</span> Additional HMAC authentication</td> | <td><span style="color: red;">TLS</span>/<span style="color: #0054a6;">Password:</span> Additional HMAC authentication</td> | ||
<td>off {{!}} on; default: <b> | <td>off {{!}} on; default: <b>off</b></td> | ||
<td>An additional layer of HMAC authentication on top of the TLS control channel to protect against DoS attacks.</td> | <td>An additional layer of HMAC authentication on top of the TLS control channel to protect against DoS attacks.</td> | ||
</tr> | </tr> | ||
| Line 220: | Line 249: | ||
</ul> | </ul> | ||
===OpenVPN | ===OpenVPN Server=== | ||
---- | ---- | ||
An <b>OpenVPN server</b> is an entity that waits for incoming connections from OpenVPN clients. To create a new server instance, go to the <i>Services → VPN → OpenVPN</i> section, select <i>Role: Server</i>, enter a custom name and click the 'Add' button. An OpenVPN server instance with the given name will appear in the "OpenVPN Configuration" list. Only one OpenVPN server instance is allowed to be added. | An <b>OpenVPN server</b> is an entity that waits for incoming connections from OpenVPN clients. To create a new server instance, go to the <i>Services → VPN → OpenVPN</i> section, select <i>Role: Server</i>, enter a custom name and click the 'Add' button. An OpenVPN server instance with the given name will appear in the "OpenVPN Configuration" list. Only one OpenVPN server instance is allowed to be added. | ||
| Line 258: | Line 287: | ||
<tr> | <tr> | ||
<td>Protocol</td> | <td>Protocol</td> | ||
<td>UDP {{!}} TCP; default: <b>UDP</b></td> | <td>UDP {{!}} TCP{{#ifeq:{{{series}}}|RUTX| {{!}} UDP6 {{!}} TCP6}}; default: <b>UDP</b></td> | ||
<td>Transfer protocol used by the OpenVPN connection. | <td>Transfer protocol used by the OpenVPN connection. | ||
<ul> | <ul> | ||
| Line 273: | Line 302: | ||
<tr> | <tr> | ||
<td>LZO</td> | <td>LZO</td> | ||
<td> | <td>Yes {{!}} No {{!}} None; default: <b>None</b></td> | ||
<td>Turns LZO data compression on or off.</td> | <td>Turns LZO data compression on or off.</td> | ||
</tr> | </tr> | ||
| Line 330: | Line 359: | ||
<tr> | <tr> | ||
<td><span style="color: red;">TLS</span>/<span style="color: #0054a6;">TLS/Password:</span> Client to client</td> | <td><span style="color: red;">TLS</span>/<span style="color: #0054a6;">TLS/Password:</span> Client to client</td> | ||
<td>off {{!}} on; default: <b> | <td>off {{!}} on; default: <b>off</b></td> | ||
<td>Allows OpenVPN clients to communicate with each other on the VPN network.</td> | <td>Allows OpenVPN clients to communicate with each other on the VPN network.</td> | ||
</tr> | </tr> | ||
| Line 355: | Line 384: | ||
<tr> | <tr> | ||
<td><span style="color: red;">TLS</span>/<span style="color: #0054a6;">TLS/Password:</span> Allow duplicate certificates</td> | <td><span style="color: red;">TLS</span>/<span style="color: #0054a6;">TLS/Password:</span> Allow duplicate certificates</td> | ||
<td>off {{!}} on; default: <b> | <td>off {{!}} on; default: <b>off</b></td> | ||
<td>When enabled allows multiple clients to connect using the same certificates.</td> | <td>When enabled allows multiple clients to connect using the same certificates.</td> | ||
</tr> | </tr> | ||
| Line 462: | Line 491: | ||
<b>Generic Routing Encapsulation</b> (<b>GRE</b>) is a tunneling protocol used to establish point-to-point connections between remote private networks. GRE tunnels encapsulate data packets in order to route other protocols over IP networks. | <b>Generic Routing Encapsulation</b> (<b>GRE</b>) is a tunneling protocol used to establish point-to-point connections between remote private networks. GRE tunnels encapsulate data packets in order to route other protocols over IP networks. | ||
===GRE: | ===GRE: Main & Tunnel Settings=== | ||
---- | ---- | ||
To create a new GRE instance, go to the <i>Services → VPN → GRE</i> section, enter a custom name and click the 'Add' button. A GRE instance with the given name will appear in the "GRE Configuration" list. | To create a new GRE instance, go to the <i>Services → VPN → GRE</i> section, enter a custom name and click the 'Add' button. A GRE instance with the given name will appear in the "GRE Configuration" list. | ||
| Line 538: | Line 567: | ||
</table> | </table> | ||
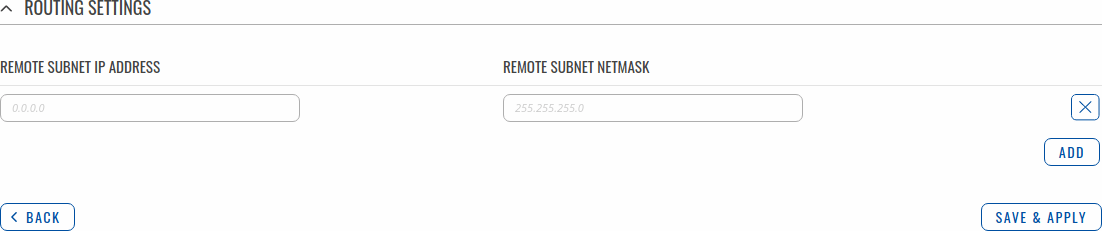
===GRE: | ===GRE: Routing Settings=== | ||
---- | ---- | ||
<b>Routing settings</b> are used to configure routes to networks that are behind the device that hosts the opposite GRE instance. To add a new route, simply click the 'Add' button. For information on configuring the route refer to the figure and table below. | <b>Routing settings</b> are used to configure routes to networks that are behind the device that hosts the opposite GRE instance. To add a new route, simply click the 'Add' button. For information on configuring the route refer to the figure and table below. | ||
| Line 568: | Line 597: | ||
To begin configuration, click the button that looks like a pencil located next to the instance. | To begin configuration, click the button that looks like a pencil located next to the instance. | ||
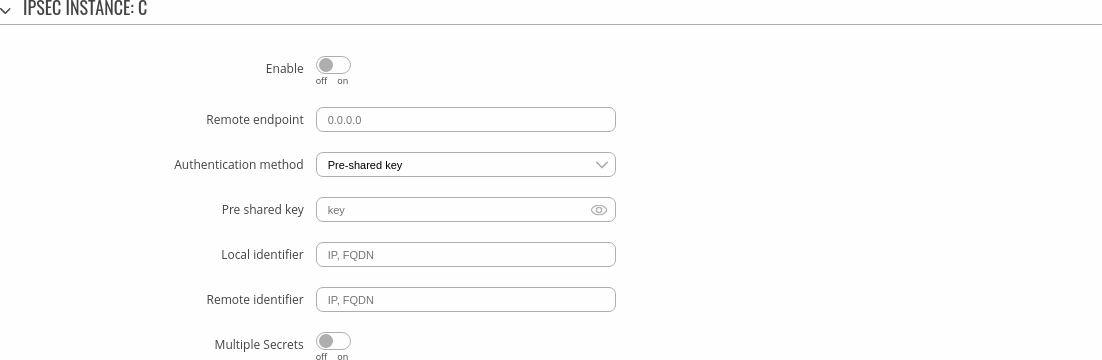
===IPsec | ===IPsec Instance=== | ||
---- | ---- | ||
The <b>general settings</b> section is used to configure the main IPsec parameters. Refer to the figure and table below for information on the configuration fields located in the general settings section. | The <b>general settings</b> section is used to configure the main IPsec parameters. Refer to the figure and table below for information on the configuration fields located in the general settings section. | ||
[[File: | [[File:Networking_rutos_vpn_ipsec_ipsec_instance_general_settings.png|border|class=tlt-border]] | ||
<table class="nd-mantable"> | <table class="nd-mantable"> | ||
| Line 600: | Line 629: | ||
<td>A shared password used for authentication between IPsec peers before a secure channel is established.</td> | <td>A shared password used for authentication between IPsec peers before a secure channel is established.</td> | ||
</tr> | </tr> | ||
<!-- removed on 7.0, to return on 7.1 <tr> | |||
<td><span style="color:darkred">Certificate files from device</span></td> | |||
<td>off {{!}} on; default: <b>off</b></td> | |||
<td>Turn on this option if you want to select generated certificate files from device.</td> | |||
</tr> --> | |||
<tr> | <tr> | ||
<td><span style="color:darkred">X.509:</span> Key</td> | <td><span style="color:darkred">X.509:</span> Key</td> | ||
| Line 634: | Line 668: | ||
</ul> | </ul> | ||
</td> | </td> | ||
</tr> | |||
<tr> | |||
<td>Multiple secrets</td> | |||
<td>off {{!}} on; default: <b>off</b></td> | |||
<td>Enable to show <b>Global Secret Settings</b> section for configuring multiple secrets.</td> | |||
</tr> | </tr> | ||
</table> | </table> | ||
| Line 647: | Line 686: | ||
</ul> | </ul> | ||
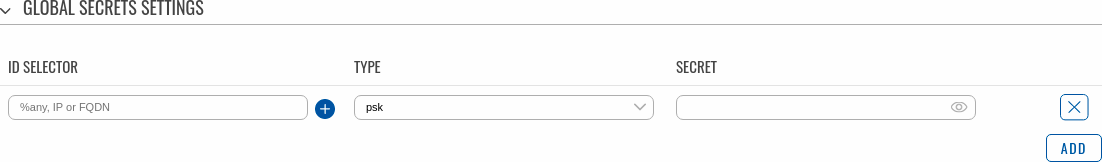
==== | ====Global Secrets Settings==== | ||
---- | ---- | ||
This section is displayed when <b>Multiple secrets</b> is enabled in General settings. You can add new instances by pressing <b>Add</b>. | |||
[[File:Networking_rutos_vpn_ipsec_ipsec_instance_general_settings_global_secrets_settings.png|border|class=tlt-border]] | |||
[[File: | |||
<table class="nd-mantable"> | <table class="nd-mantable"> | ||
| Line 661: | Line 699: | ||
</tr> | </tr> | ||
<tr> | <tr> | ||
<td> | <td>ID Selector</td> | ||
<td>. | <td>%any, IP or FQDN; default: <b>none</b></td> | ||
<td>Each secret can be preceded by a list of optional ID selectors. A selector is an IP address, a Fully Qualified Domain Name, user@FQDN or %any. When using IKEv1 use IP address.</br><b>NOTE:</b> IKEv1 only supports IP address ID selector.</td> | |||
</tr> | |||
<tr> | |||
<td>Type</td> | |||
<td>psk {{!}} xauth; default: <b>psk</b></td> | |||
<td>IPSec secret type.</br><b>NOTE:</b> XAUTH secrets are IKEv1 only.</td> | |||
</tr> | |||
<tr> | |||
<td>Secret</td> | |||
<td>string; default: <b>none</b></td> | |||
<td>A shared password to authenticate between the peers. Minimum length is 5 symbols. All characters are allowed except `.</td> | |||
</tr> | </tr> | ||
</table> | </table> | ||
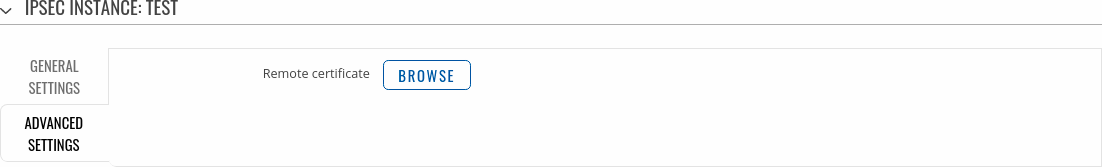
===IPsec | ====Advanced Settings==== | ||
---- | |||
The <b>Advanced settings</b> section is only visible when <b>X.509</b> is selected as Authentication method. | |||
[[File:Networking_rutos_vpn_ipsec_ipsec_instance_advanced_settings.png|border|class=tlt-border]] | |||
<table class="nd-mantable"> | |||
<tr> | |||
<th>Field</th> | |||
<th>Value</th> | |||
<th>Description</th> | |||
</tr> | |||
<!-- removed on 7.0, to return on 7.1 <tr> | |||
<td>Certificate files from device</td> | |||
<td>off | on; default: <b>off</b></td> | |||
<td>Uses certificate file generated on this device instead of uploading. (You can generate certificates within this device via the System → Administration → [[{{{name}}}_Administration#Certificates|Certificates]] page.)</td> | |||
</tr> --> | |||
<tr> | |||
<td>Remote Certificate</td> | |||
<td>.crt file; default: <b>none</b></td> | |||
<td>Selects a certificate file from a computer.</td> | |||
</tr> | |||
</table> | |||
===IPsec Instance: Connection Settings=== | |||
---- | ---- | ||
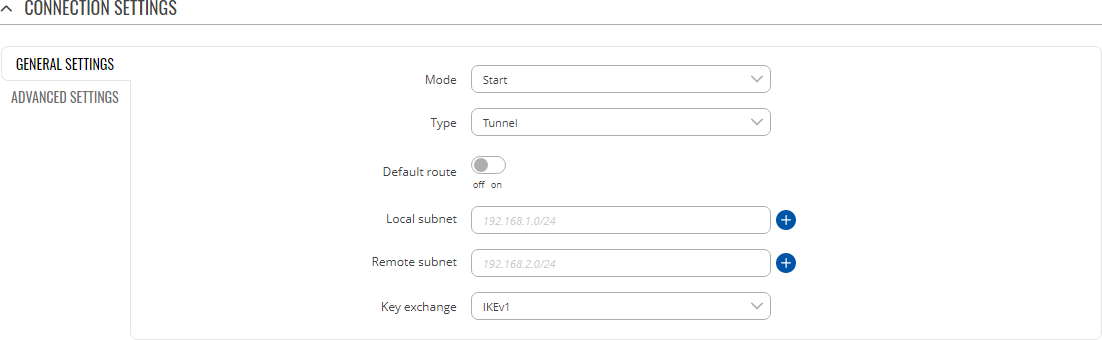
The <b>connection settings</b> section is used to configure the main parameters of an IPsec connection. Refer to the figure and table below for information on the configuration fields located in the connection settings section. | The <b>connection settings</b> section is used to configure the main parameters of an IPsec connection. Refer to the figure and table below for information on the configuration fields located in the connection settings section. | ||
====General | ====General Settings==== | ||
---- | ---- | ||
[[File: | [[File:Networking_rutos_vpn_ipsec_connection_settings_general_settings.png|border|class=tlt-border]] | ||
<table class="nd-mantable"> | <table class="nd-mantable"> | ||
| Line 699: | Line 772: | ||
</tr> | </tr> | ||
<tr> | <tr> | ||
<td><span style="color: red;">Tunnel:</span> Local subnet</td> | <td><span style="color: red;">Tunnel:</span> Default route</td> | ||
<td>ip/netmask {{!}} default: <b>none</b></td> | <td>off {{!}} on; default: <b>off</b></td> | ||
<td>Turn on to route all traffic through IPSec tunnel.</td> | |||
</tr> | |||
<tr> | |||
<td><span style="color: red;">Tunnel:</span> Local subnet</td> | |||
<td>ip/netmask {{!}} default: <b>none</b></td> | |||
<td>Local IP address and subnet mask used to determine which part of the network can be accessed in the VPN network. Netmask range [0..32]. If left empty, IP address will be selected automatically.</td> | <td>Local IP address and subnet mask used to determine which part of the network can be accessed in the VPN network. Netmask range [0..32]. If left empty, IP address will be selected automatically.</td> | ||
</tr> | </tr> | ||
| Line 722: | Line 800: | ||
</ul> | </ul> | ||
</td> | </td> | ||
</tr> | </tr> | ||
</table> | </table> | ||
| Line 743: | Line 816: | ||
---- | ---- | ||
[[File: | [[File:Networking_rutos_vpn_ipsec_connection_settings_advanced_settings.png|border|class=tlt-border]] | ||
<table class="nd-mantable"> | <table class="nd-mantable"> | ||
| Line 754: | Line 827: | ||
<td>Aggressive</td> | <td>Aggressive</td> | ||
<td>off {{!}} on; default: <b>off</b></td> | <td>off {{!}} on; default: <b>off</b></td> | ||
<td>Turn aggressive mode on or off for outgoing connections.</td> | <td>Turn aggressive mode on or off for outgoing connections. Aggressive mode performs fewer exchanges (a total of 4 messages) than Main mode (a total of 6 messages) by storing most data into the first exchange. In aggressive mode, the information is exchanged before there is a secure channel, making it less secure but faster than main mode.<br>Aggressive mode is available only with IKEv1; if IKEv2 is selected this field becomes hidden.</td> | ||
</tr> | </tr> | ||
<tr> | <tr> | ||
| Line 764: | Line 837: | ||
<td>Local firewall</td> | <td>Local firewall</td> | ||
<td>off {{!}} on; default: <b>on</b></td> | <td>off {{!}} on; default: <b>on</b></td> | ||
<td>Adds | <td>Adds necessary firewall rules to allow traffic of this IPsec instance on this device.</td> | ||
</tr> | </tr> | ||
<tr> | <tr> | ||
<td>Remote firewall</td> | <td>Remote firewall</td> | ||
<td>off {{!}} on; default: <b>on</b></td> | <td>off {{!}} on; default: <b>on</b></td> | ||
<td>Adds | <td>Adds necessary firewall rules to allow traffic of from the opposite IPsec instance on this device.</td> | ||
</tr> | </tr> | ||
<tr> | <tr> | ||
| Line 827: | Line 900: | ||
</tr> | </tr> | ||
<tr> | <tr> | ||
<td><span style="color: red;">Tunnel:</span> Passthrough</td> | <td><span style="color: red;">Tunnel:</span> Passthrough interfaces</td> | ||
<td> | <td>network interfaces; default: <b>none</b></td> | ||
<td> | <td>Network interfaces to include in IPsec Passthrough.</td> | ||
</tr> | |||
<tr> | |||
<td><span style="color: red;">Tunnel:</span> Passthrough subnets</td> | |||
<td>ip/netmask; default: <b>none</b></td> | |||
<td>Networks to include in IPsec Passthrough.</td> | |||
</tr> | </tr> | ||
</table> | </table> | ||
| Line 989: | Line 1,067: | ||
===PPTP client=== | ===PPTP client=== | ||
---- | ---- | ||
A <b>PPTP client</b> is an entity that initiates a connection to a PPTP server. To create a new client instance, go to the <i>Services → VPN → PPTP</i> section, select <i>Role: Client</i>, enter a custom name and click the 'Add' button | A <b>PPTP client</b> is an entity that initiates a connection to a PPTP server. To create a new client instance, go to the <i>Services → VPN → PPTP</i> section, select <i>Role: Client</i>, enter a custom name and click the 'Add' button: | ||
[[File:Networking_rutos_vpn_pptp_client_add_button.png|border|class=tlt-border]] | |||
[[File: | You should be redirected to the configuration page for the newly added PPTP Client which should look similar to this: | ||
[[File:Networking_rutos_vpn_pptp_client.png|border|class=tlt-border]] | |||
<table class="nd-mantable"> | <table class="nd-mantable"> | ||
| Line 1,029: | Line 1,109: | ||
===PPTP server=== | ===PPTP server=== | ||
---- | ---- | ||
A <b>PPTP server</b> is an entity that waits for incoming connections from PPTP clients. To create a new server instance, go to the <i>Services → VPN → PPTP</i> section, select <i>Role: Server</i>, enter a custom name and click the 'Add' button | A <b>PPTP server</b> is an entity that waits for incoming connections from PPTP clients. To create a new server instance, go to the <i>Services → VPN → PPTP</i> section, select <i>Role: Server</i>, enter a custom name and click the 'Add' button: | ||
[[File:Networking_rutos_vpn_pptp_server_add_button.png|border|class=tlt-border]] | |||
You should be redirected to the configuration page for the newly added PPTP Server which should look similar to this: | |||
[[File: | [[File:Networking_rutos_vpn_pptp_server.png|border|class=tlt-border]] | ||
<table class="nd-mantable"> | <table class="nd-mantable"> | ||
| Line 1,064: | Line 1,144: | ||
</tr> | </tr> | ||
<tr> | <tr> | ||
<td> | <td>Timeout</td> | ||
<td> | <td>integer; default: <b>none</b></td> | ||
<td> | <td>Time in seconds. If no packets pass through the tunnel between this server and a client, the server will terminate the connection to that client after the amount of time specified in this field passes.</td> | ||
</tr> | </tr> | ||
<tr> | <tr> | ||
<td> | <td>Primary DNS</td> | ||
<td> | <td>ip; default: <b>none</b></td> | ||
<td> | <td>IP address of the primary DNS server.</td> | ||
</tr> | </tr> | ||
<tr> | <tr> | ||
<td> | <td>Secondary DNS</td> | ||
<td>ip; default: <b>none</b></td> | <td>ip; default: <b>none</b></td> | ||
<td> | <td>IP address of the secondary DNS server.</td> | ||
</tr> | </tr> | ||
</table> | </table> | ||
---- | |||
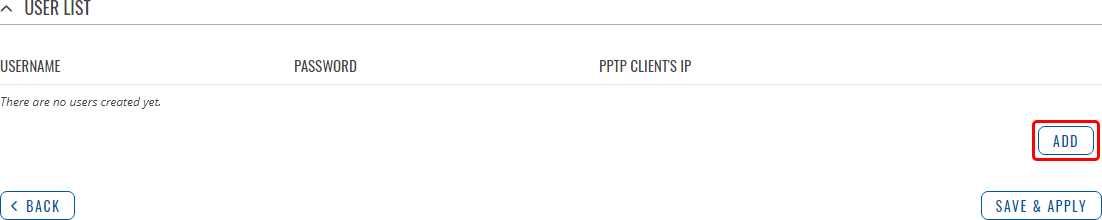
The <b>User List</b> section is used to user authentication settings required to successfully connect to this server. The list is empty by default. Click the 'Add' button to create a new PPTP User: | |||
[[File:Networking_rutos_vpn_pptp_server_user_list_add_button.png|border|class=tlt-border]] | |||
[[File:Networking_rutos_vpn_pptp_server_user_list.png|border|class=tlt-border]] | |||
<table class="nd-mantable"> | |||
<tr> | |||
<th>Field</th> | |||
<th>Value</th> | |||
<th>Description</th> | |||
</tr> | |||
<tr> | |||
<td>Username</td> | |||
<td>string; default: <b>none</b></td> | |||
<td>Username used for authentication to this PPTP server.</td> | |||
</tr> | |||
<tr> | |||
<td>Password</td> | |||
<td>string; default: <b>none</b></td> | |||
<td>Password used for authentication to this PPTP server.</td> | |||
</tr> | |||
<tr> | |||
<td>PPTP Client's IP</td> | |||
<td>ip; default: <b>none</b></td> | |||
<td>Assigns an IP address to the client that uses the adjacent authentication info. This field is optional and if left empty the client will simply receive an IP address from the IP pool defined above.</td> | |||
</tr> | |||
</table> | |||
<b>Note:</b> there can only one PPTP Server configuration on the device. | |||
==SSTP== | |||
<b>Secure Socket Tunneling Protocol</b> (SSTP) is a VPN protocol designed to transport PPP traffic via a secure SSL/TLS channel. | |||
{{#ifeq: TRB1 | RUTX | | | |||
</br><u><b>Note:</b> SSTP is additional software that can be installed from the <b>Services → [[{{{name}}} Package Manager|Package Manager]]</b> page.</u> | |||
}} | |||
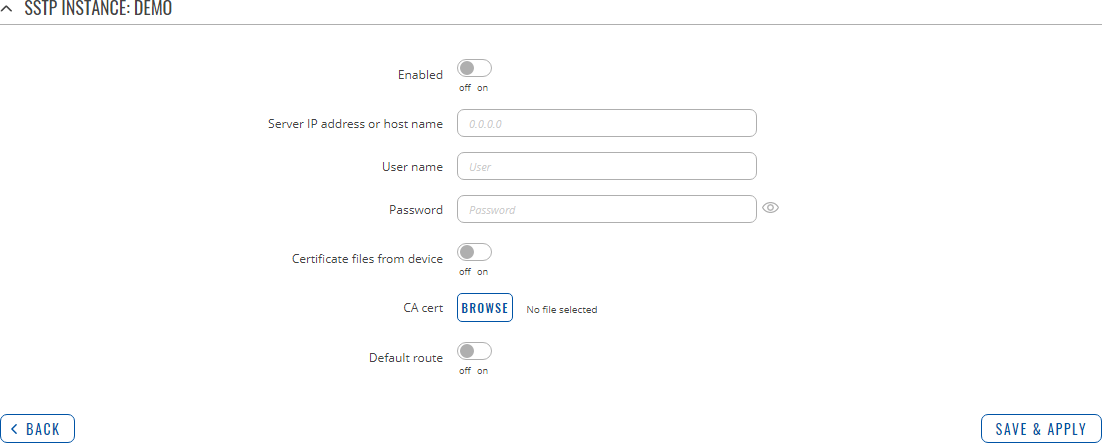
===SSTP configuration=== | ===SSTP configuration=== | ||
---- | ---- | ||
| Line 1,094: | Line 1,206: | ||
Refer to the figure and table below for information on the SSTP instance's configuration fields: | Refer to the figure and table below for information on the SSTP instance's configuration fields: | ||
[[File: | [[File:Networking_rutos_manual_vpn_sstp_sstp_instance.png|border|class=tlt-border]] | ||
<table class="nd-mantable"> | <table class="nd-mantable"> | ||
| Line 1,121: | Line 1,233: | ||
<td>string; default: <b>none</b></td> | <td>string; default: <b>none</b></td> | ||
<td>Password used for authentication to the SSTP server.</td> | <td>Password used for authentication to the SSTP server.</td> | ||
</tr> | |||
<tr> | |||
<td>Certificate files from device</td> | |||
<td>off {{!}} on; default: <b>off</b></td> | |||
<td>Turn on this option if you want to select generated certificate files from device.</td> | |||
</tr> | </tr> | ||
<tr> | <tr> | ||
| Line 1,145: | Line 1,262: | ||
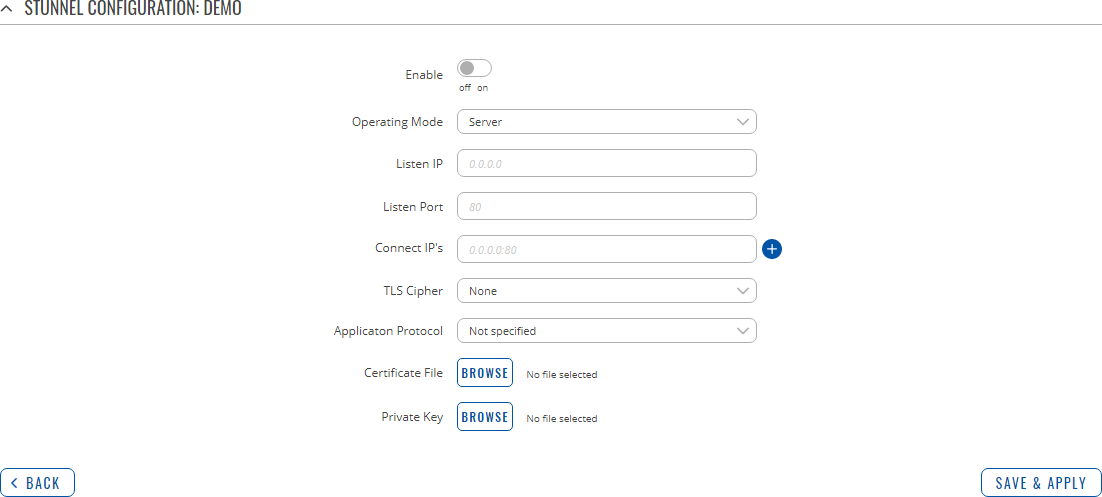
The Stunnel Globals section is used to manage the Stunnel service as a whole. | The Stunnel Globals section is used to manage the Stunnel service as a whole. | ||
Refer to the figure and table below for information on the fields contained in the Stunnel Globals section. | Refer to the figure and table below for information on the fields contained in the Stunnel Globals section. | ||
{{#ifeq: {{{series}}} | RUTX | | | |||
[[File: | </br><u><b>Note:</b> Stunnel is additional software that can be installed from the <b>Services → [[{{{name}}} Package Manager|Package Manager]]</b> page.</u> | ||
}} | |||
[[File:Networking_rutos_manual_vpn_stunnel_globals.png|border|class=tlt-border]] | |||
<table class="nd-mantable"> | <table class="nd-mantable"> | ||
| Line 1,176: | Line 1,295: | ||
<tr> | <tr> | ||
<td>Use alternative config</td> | <td>Use alternative config</td> | ||
<td>off {{!}} on; default: <b> | <td>off {{!}} on; default: <b>off</b></td> | ||
<td>Turns the possibility to upload an external Stunnel configuration file on or off.if you turn this on, other Stunnel configurations present in the router will become inactive.</td> | <td>Turns the possibility to upload an external Stunnel configuration file on or off.if you turn this on, other Stunnel configurations present in the router will become inactive.</td> | ||
</tr> | </tr> | ||
| Line 1,194: | Line 1,313: | ||
Refer to the figure and table below for information on the Stunnel instance's configuration fields: | Refer to the figure and table below for information on the Stunnel instance's configuration fields: | ||
[[File: | [[File:Networking_rutos_manual_vpn_stunnel_configuration.png|border|class=tlt-border]] | ||
<table class="nd-mantable"> | <table class="nd-mantable"> | ||
| Line 1,285: | Line 1,404: | ||
<b>Dynamic Multipoint VPN</b> (<b>DMVPN</b>) is a method of building scalable IPsec VPNs. DMVPN is configured as a hub-and-spoke network, where tunnels between spokes are built dynamically; therefore, no change in configuration is required on the hub in order to connect new spokes. | <b>Dynamic Multipoint VPN</b> (<b>DMVPN</b>) is a method of building scalable IPsec VPNs. DMVPN is configured as a hub-and-spoke network, where tunnels between spokes are built dynamically; therefore, no change in configuration is required on the hub in order to connect new spokes. | ||
{{#ifeq: {{{series}}} | RUTX | | | |||
</br><u><b>Note:</b> DMPVN is additional software that can be installed from the <b>Services → [[{{{name}}} Package Manager|Package Manager]]</b> page.</u> | |||
}} | |||
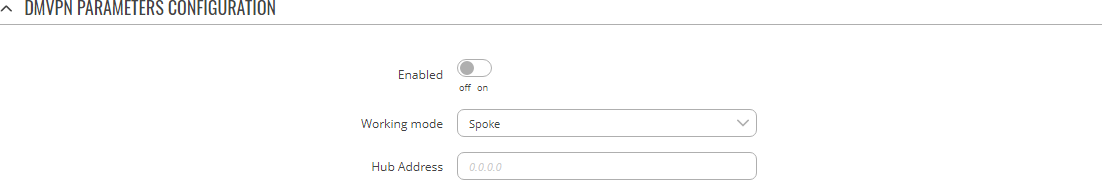
===DMVPN configuration=== | ===DMVPN configuration=== | ||
---- | ---- | ||
| Line 1,292: | Line 1,413: | ||
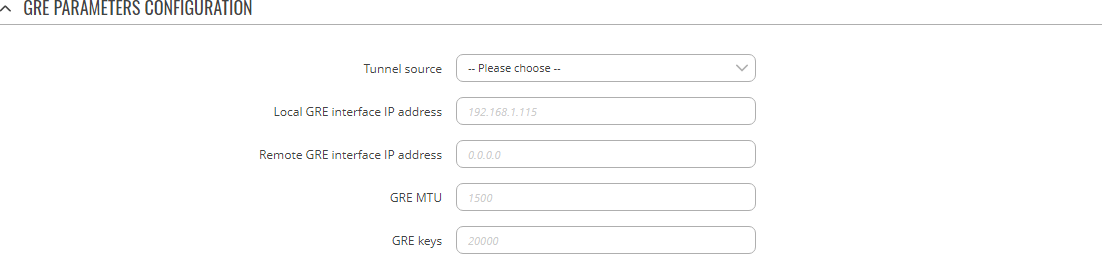
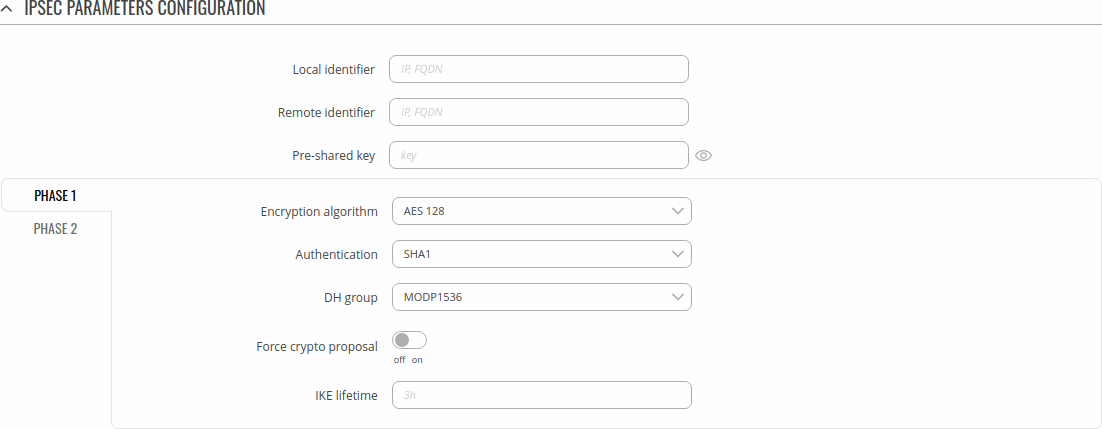
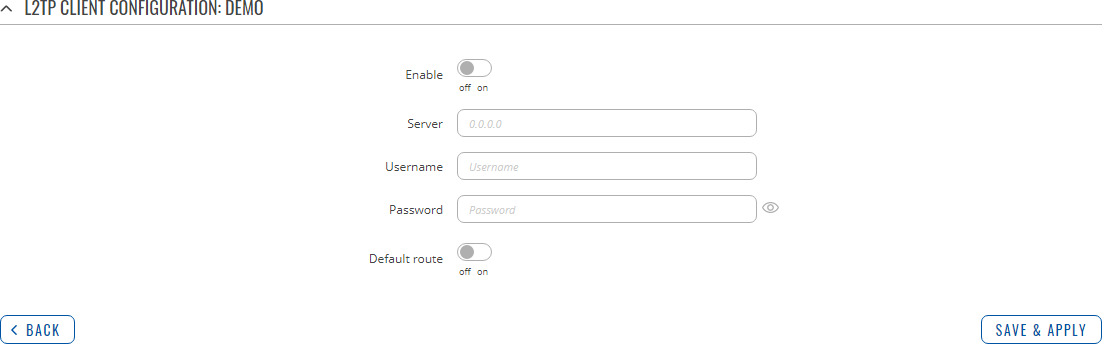
To begin configuration, click the button that looks like a pencil located next to the instance. Refer to the figures and tables below for information on the DMVPN instance configuration: | To begin configuration, click the button that looks like a pencil located next to the instance. Refer to the figures and tables below for information on the DMVPN instance configuration: | ||
[[File: | [[File:Networking_rutos_manual_vpn_dmvpn_dmvpn_parameters_configuration.png|border|class=tlt-border]] | ||
<table class="nd-mantable"> | <table class="nd-mantable"> | ||
| Line 1,323: | Line 1,444: | ||
<br> | <br> | ||
---- | ---- | ||
[[File: | [[File:Networking_rutos_manual_vpn_dmvpn_gre_parameters_configuration.png|border|class=tlt-border]] | ||
<table class="nd-mantable"> | <table class="nd-mantable"> | ||
| Line 1,448: | Line 1,569: | ||
</tr> | </tr> | ||
</table> | </table> | ||
==L2TP== | ==L2TP== | ||
| Line 1,461: | Line 1,580: | ||
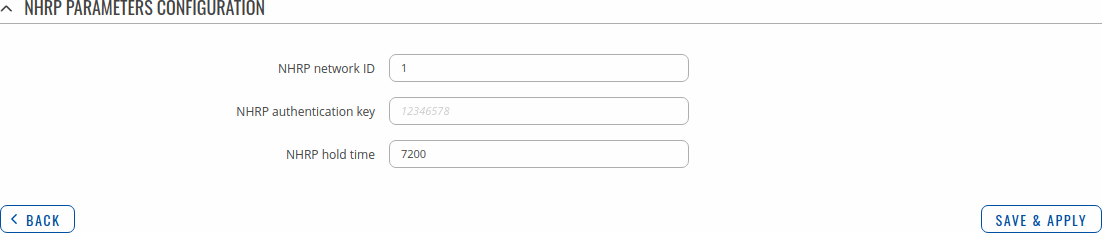
To begin configuration, click the button that looks like a pencil next to the client instance. Refer to the figure and table below for information on the L2TP client's configuration fields: | To begin configuration, click the button that looks like a pencil next to the client instance. Refer to the figure and table below for information on the L2TP client's configuration fields: | ||
[[File: | [[File:Networking_rutos_manual_vpn_l2tp_client.png|border|class=tlt-border]] | ||
<table class="nd-mantable"> | <table class="nd-mantable"> | ||
| Line 1,546: | Line 1,665: | ||
<td>ip; default: <b>none</b></td> | <td>ip; default: <b>none</b></td> | ||
<td>Assigns an IP address to the client that uses the adjacent authentication info. This field is optional and if left empty the client will simply receive an IP address from the IP pool defined above.</td> | <td>Assigns an IP address to the client that uses the adjacent authentication info. This field is optional and if left empty the client will simply receive an IP address from the IP pool defined above.</td> | ||
</tr> | |||
</table> | |||
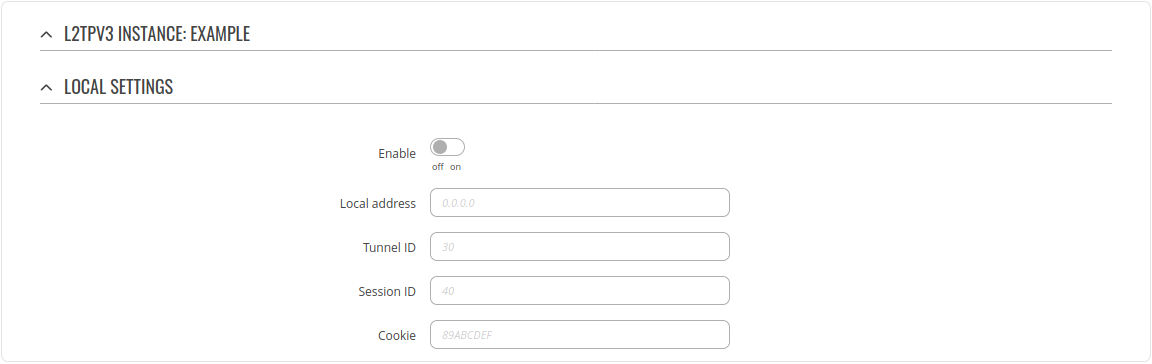
==L2TPv3== | |||
L2TPv3 (Layer Two Tunneling Protocol Version 3) is a point-to-point layer two over IP tunnel. This means you can tunnel L2 protocols like Ethernet, Frame-relay, ATM, HDLC, PPP, etc. over an IP network. | |||
===Local settings=== | |||
---- | |||
[[File:Networking_rutos_vpn_l2tpv3_configuration_local_settings_v1.png]] | |||
<table class="nd-mantable"> | |||
<tr> | |||
<th>Field</th> | |||
<th>Value</th> | |||
<th>Description</th> | |||
</tr> | |||
<tr> | |||
<td>Enable</td> | |||
<td>off {{!}} on; default: <b>off</b></td> | |||
<td>Turns the L2TPv3 instance on or off.</td> | |||
</tr> | |||
<tr> | |||
<td>Local address</td> | |||
<td>ip; default: <b>none</b></td> | |||
<td>IP address of device's WAN. Note: If left empty, it will take IP address automatically from main WAN interface. <td> | |||
</tr> | |||
<tr> | |||
<td>Tunnel ID</td> | |||
<td>integer [1..4294967295]; default: <b>none</b></td> | |||
<td>Uniquely identifies the tunnel. The value used must match the peer tunnel ID value being used at the peer.</td> | |||
</tr> | |||
<tr> | |||
<td>Session ID</td> | |||
<td>integer [1..4294967295]; default: <b>none</b></td> | |||
<td>The value used must match the tunnel ID value being used at the peer.</td> | |||
</tr> | |||
<tr> | |||
<td>Cookie</td> | |||
<td>string; default: <b>none</b></td> | |||
<td>Must be specified in hexidecimal form and be length of 8 or 16. eg.: 89ABCDEF.</td> | |||
</tr> | |||
</table> | |||
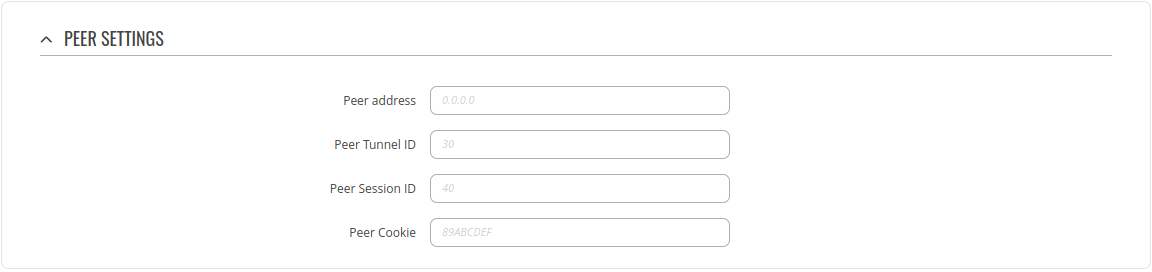
===Peer settings=== | |||
---- | |||
[[File:Networking_rutos_vpn_l2tpv3_configuration_peer_settings_v1.png]] | |||
<table class="nd-mantable"> | |||
<tr> | |||
<th>Field</th> | |||
<th>Value</th> | |||
<th>Description</th> | |||
</tr> | |||
<tr> | |||
<td>Peer address</td> | |||
<td>ip; default: <b>none</b></td> | |||
<td>Peer Endpoint IP address.</td> | |||
</tr> | |||
<tr> | |||
<td>Peer Tunnel ID</td> | |||
<td>integer [1..4294967295]; default: <b>none</b></td> | |||
<td>ID of peer's tunnel is specified from 1 to 4294967295. It must match other end tunnel ID.<td> | |||
</tr> | |||
<tr> | |||
<td>Peer Session ID</td> | |||
<td>integer [1..4294967295]; default: <b>none</b></td> | |||
<td>UID of peer's session is specified from 1 to 4294967295. It must match other end session ID. </td> | |||
</tr> | |||
<tr> | |||
<td>Peer Cookie</td> | |||
<td>string; default: <b>none</b></td> | |||
<td>Must be specified in hexidecimal form and be length of 8 or 16. eg.: 89ABCDEF. It must match other end Cookie.</td> | |||
</tr> | |||
</table> | |||
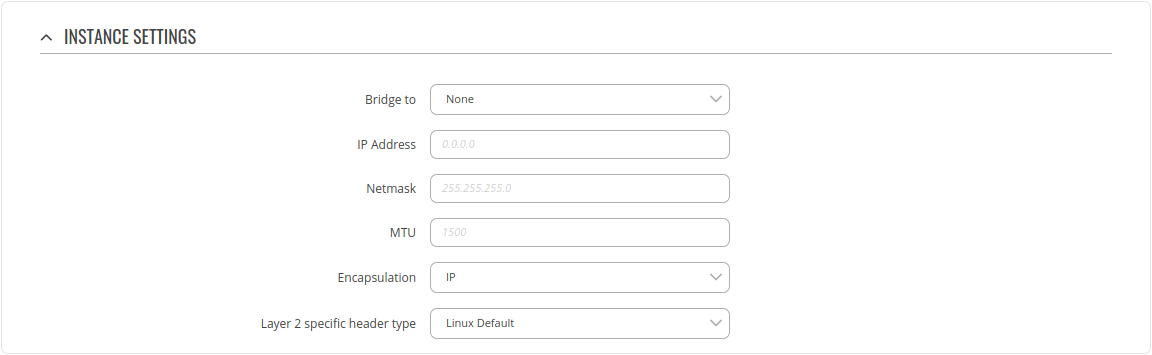
===Instance Settings=== | |||
---- | |||
[[File:Networking_rutos_vpn_l2tpv3_configuration_instance_settings_v1.png]] | |||
<table class="nd-mantable"> | |||
<tr> | |||
<th>Field</th> | |||
<th>Value</th> | |||
<th>Description</th> | |||
</tr> | |||
<tr> | |||
<td>Bridge to</td> | |||
<td>None {{!}} LAN; default: <b>None</b></td> | |||
<td>Peer Endpoint IP address.</td> | |||
</tr> | |||
<tr> | |||
<td>IP Address</td> | |||
<td>ip; default: <b>none</b></td> | |||
<td>IP address of standalone L2TPv3 interface.<td> | |||
</tr> | |||
<tr> | |||
<td>Netmask</td> | |||
<td>netmask; default: <b>none</b></td> | |||
<td>Netmask of standalone L2TPv3 interface. </td> | |||
</tr> | |||
<tr> | |||
<td>MTU</td> | |||
<td>integer [64..9000]; default: <b>none</b></td> | |||
<td>Sets the maximum transmission unit (MTU) size. It is the largest size of a protocol data unit (PDU) that can be transmitted in a single network layer transaction.</td> | |||
</tr> | |||
<tr> | |||
<td>Encapsulation</td> | |||
<td>IP {{!}} UDP; default: <b>IP</b></td> | |||
<td>Specify technology to use when connecting to other end.</td> | |||
</tr> | |||
<tr> | |||
<td>Layer 2 specific header type</td> | |||
<td>None {{!}} Linux Default; default: <b>Linux Default</b></td> | |||
<td>It might be neccessary to set this option to none when using other hardware.</td> | |||
</tr> | |||
</table> | |||
==ZeroTier== | |||
<b>ZeroTier One</b> is an open source software which can establish Peer to Peer VPN (P2PVPN) connection between various devices running various operating systems. It also provides network management possibilities such as routing and creating firewall rules. | |||
<u><b>Note:</b> ZeroTier is additional software that can be installed from the <b>Services → [[{{{name}}} Package Manager|Package Manager]]</b> page.</u> | |||
---- | |||
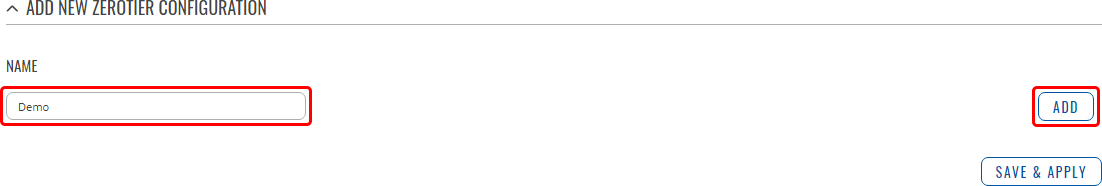
In order to create a new ZeroTier Instance, look to the Add New ZeroTier Configuration section; enter a custom name and click the 'Add' button: | |||
[[File:Networking_rutos_manual_vpn_zerotier_add_button.png|border|class=tlt-border]] | |||
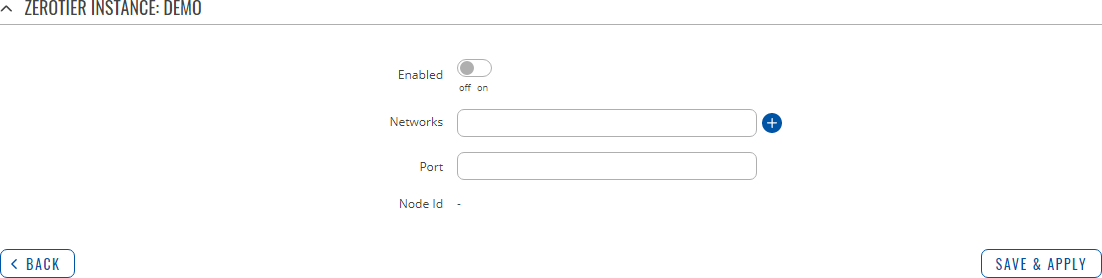
You should be redirected to the configuration page for the newly added ZeroTier Instance which should look similar to this: | |||
[[File:Networking_rutos_manual_vpn_zerotier_instance.png|border|class=tlt-border]] | |||
<table class="nd-mantable"> | |||
<tr> | |||
<th>Field</th> | |||
<th>Value</th> | |||
<th>Description</th> | |||
</tr> | |||
<tr> | |||
<td>Enabled</td> | |||
<td>off {{!}} on; default: <b>off</b></td> | |||
<td>Turns the ZeroTier Instance on or off.</td> | |||
</tr> | |||
<tr> | |||
<td>Networks/td> | |||
<td>hex string; default: <b>none</b></td> | |||
<td>ZeroTier Network ID. Log in to your ZeroTier account in order to locate the ZeroTier Network ID, which should be a string of hexadecimal characters.</td> | |||
</tr> | |||
<tr> | |||
<td>Port/td> | |||
<td>integer [0..65535]; default: <b>none</b></td> | |||
<td>ZeroTier Network port.</td> | |||
</tr> | |||
</table> | |||
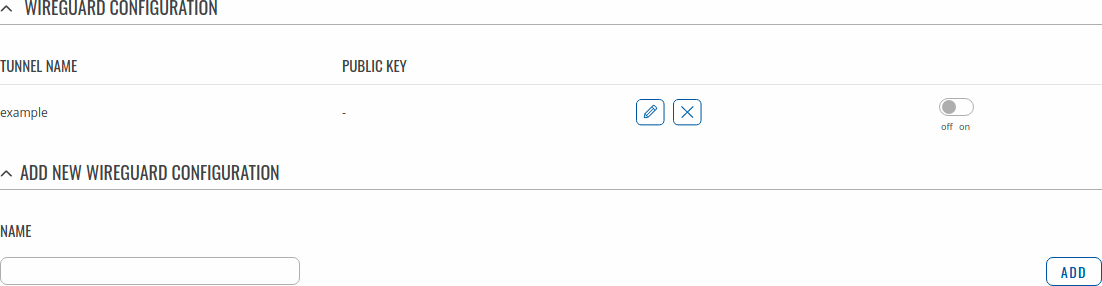
==WireGuard== | |||
'''WireGuard''' is simple, fast, lean, and modern VPN that utilizes secure and trusted cryptography. | |||
It intends to be more performant than OpenVPN. WireGuard is designed as general purpose VPN, fit for | |||
many different circumstances and while it is currently under heavy development, it already | |||
might be regarded as the most secure, easiest to use, and simplest VPN solution. | |||
<u><b>Note:</b> WireGuard is additional software that can be installed from the <b>Services → [[{{{name}}} Package Manager|Package Manager]]</b> page.</u> | |||
WireGuard works by adding an interface which acts as a tunnel. To create one enter its name and click the <b>Add</b> button. | |||
To configure it click the <b>Edit</b> [[File:Networking_rutx_manual_edit_button_v1.png]] button. | |||
[[File:Networking_rutx_vpn_wireguard_v1.png|border|class=tlt-border]] | |||
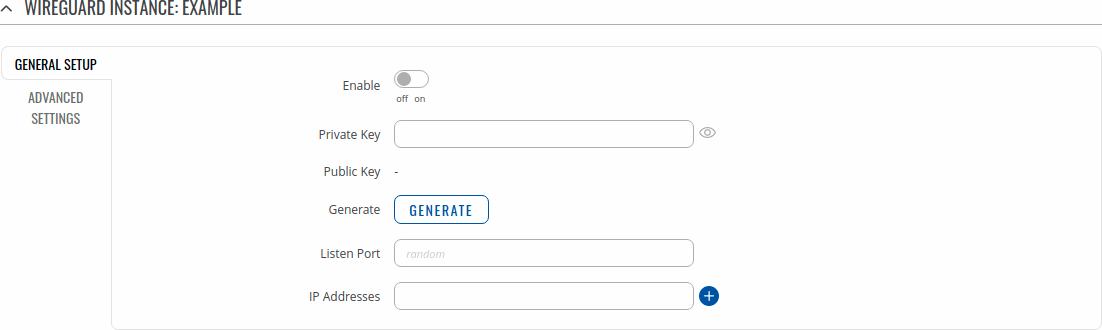
===General Instance Settings=== | |||
---- | |||
This section contains General settings of created WireGuard Instance. Here you can find its Public and | |||
Private keys and generate them, specify Port and IP addresses for communication. | |||
[[File:Networking_rutx_vpn_wireguard_instance_general_v1.png|border|class=tlt-border]] | |||
<table class="nd-mantable"> | |||
<tr> | |||
<th>Field</th> | |||
<th>Value</th> | |||
<th>Description</th> | |||
</tr> | |||
<tr> | |||
<td>Enable</td> | |||
<td>off | on; default: <b>off</b></td> | |||
<td>Turns WireGuard Instance on or off.</td> | |||
</tr> | |||
<tr> | |||
<td>Private Key</td> | |||
<td>string; default: <b>none</b></td> | |||
<td>Private Key used in authentication.</td> | |||
</tr> | |||
<tr> | |||
<td>Public Key</td> | |||
<td>string; default: <b>-</b></td> | |||
<td>Public Key used in authentication.</td> | |||
</tr> | |||
<tr> | |||
<td>Generate</td> | |||
<td>-(interactive button)</td> | |||
<td>Click to generate Public Key and Private Key.</td> | |||
</tr> | |||
<tr> | |||
<td>Listen Port</td> | |||
<td>integer [0..65535]; default: <b>none</b></td> | |||
<td>Specify port to listen for incomming connections. It will be set to a random integer if left empty.</td> | |||
</tr> | |||
<tr> | |||
<td>IP Addresses</td> | |||
<td>ip; default: <b>none</b></td> | |||
<td>A single IP address or a list of them for this instance associated with public keys.</td> | |||
</tr> | |||
</table> | |||
====Advanced Settings==== | |||
---- | |||
Advanced Settings section contains Metric and MTU configuration for this WireGuard interface. | |||
[[File:Networking_rutx_vpn_wireguard_instance_advanced_v1.png|border|class=tlt-border]] | |||
<table class="nd-mantable"> | |||
<tr> | |||
<th>Field</th> | |||
<th>Value</th> | |||
<th>Description</th> | |||
</tr> | |||
<tr> | |||
<td>Metric</td> | |||
<td>positive integer; default: <b>none</b></td> | |||
<td>Specify metric for this tunnel interface. Lower number means higher priority.</td> | |||
</tr> | |||
<tr> | |||
<td>MTU</td> | |||
<td>integer [1280..1420]; default: <b>none</b></td> | |||
<td>Maximum Transmission Unit for this tunnel interface.</td> | |||
</tr> | |||
</table> | |||
===Peers=== | |||
---- | |||
The Peers section is used to create and configure all the peers for this interface. | |||
To create one enter its name and click the <b>Add</b> button. | |||
To configure it click the <b>Edit</b> [[File:Networking_rutx_manual_edit_button_v1.png]] button. | |||
[[File:Networking_rutx_vpn_wireguard_instance_peer_v2.png|border|class=tlt-border]] | |||
====General Peer Settings==== | |||
---- | |||
In the General section of Peer instance you can configure basic information about the endpoint to allow communications. | |||
[[File:Networking_rutx_vpn_wireguard_instance_peer_instance_general_v1.png|border|class=tlt-border]] | |||
<table class="nd-mantable"> | |||
<tr> | |||
<th>Field</th> | |||
<th>Value</th> | |||
<th>Description</th> | |||
</tr> | |||
<tr> | |||
<td>Public Key</td> | |||
<td>string; default: <b>none</b></td> | |||
<td>Endpoint's Public Key.</td> | |||
</tr> | |||
<tr> | |||
<td>Allowed IPs</td> | |||
<td>ip; default: <b>none</b></td> | |||
<td>A single IP address or a list of them which are allowed to communicate with this peer.</td> | |||
</tr> | |||
</table> | |||
====Advanced Peer Settings==== | |||
---- | |||
In the Advanced section of Peer instance you are able to configure additional | |||
settings such as its Description, Endpoint Host and Port, Preshared Key and other. | |||
See more information below. | |||
[[File:Networking_rutx_vpn_wireguard_instance_peer_instance_advanced_v1.png|border|class=tlt-border]] | |||
<table class="nd-mantable"> | |||
<tr> | |||
<th>Field</th> | |||
<th>Value</th> | |||
<th>Description</th> | |||
</tr> | |||
<tr> | |||
<td>Description</td> | |||
<td>string; default: <b>none</b></td> | |||
<td>Description of this peer.</td> | |||
</tr> | |||
<tr> | |||
<td>Pre-Shared Key</td> | |||
<td>string; default: <b>none</b></td> | |||
<td>Base64-encoded preshared key. Adds in an additional layer of symmetric-key cryptography for post-quantum resistance.</td> | |||
</tr> | |||
<tr> | |||
<td>Route Allowed IPs</td> | |||
<td>off {{!}} on; default: <b>off</b></td> | |||
<td>Enable to create routes for <b>Allowed IPs</b> for this peer.</td> | |||
</tr> | |||
<tr> | |||
<td>Endpoint Host</td> | |||
<td>ip {{!}} url; default: <b>none</b></td> | |||
<td>IP or URL of Remote Endpoint.</td> | |||
</tr> | |||
<tr> | |||
<td>Endpoint Port</td> | |||
<td>integer [0..65535]; default: <b>none</b></td> | |||
<td>Specify port to connect to Remote Endpoint. It will be set to <b>51820</b> if left empty.</td> | |||
</tr> | |||
<tr> | |||
<td>Persistent Keep Alive</td> | |||
<td>integer [0..65535]; default: <b>none</b></td> | |||
<td>Specify time amount in seconds between Keep Alive messages. By default this option is <b>0</b> which means it is disabled. Recommended value for a device behind NAT is 25.</td> | |||
</tr> | </tr> | ||
</table> | </table> | ||
[[Category:{{{name}}} Services section]] | [[Category:{{{name}}} Services section]] | ||
Revision as of 14:11, 8 September 2021
Template:Networking rutos manual fw disclosure
Summary
Virtual Private Network (VPN) is a method of connecting multiple private networks across the Internet. VPNs can serve to achieve many different goals, but some of its main purposes are:
- access between remote private networks;
- data encryption;
- anonymity when browsing the Internet.
This page is an overview of the different types of VPNs supported by {{{name}}} devices.
OpenVPN
OpenVPN is an open-source software application that implements virtual private network (VPN) techniques for creating secure point-to-point or site-to-site connections in routed or bridged configurations and remote access facilities. It is often regarded as being the most universal VPN protocol because of its flexibility, support of SSL/TLS security, multiple encryption methods, many networking features and compatibility with most OS platforms.
{{{name}}} devices run OpenVPN version 2.5.2.
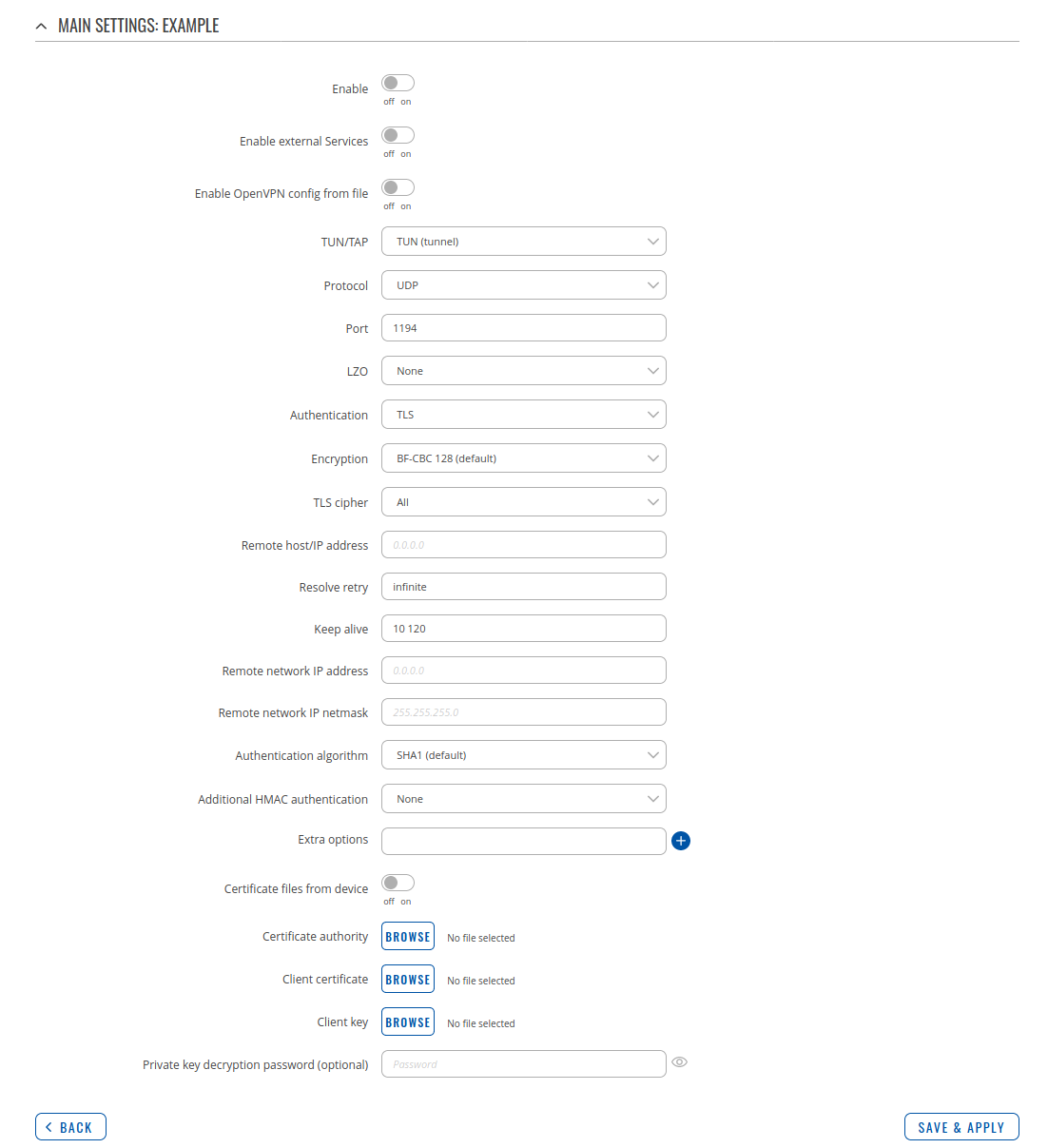
OpenVPN Client
An OpenVPN client is an entity that initiates a connection to an OpenVPN server. To create a new client instance, go to the Services → VPN → OpenVPN section, select Role: Client, enter a custom name and click the 'Add' button. An OpenVPN client instance with the given name will appear in the "OpenVPN Configuration" list.
To begin configuration, click the button that looks like a pencil next to the client instance. Refer to the figure and table below for information on the OpenVPN client's configuration fields:
| Field | Value | Description |
|---|---|---|
| Enable | off | on; default: off | Turns the OpenVPN instance on or off. |
| Enable external Services | off | on; default: off | Turns the OpenVPN external Services on or off. |
| VPN providers | Express VPN | Nord VPN; default: Nord VPN | Represents a list of available VPN providers. |
| VPN servers | United Kingdom | USA | Australia | South Africa | Custom; default: United Kingdom | Represents a list of available VPN servers. |
| Enable OpenVPN config from file | off | on; default: off | Enables or disables custom OpenVPN config from file. |
| Username | string; default: none | Username used for authentication to the VPN server. |
| Password | string; default: none | Password used for authentication to the VPN server. |
| TUN/TAP | TUN (tunnel) | TAP (bridged); default: TUN (tunnel) | Virtual network device type.
|
| Protocol | UDP | TCP; default: UDP | Transfer protocol used by the OpenVPN connection.
|
| Port | integer [0..65535]; default: 1194 | TCP/UDP port number used for the connection. Make sure it matches the port number specified on the server side. NOTE: traffic on the selected port will be automatically allowed in the device firewall rules. |
| LZO | Yes | No | None; default: None | Turns LZO data compression on or off. |
| Encryption | DES-CBC 64 | RC2-CBC 128 | DES-EDE-CBC 128 | DES-EDE3-CBC 192 | DESX-CBC 192 | BF-CBC 128 | RC2-40-CBC 40 | CAST5-CBC 128 | RC2-40CBC 40 | CAST5-CBC 128 | RC2-64-CBC 64| AES-128-CBC 128 | AES-192-CBC 192 | AES-256-CBC 256 | none; default: BF-CBC 128 | Algorithm used for packet encryption. |
| Authentication | TLS | Static Key | Password | TLS/Password; default: TLS | Authentication mode, used to secure data sessions.
|
| TLS: TLS cipher | All | DHE+RSA | Custom; default: All | Packet encryption algorithm cipher. |
| TLS: Allowed TLS ciphers | All | DHE+RSA | Custom; default: All | A list of TLS ciphers accepted by this connection. |
| Remote host/IP address | ip; default: none | IP address or hostname of an OpenVPN server. |
| Resolve retry | integer | infinite; default: infinite | In case server hostname resolve fails, this field indicates the amount of time (in seconds) to retry the resolve. Specify infinite to retry indefinitely. |
| Keep alive | two integers separated by a space; default: none | Defines two time intervals: the first is used to periodically send ICMP requests to the OpenVPN server, the second one defines a time window, which is used to restart the OpenVPN service if no ICMP response is received during the specified time slice. When this value is specfiied on the OpenVPN server, it overrides the 'keep alive' values set on client instances. Example: 10 120 |
| Static key: Local tunnel endpoint IP | ip; default: none | IP address of the local OpenVPN network interface. |
| Static key: Remote tunnel endpoint IP | ip; default: none | IP address of the remote OpenVPN network (server) interface. |
| Remote network IP address | ip; default: none | LAN IP address of the remote network (server). |
| Remote network IP netmask | netmask; default: none | LAN IP subnet mask of the remote network (server). |
| Password: User name | string; default: none | Username used for authentication to the OpenVPN server. |
| Password: Password | string; default: none | Password used for authentication to the OpenVPN server. |
| Extra options | string; default: none | Extra OpenVPN options to be used by the OpenVPN instance. |
| Certificate files from device | off | on; default: off | Turn on this option if you want to select generated certificate files from device. |
| TLS/Password: HMAC authentication algorithm | none | SHA1 | SHA256 | SHA384 | SHA512; default: SHA1 | HMAC authentication algorithm type. |
| TLS/Password: Additional HMAC authentication | off | on; default: off | An additional layer of HMAC authentication on top of the TLS control channel to protect against DoS attacks. |
| TLS/Password: HMAC authentication key | .key file; default: none | Uploads an HMAC authentication key file. |
| TLS/Password: HMAC key direction | 0 | 1 | none; default: 1 | The value of the key direction parameter should be complementary on either side (client and server) of the connection. If one side uses 0, the other side should use 1, or both sides should omit the parameter altogether. |
| TLS/Password: Certificate authority | .ca file; default: none | Certificate authority is an entity that issues digital certificates. A digital certificate certifies the ownership of a public key by the named subject of the certificate. |
| TLS: Client certificate | .crt file; default: none | Client certificate is a type of digital certificate that is used by client systems to make authenticated requests to a remote server. Client certificates play a key role in many mutual authentication designs, providing strong assurances of a requester's identity. |
| TLS: Client key | .key file; default: none | Authenticates the client to the server and establishes precisely who they are. |
| TLS: Private key decryption password (optional) | string; default: none | A password used to decrypt the server's private key. Use only if server's .key file is encrypted with a password. |
| Static key: Static pre-shared key | .key file; default: none | Uploads a secret key file used for server–client authentication. |
Additional notes:
- Some configuration fields become available only when certain other parameters are selected. The names of the parameters are followed by a prefix that specifies the authentication type under which they become visible. Different color codes are used for different prefixes:
- Red for Authentication: TLS
- Purple for Authentication: Static key
- Blue for Authentication: Password
- After changing any of the parameters, don't forget to click the Save & Apply button located at the bottom-right side of the page.
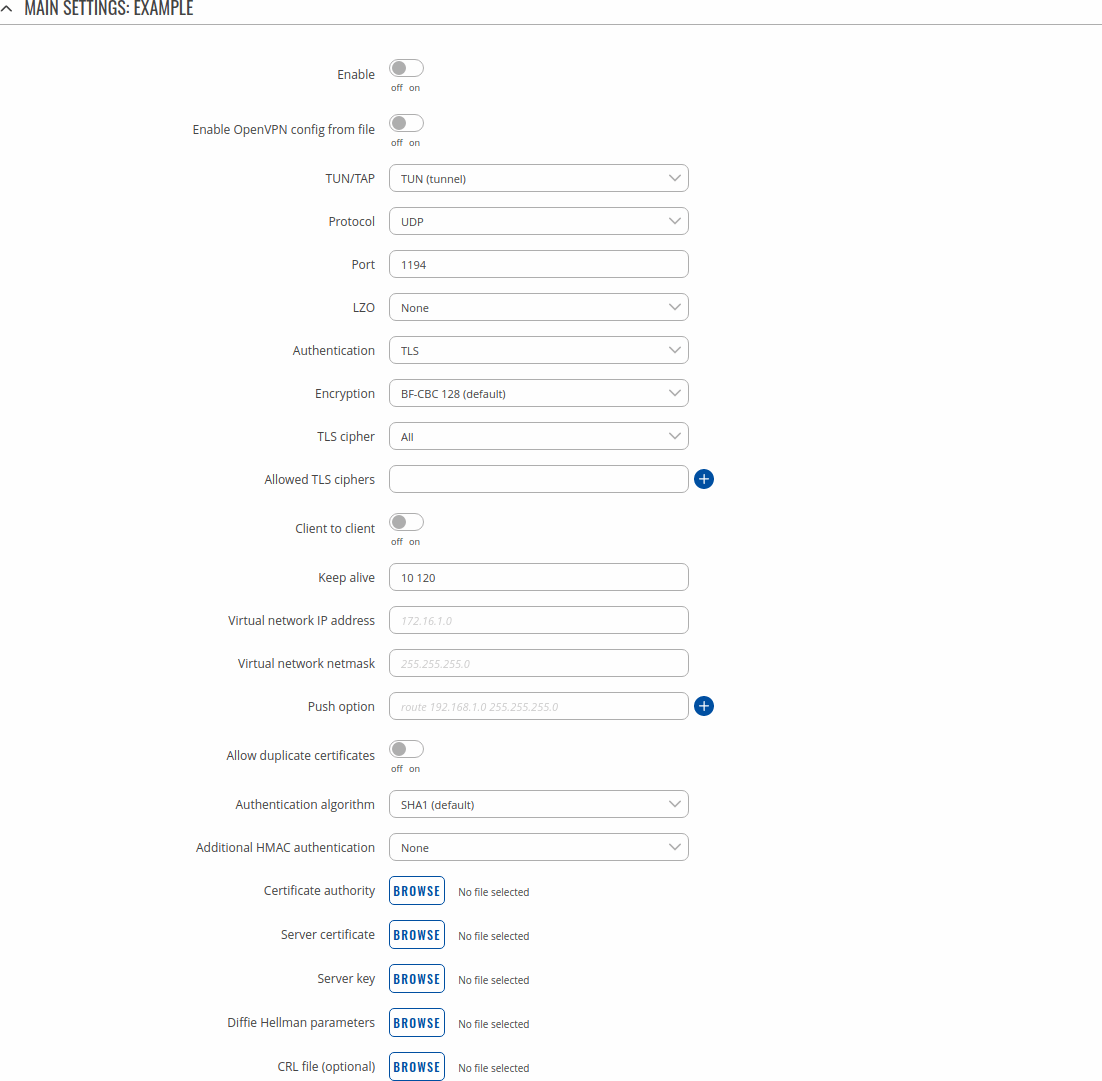
OpenVPN Server
An OpenVPN server is an entity that waits for incoming connections from OpenVPN clients. To create a new server instance, go to the Services → VPN → OpenVPN section, select Role: Server, enter a custom name and click the 'Add' button. An OpenVPN server instance with the given name will appear in the "OpenVPN Configuration" list. Only one OpenVPN server instance is allowed to be added.
A server needs to have a public IP address in order to be available from the public network (the Internet).
To begin configuration, click the button that looks like a pencil next to the server instance. Refer to the figure and table below for information on the OpenVPN server's configuration fields:
| Field | Value | Description |
|---|---|---|
| Enable | off | on; default: off | Turns the OpenVPN instance on or off. |
| Enable OpenVPN config from file | off | on; default: off | Enables or disables custom OpenVPN config from file. |
| TUN/TAP | TUN (tunnel) | TAP (bridged); default: TUN (tunnel) | Virtual network device type.
|
| Protocol | UDP | TCP; default: UDP | Transfer protocol used by the OpenVPN connection.
|
| Port | integer [0..65535]; default: 1194 | TCP/UDP port number used for the connection. Make sure it matches the port number specified on the server side. NOTE: traffic on the selected port will be automatically allowed in device firewall rules. |
| LZO | Yes | No | None; default: None | Turns LZO data compression on or off. |
| Encryption | DES-CBC 64 | RC2-CBC 128 | DES-EDE-CBC 128 | DES-EDE3-CBC 192 | DESX-CBC 192 | BF-CBC 128 | RC2-40-CBC 40 | CAST5-CBC 128 | RC2-40CBC 40 | CAST5-CBC 128 | RC2-64-CBC 64| AES-128-CBC 128 | AES-192-CBC 192 | AES-256-CBC 256 | none; default: BF-CBC 128 | Algorithm used for packet encryption. |
| Authentication | TLS | Static Key | TLS/Password; default: TLS | Authentication mode, used to secure data sessions.
|
| Static key: Local tunnel endpoint IP | ip; default: none | IP address of the local OpenVPN network interface. |
| Static key: Remote tunnel endpoint IP | ip; default: none | IP address of the remote OpenVPN network (client) interface. |
| Static key: Remote network IP address | ip; default: none | LAN IP address of the remote network (client). |
| Static key: Remote network IP netmask | netmask; default: none | LAN IP subnet mask of the remote network (client). |
| TLS/TLS/Password: TLS cipher | All | DHE+RSA | Custom; default: All | Packet encryption algorithm cipher. |
| TLS/Password: Allowed TLS ciphers | All | DHE+RSA | Custom; default: All | A list of TLS ciphers accepted by this connection. |
| TLS/TLS/Password: Client to client | off | on; default: off | Allows OpenVPN clients to communicate with each other on the VPN network. |
| TLS/TLS/Password: Keep alive | two integers separated by a space; default: none | Defines two time intervals: the first is used to periodically send ICMP requests to the OpenVPN server, the second one defines a time window, which is used to restart the OpenVPN service if no ICMP response is received during the specified time slice. When this value is specifiied on the OpenVPN server, it overrides the 'keep alive' values set on client instances. Example: 10 120 |
| TLS/TLS/Password: Virtual network IP address | ip; default: none | IP address of the OpenVPN network. |
| TLS/TLS/Password: Virtual network netmask | netmask; default: none | Subnet mask of the OpenVPN network. |
| TLS/TLS/Password: Push option | OpenVPN options; default: none | Push options are a way to "push" routes and other additional OpenVPN options to connecting clients. |
| TLS/TLS/Password: Allow duplicate certificates | off | on; default: off | When enabled allows multiple clients to connect using the same certificates. |
| TLS/Password: User name | string; default: none | Username used for authentication to this OpenVPN server. |
| TLS/Password: Password | string; default: none | Password used for authentication to this OpenVPN server. |
| Static key: Static pre-shared key | .key file; default: none | Uploads a secret key file used for server–client authentication. |
| TLS/TLS/Password: Certificate authority | .ca file; default: none | Certificate authority is an entity that issues digital certificates. A digital certificate certifies the ownership of a public key by the named subject of the certificate. |
| TLS/TLS/Password: Server certificate | .crt file; default: none | A type of digital certificate that is used to identify the OpenVPN server. |
| TLS/TLS/Password: Server key | .key file; default: none | Authenticates clients to the server. |
| TLS/TLS/Password: Diffie Hellman parameters | .pem file; default: none | DH parameters define how OpenSSL performs the Diffie-Hellman (DH) key-exchange. |
| TLS/TLS/Password: CRL file (optional) | .pem file | .crl file; Default: none | A certificate revocation list (CRL) file is a list of certificates that have been revoked by the certificate authority (CA). It indicates which certificates are no longer acccepted by the CA and therefore cannot be authenticated to the server. |
Additional notes:
- Some configuration fields become available only when certain other parameters are selected. The names of the parameters are followed by a prefix that specifies the authentication type under which they become visible. Different color codes are used for different prefixes:
- Red for Authentication: TLS
- Purple for Authentication: Static key
- Blue for Authentication: TLS/Password
- After changing any of the parameters, don't forget to click the Save & Apply button located at the bottom-right side of the page.
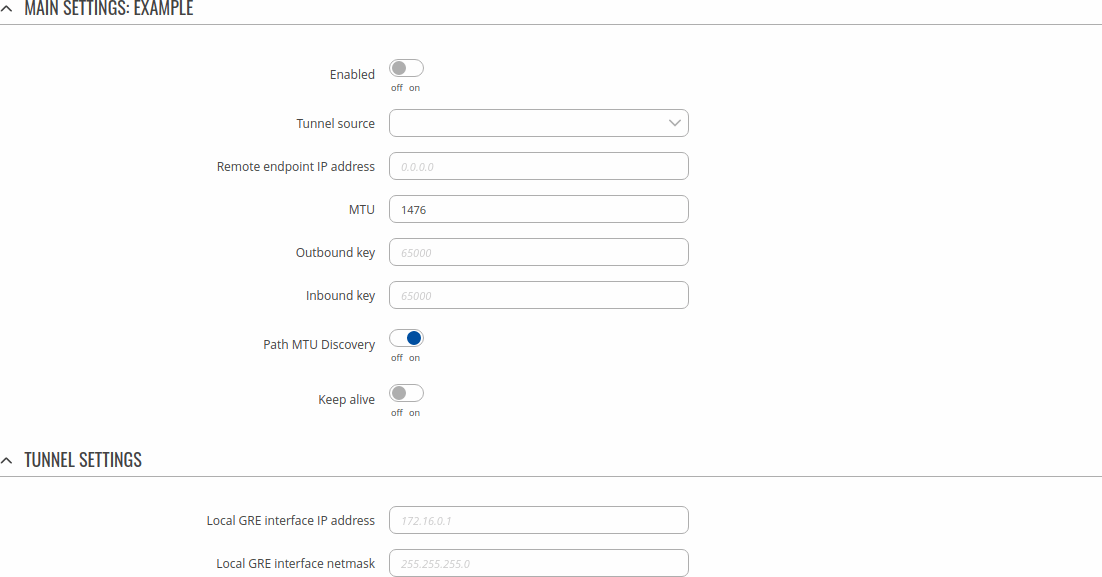
TLS Clients
TLS Clients is a way to differentiate clients by their Common Names (CN), which are found in the client certificate file. It can be used to assign specific VPN addresses to corresponding clients and bind them to their LAN addresses, making the server aware of which client has which LAN IP address.
The TLS Clients section can be found in the OpenVPN Server configuration window, provided that the OpenVPN server uses TLS or TLS/Password authentication methods. To create a new TLS client, type in the new client‘s name in the text field found bellow the TLS Clients tab and click the 'Add' button. Refer to the figure and table below for information on the TLS Clients' configuration fields:
| Field | Value | Description |
|---|---|---|
| Endpoint name | string; default: none | A custom name for the client. |
| Common name (CN) | string; default: none | Client’s Common Name (CN) found in the client certificate file. |
| Virtual local endpoint | ip; default: none | Client’s local address in the virtual network. |
| Virtual remote endpoint | ip; default: none | Client’s remote address in the virtual network. |
| Private network | ip; default: none | Client’s private network (LAN) IP address. |
| Private netmask | netmask; default: none | Client’s private network (LAN) IP netmask. |
GRE
Generic Routing Encapsulation (GRE) is a tunneling protocol used to establish point-to-point connections between remote private networks. GRE tunnels encapsulate data packets in order to route other protocols over IP networks.
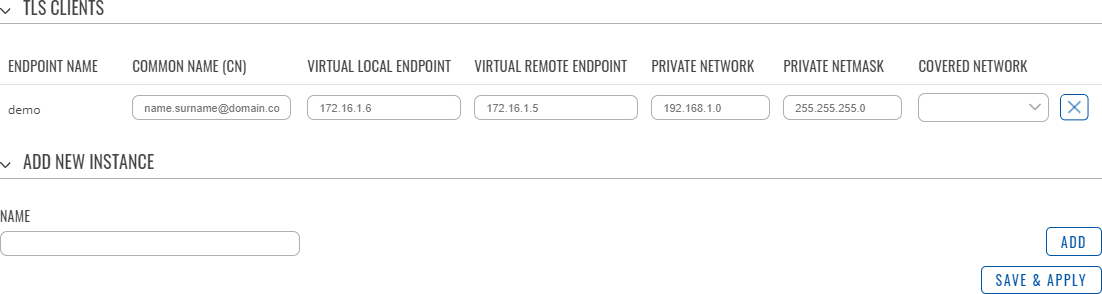
GRE: Main & Tunnel Settings
To create a new GRE instance, go to the Services → VPN → GRE section, enter a custom name and click the 'Add' button. A GRE instance with the given name will appear in the "GRE Configuration" list.
To begin configuration, click the button that looks like a pencil located next to the instance. Refer to the figure and table below for information on the fields located in the GRE instance configuration section.
| Field | Value | Description |
|---|---|---|
| Enabled | off | on; default: off | Turns the GRE instance on or off. |
| Tunnel source | network interface; default: none | Network interface used to establish the GRE Tunnel. |
| Remote endpoint IP address | ip; default: none | External IP address of another GRE instance used to establish the initial connection between peers. |
| MTU | integer; default: 1476 | Sets the maximum transmission unit (MTU) size. It is the largest size of a protocol data unit (PDU) that can be transmitted in a single network layer transaction. |
| TTL | integer [0..255]; default: 255 | Sets a custom TTL (Time to Live) value for encapsulated packets. TTL is a field in the IP packet header which is initially set by the sender and decreased by 1 on each hop. When it reaches 0 it is dropped and the last host to receive the packet sends an ICMP "Time Exceeded" message back to the source. |
| Outbound key | integer [0..65535]; default: none | A key used to identify outgoing packets. This value should match the "Inbound key" value set on the opposite GRE instance or both key values should be omitted on both sides. |
| Inbound key | integer [0..65535]; default: none | A key used to identify incoming packets. This value should match the "Outbound key" value set on the opposite GRE instance or both key values should be omitted on both sides. |
| Path MTU Discovery | off | on; default: on | When unchecked, sets the nopmtudisc option for tunnel. Can not be used together with the TTL option. |
| Keep alive | off | on; default: off | Turns "keep alive" on or off. The "keep alive" feature sends packets to the remote instance in order to determine the health of the connection. If no response is received, the device will attempt to re-establish the tunnel. |
| Keep alive interval | integer [0..255]; default: none | Frequency (in seconds) at which "keep alive" packets are sent to the remote instance. |
| Local GRE interface IP address | ip; default: none | IP address of the local GRE Tunnel network interface. |
| Local GRE interface netmask | netmask; default: none | Subnet mask of the local GRE Tunnel network interface. |
GRE: Routing Settings
Routing settings are used to configure routes to networks that are behind the device that hosts the opposite GRE instance. To add a new route, simply click the 'Add' button. For information on configuring the route refer to the figure and table below.
| Field | Value | Description |
|---|---|---|
| Remote subnet IP address | ip; default: none | IP address of the network behind the device that hosts the remote GRE instance. |
| Remote subnet netmask | netmask; default: none | Subnet mask of the network behind the device that hosts the remote GRE instance. |
IPsec
To create a new IPsec instance, go to the Services → VPN → IPsec section, enter a custom name and click the 'Add' button. An IPsec instance with the given name will appear in the "IPsec Configuration" list.
To begin configuration, click the button that looks like a pencil located next to the instance.
IPsec Instance
The general settings section is used to configure the main IPsec parameters. Refer to the figure and table below for information on the configuration fields located in the general settings section.
| Field | Value | Description |
|---|---|---|
| Enable | off | on; default: off | Turns the IPsec instance on or off. |
| Remote endpoint | host | ip; default: none | IP address or hostname of the remote IPsec instance. |
| Authentication method | Pre-shared key | X.509; default: Pre-shared key | Specify authentication method. Choose between Pre-shared key and X.509 certificates. |
| Pre-shared key: Pre shared key | string; default: none | A shared password used for authentication between IPsec peers before a secure channel is established. |
| X.509: Key | .key file; default: none | A public key file. |
| X.509: Local Certificate | .pem file; default: none | A local certificate file. |
| X.509: CA Certificate | .crt file; default: none | A certificate authority file. |
| Local identifier | ip | string; default: none | Defines how the user (left participant) will be identified during authentication.
|
| Remote identifier | ip | string; default: none | Defines how the right participant will be identified during authentication.
|
| Multiple secrets | off | on; default: off | Enable to show Global Secret Settings section for configuring multiple secrets. |
Additional notes:
- Some configuration fields become available only when certain other parameters are selected. The names of the parameters are followed by a prefix that specifies the authentication type under which they become visible. Different color codes are used for different prefixes:
- Chocolate for Authentication method: Pre-shared key
- Dark red for Authentication method: X.509
Global Secrets Settings
This section is displayed when Multiple secrets is enabled in General settings. You can add new instances by pressing Add.
| Field | Value | Description |
|---|---|---|
| ID Selector | %any, IP or FQDN; default: none | Each secret can be preceded by a list of optional ID selectors. A selector is an IP address, a Fully Qualified Domain Name, user@FQDN or %any. When using IKEv1 use IP address. NOTE: IKEv1 only supports IP address ID selector. |
| Type | psk | xauth; default: psk | IPSec secret type. NOTE: XAUTH secrets are IKEv1 only. |
| Secret | string; default: none | A shared password to authenticate between the peers. Minimum length is 5 symbols. All characters are allowed except `. |
Advanced Settings
The Advanced settings section is only visible when X.509 is selected as Authentication method.
| Field | Value | Description |
|---|---|---|
| Remote Certificate | .crt file; default: none | Selects a certificate file from a computer. |
IPsec Instance: Connection Settings
The connection settings section is used to configure the main parameters of an IPsec connection. Refer to the figure and table below for information on the configuration fields located in the connection settings section.
General Settings
| Field | Value | Description |
|---|---|---|
| Mode | Start | Add | Route; default: Start | Specifies which operation will be done automatically at IPSec startup. |
| Type | Tunnel | Transport; default: Tunnel | Type of connection.
|
| Tunnel: Default route | off | on; default: off | Turn on to route all traffic through IPSec tunnel. |
| Tunnel: Local subnet | ip/netmask | default: none | Local IP address and subnet mask used to determine which part of the network can be accessed in the VPN network. Netmask range [0..32]. If left empty, IP address will be selected automatically. |
| Tunnel: Remote subnet | ip/netmask; default: none | Remote network IP address and subnet mask used to determine which part of the network can be accessed in the VPN network. Netmask range [0..32]. This value must differ from the device’s LAN IP. |
| Transport: Bind to | GRE interface; default: none | Bind to GRE interface to create GRE over IPsec. |
| Key exchange | IKEv1 | IKEv2; default: IKEv1 | Internet Key Exchange (IKE) version used for key exchange.
|
Additional notes:
- Some configuration fields become available only when certain other parameters are selected. The names of the parameters are followed by a prefix that specifies the authentication type under which they become visible. Different color codes are used for different prefixes:
- Red for Type: Tunnel
- Purple for Type: Transport
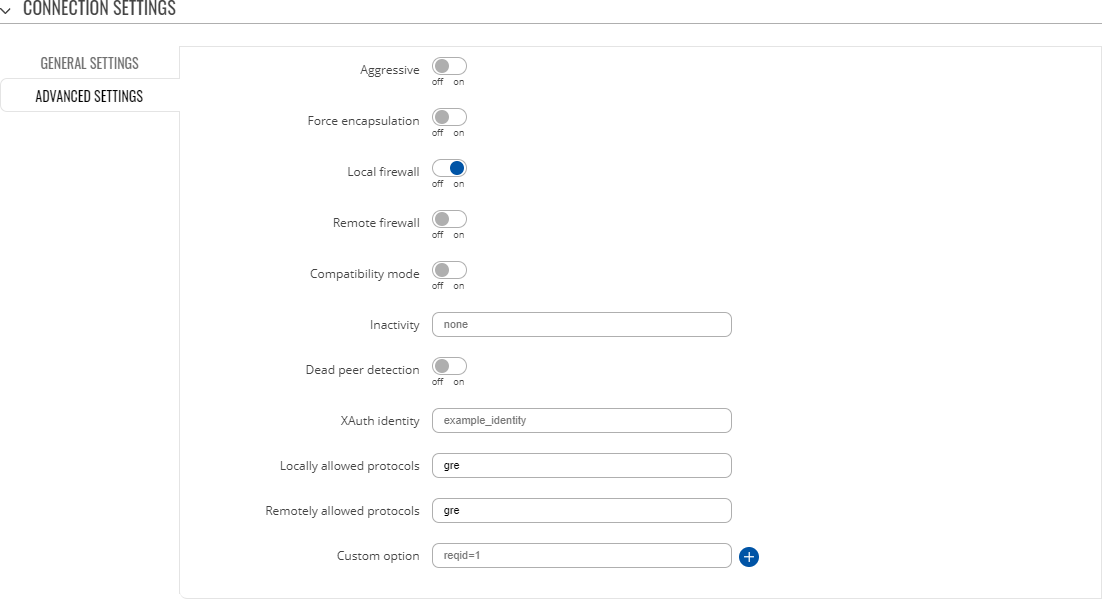
Advanced settings
| Field | Value | Description |
|---|---|---|
| Aggressive | off | on; default: off | Turn aggressive mode on or off for outgoing connections. Aggressive mode performs fewer exchanges (a total of 4 messages) than Main mode (a total of 6 messages) by storing most data into the first exchange. In aggressive mode, the information is exchanged before there is a secure channel, making it less secure but faster than main mode. Aggressive mode is available only with IKEv1; if IKEv2 is selected this field becomes hidden. |
| Force encapsulation | off | on; default: off | Forces UDP encapsulation for ESP packets even if a "no NAT" situation is detected. |
| Local firewall | off | on; default: on | Adds necessary firewall rules to allow traffic of this IPsec instance on this device. |
| Remote firewall | off | on; default: on | Adds necessary firewall rules to allow traffic of from the opposite IPsec instance on this device. |
| Inactivity | integer; default: none | Defines timeout interval, after which a CHILD_SA is closed if it did not send or receive any traffic. |
| Dead Peer Detection | off | on; default: off | A function used during Internet Key Exchange (IKE) to detect a "dead" peer. It used to reduce traffic by minimizing the number of messages when the opposite peer in unavailable and as failover mechanism. |
| Dead Peer Detection: DPD action | Restart | Hold | Clear | None; default: Restart | Controls the use of the Dead Peer Detection protocol where notification messages are periodically sent in order to check the liveliness of the IPsec peer. |
| Dead Peer Detection: DPD Delay | integer; default: none | The frequency of sending R_U_THERE messages or INFORMATIONAL exchanges to peer. |
| Tunnel: Remote source IP | ip; default: none | The internal source IP to use in a tunnel for the remote (right) peer. |
| Tunnel: Local source IP | ip; default: none | The internal (left) source IP to use in a tunnel, also known as virtual IP. |
| Tunnel: Remote DNS | ip; default: none | List of DNS server addresses to exchange as configuration attributes. On the responder, only fixed IPv4/IPv6 addresses are allowed and define DNS servers assigned to the client. |
| Locally allowed protocols | string; default: none | Allowed protocols and ports over connection, also called Port Selectors. Defines in form of 'protocol/port' eg:'17/1701' or '17/%any' or 'udp/l2f'. |
| Remotely allowed protocols | string; default: none | Allowed protocols and ports over connection, also called Port Selectors. Defines in form of 'protocol/port' eg:'17/1701' or '17/%any' or 'udp/l2f'. |
| Custom option | string; default: none | Add custom connection parameters. |
| Local source IP | ip; default: none | The internal (left) source IP to use in a tunnel, also known as virtual IP. |
| Tunnel: Passthrough interfaces | network interfaces; default: none | Network interfaces to include in IPsec Passthrough. |
| Tunnel: Passthrough subnets | ip/netmask; default: none | Networks to include in IPsec Passthrough. |
Additional notes:
- Some configuration fields become available only when certain other parameters are selected. The names of the parameters are followed by a prefix that specifies the authentication type under which they become visible. Different color codes are used for different prefixes:
- Red for Type: Tunnel
- Blue for Dead Peer Detection: Enabled
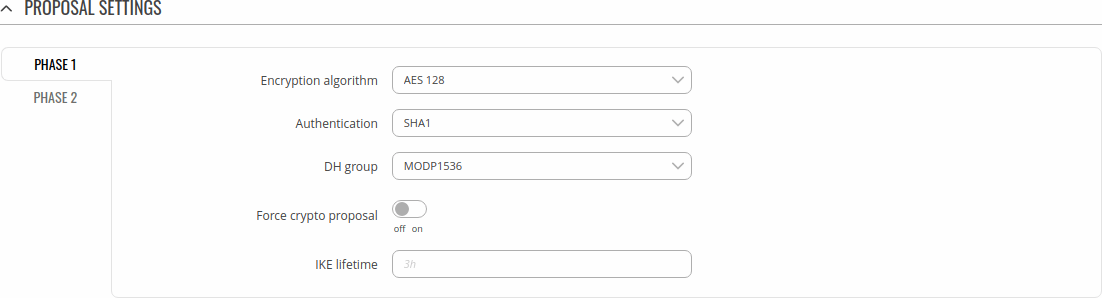
IPsec instance: proposal settings
The proposal settings section is used to configure IKE (Internet Key Exchange) phase 1 & 2 settings. IKE is a protocol used to set up security associations (SAs) for the IPsec connection. This process is required before any IPsec tunnel can be established. It is done in two phases:
| Phase | Mode | |
|---|---|---|
Phase 1
|
Main mode (figure 1)
|
Aggressive mode (figure 2)
|
Phase 2
|
Quick mode
|
|
| Figure 1 |
Figure 2 |
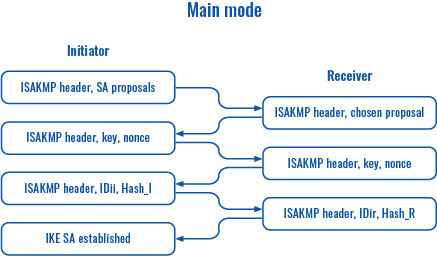 |
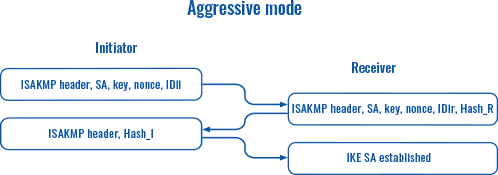 |
Phase 1
| Field | Value | Description |
|---|---|---|
| Encryption algorithm | 3DES | AES 128 | AES 192 | AES 256 | AES128 GCM8 | AES192 GCM8 | AES256 GCM8 | AES128 GCM12 | AES192 GCM12 | AES256 GCM12 | AES128 GCM16 | AES192 GCM16 | AES256 GCM16; default: AES 128 | Algorithm used for data encryption. |
| Authentication | MD5 | SHA1 | SHA256 | SHA384 | SHA512; default: SHA1 | Algorithm used for exchanging authentication and hash information. |
| DH group | MODP768 | MODP1024 | MODP1536 | MODP2048 | MODP3072 | MODP4096 | ECP192 | ECP224 | ECP256 | ECP384 | ECP521; default: MODP1536 | Diffie-Hellman (DH) group used in the key exchange process. Higher group numbers provide more security, but take longer and use more resources to compute the key. Must match with another incoming connection to establish IPSec. |
| Force crypto proposal | off | on; default: off | Only chosen proposals will be used when turned on. |
| IKE Lifetime | string; default: none | How long the keying channel of a connection (ISAKMP or IKE SA) should last before being renegotiated. The time is specified in seconds. The s, m, h and d suffixes explicitly define the units for seconds, minutes, hours and days, respectively. |
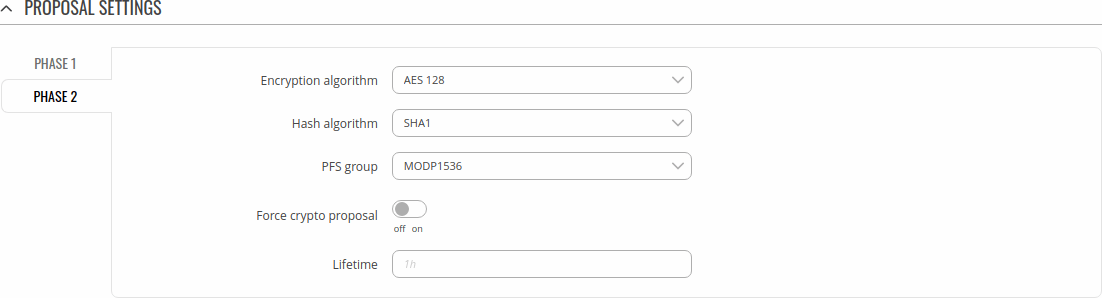
Phase 2
| Field | Value | Description |
|---|---|---|
| Hash algorithm | 3DES | AES 128 | AES 192 | AES 256 | AES128 GCM8 | AES192 GCM8 | AES256 GCM8 | AES128 GCM12 | AES192 GCM12 | AES256 GCM12 | AES128 GCM16 | AES192 GCM16 | AES256 GCM16; default: AES 128 | Algorithm used for data encryption. |
| Hash algorithm | MD5 | SHA1 | SHA256 | SHA384 | SHA512; default: SHA1 | Algorithm used for exchanging authentication and hash information. |
| PFS group | MODP768 | MODP1024 | MODP1536 | MODP2048 | MODP3072 | MODP4096 | ECP192 | ECP224 | ECP256 | ECP384 | ECP521; default: MODP1536 | The PFS (Perfect Forward Secrecy). Must match with another incoming connection to establish IPSec. |
| Force crypto proposal | off | on; default: off | Only chosen proposals will be used when turned on. |
| Lifetime | string; default: none | How long the keying channel of a connection (ISAKMP or IKE SA) should last before being renegotiated. The time is specified in seconds. The s, m, h and d suffixes explicitly define the units for seconds, minutes, hours and days, respectively. |
PPTP
Point-to-Point Tunneling Protocol (PPTP) is a type of VPN protocol that uses a TCP control channel and a Generic Routing Encapsulation tunnel to encapsulate PPP packets.
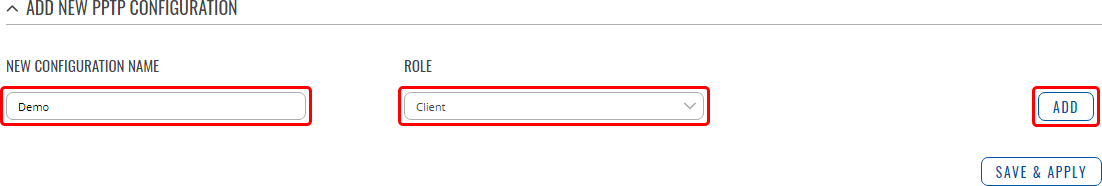
PPTP client
A PPTP client is an entity that initiates a connection to a PPTP server. To create a new client instance, go to the Services → VPN → PPTP section, select Role: Client, enter a custom name and click the 'Add' button:
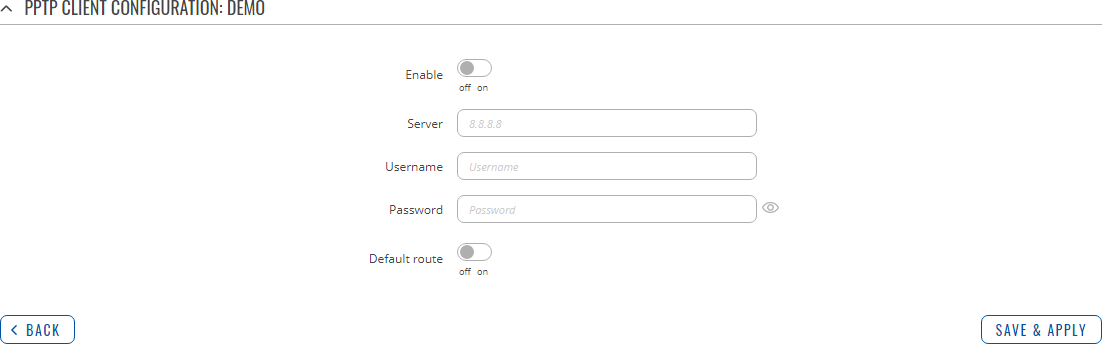
You should be redirected to the configuration page for the newly added PPTP Client which should look similar to this:
| Field | Value | Description |
|---|---|---|
| Enable | off | on; default: off | Turns the PPTP instance on or off. |
| Server | ip | host; default: none | IP address or hostname of a PPTP server. |
| Username | string; default: none | Username used for authentication to the PPTP server. |
| Password | string; default: none | Password used for authentication to the PPTP server. |
| Default route | off | on; default: off | When turned on, this connection will become the device default route. This means that all traffic directed to the Internet will go through the PPTP server and the server's IP address will be seen as this device's source IP to other hosts on the Internet. |
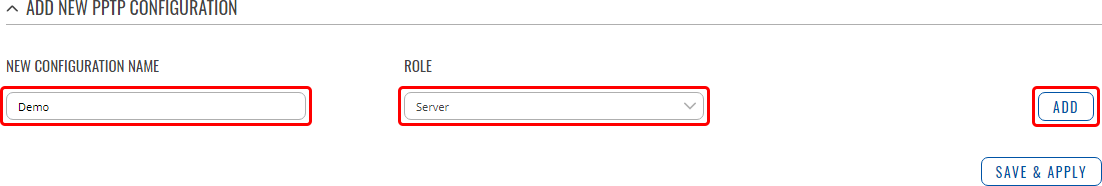
PPTP server
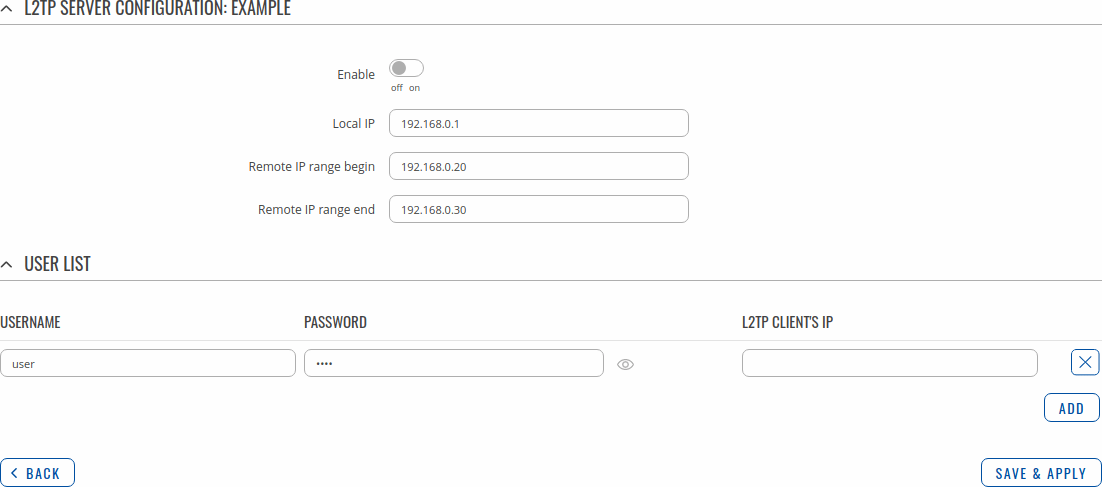
A PPTP server is an entity that waits for incoming connections from PPTP clients. To create a new server instance, go to the Services → VPN → PPTP section, select Role: Server, enter a custom name and click the 'Add' button:
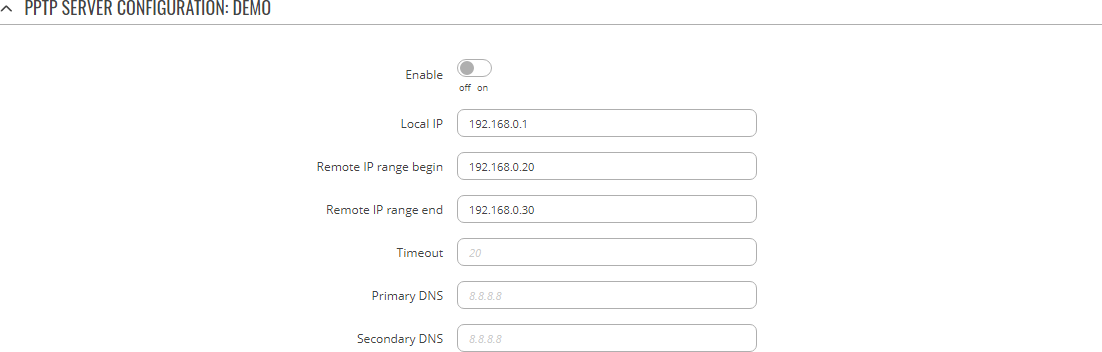
You should be redirected to the configuration page for the newly added PPTP Server which should look similar to this:
| Field | Value | Description |
|---|---|---|
| Enable | off | on; default: off | Turns the PPTP instance on or off. |
| Local IP | ip; default: 192.168.0.1 | IP address of this PPTP network interface. |
| Remote IP range start | ip; default: 192.168.0.20 | PPTP IP address leases will begin from the address specified in this field. |
| Remote IP range end | ip; default: 192.168.0.30 | PPTP IP address leases will end with the address specified in this field. |
| Timeout | integer; default: none | Time in seconds. If no packets pass through the tunnel between this server and a client, the server will terminate the connection to that client after the amount of time specified in this field passes. |
| Primary DNS | ip; default: none | IP address of the primary DNS server. |
| Secondary DNS | ip; default: none | IP address of the secondary DNS server. |
The User List section is used to user authentication settings required to successfully connect to this server. The list is empty by default. Click the 'Add' button to create a new PPTP User:
| Field | Value | Description |
|---|---|---|
| Username | string; default: none | Username used for authentication to this PPTP server. |
| Password | string; default: none | Password used for authentication to this PPTP server. |
| PPTP Client's IP | ip; default: none | Assigns an IP address to the client that uses the adjacent authentication info. This field is optional and if left empty the client will simply receive an IP address from the IP pool defined above. |
Note: there can only one PPTP Server configuration on the device.
SSTP
Secure Socket Tunneling Protocol (SSTP) is a VPN protocol designed to transport PPP traffic via a secure SSL/TLS channel.
Note: SSTP is additional software that can be installed from the Services → [[{{{name}}} Package Manager|Package Manager]] page.
SSTP configuration
To create a new SSTP instance, go to the Services → VPN → SSTP section, enter a custom name and click the 'Add' button. An SSTP instance with the given name will appear in the "SSTP Configuration" list.
To begin configuration, click the 'Edit' button located next to the instance. Refer to the figure and table below for information on the SSTP instance's configuration fields:
| Field | Value | Description |
|---|---|---|
| Enable | off | on; default: off | Turns the SSTP instance on or off. |
| Server IP address | ip | host; default: none | IP address or hostname of a SSTP server. |
| User name | string; default: none | Username used for authentication to the SSTP server. |
| Password | string; default: none | Password used for authentication to the SSTP server. |
| Certificate files from device | off | on; default: off | Turn on this option if you want to select generated certificate files from device. |
| CA cert | .crt file; default: none | Upload a Certificate authority (CA) file. |
| Default route | off | on; default: off | When turned on, this connection will become the device default route. This means that all traffic directed to the Internet will go through the SSTP server and the server's IP address will be seen as this device's source IP to other hosts on the Internet. NOTE: this can only be used when [[{{{name}}} Failover|Failover]] is turned off. |
Stunnel
Stunnel is an open-source a proxy service that adds TLS encryption to clients and servers already existing on a VPN network. TLS encryption provided by Stunnel can be used as an additional layer of encryption for data sent by VPN. This procedure increases the security of the established connection and provides higher chances of passing a Deep packet inspection (DPI) check.
Stunnel globals
The Stunnel Globals section is used to manage the Stunnel service as a whole.
Refer to the figure and table below for information on the fields contained in the Stunnel Globals section.
Note: Stunnel is additional software that can be installed from the Services → [[{{{name}}} Package Manager|Package Manager]] page.
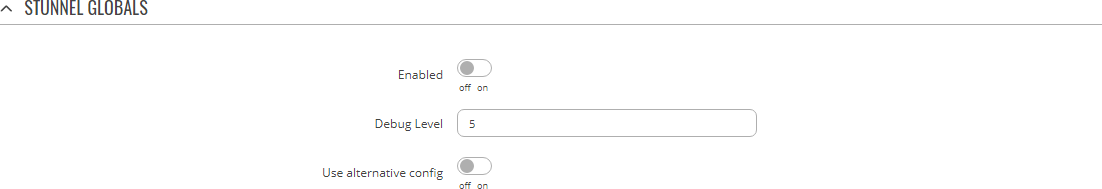
| Field | Value | Description |
|---|---|---|
| Enabled | off | on; default: off | Turns the Stunnel service on or off. If this is unchecked, Stunnel instances will not start (even if they are enabled individually); therefore, it is necessary to check this field in order to make Stunnel active on the router. |
| Debug Level | integer [0..7]; default: 5 | Debugging to log output level.
|
| Use alternative config | off | on; default: off | Turns the possibility to upload an external Stunnel configuration file on or off.if you turn this on, other Stunnel configurations present in the router will become inactive. |
| Upload alternative config | file; default: none | Uploads an Stunnel configuration file. |
Stunnel instance
To create a new Stunnel instance, go to the Services → VPN → Stunnel section, enter a custom name and click the 'Add' button. An Stunnel instance with the given name will appear in the "Stunnel Configuration" list.
To begin configuration, click the 'Edit' button located next to the instance. Refer to the figure and table below for information on the Stunnel instance's configuration fields:
| Field | Value | Description |
|---|---|---|
| Enable | off | on; default: off | Turns the Stunnel instance on or off. |
| Operating Mode | Server | Client; default: Server | Selects the Stunnel instance's role.
|
| Listen IP | ip; default: none | Makes the instance "listen" for incoming connections on the specified IP address. When left empty, the value of this field defaults to localhost (127.0.0.1). |
| Listen Port | integer [0..65535]; default: none | Makes the instance "listen" for incoming connections on the specified TCP port. Make sure you chose a port that is not being used by another service. You will also have to allow traffic on the specified port. |
| Connect IP's | ip:port; default: none | IP:Port to listen for VPN connections. When left empty the value of this field is interpreted as localhost. Must contain at least one item. If multiple options are specified, remote address is chosen using a round-robin algorithm. |
| TLS Cipher | None | Secure | Custom; default: None | Packet encryption algorithm cipher. |
| Custom: Allowed TLS Ciphers | string; default: none | A list of TLS ciphers accepted for this connection. |
| Application Protocol | Connect | SMTP | Not specified; default: Not specified | This option enables initial, protocol-specific negotiation of the TLS encryption. The protocol option should not be used with TLS encryption on a separate port. |
| Connect: Protocol Authentication | Basic | NTLM; default: Basic | Authentication type for the protocol negotiations. |
| SMTP: Protocol Authentication | Plain | Login; default: Plain | Authentication type for the protocol negotiations. |
| Certificate File | .crt file; default: none | TLS client or server certificate file. |
| Private Key | .key file; default: none | TLS client or server key file. |
Additional notes:
- Some configuration fields become available only when certain other parameters are selected. The names of the parameters are followed by a prefix that specifies the authentication type under which they become visible. Different color codes are used for different prefixes:
- Blue for TLS Cipher: Custom
- Dark red for Application Protocol: Connect
- Chocolate for Application Protocol: SMTP
DMVPN
Dynamic Multipoint VPN (DMVPN) is a method of building scalable IPsec VPNs. DMVPN is configured as a hub-and-spoke network, where tunnels between spokes are built dynamically; therefore, no change in configuration is required on the hub in order to connect new spokes.
Note: DMPVN is additional software that can be installed from the Services → [[{{{name}}} Package Manager|Package Manager]] page.
DMVPN configuration
To create a new DMVPN instance, go to the Services → VPN → DMVPN section, enter a custom name and click the 'Add' button. A DMVPN instance with the given name will appear in the "DMVPN Configuration" list.
To begin configuration, click the button that looks like a pencil located next to the instance. Refer to the figures and tables below for information on the DMVPN instance configuration:
| Field | Value | Description |
|---|---|---|
| Enabled | off | on; default: off | Turns the DMVPN instance on or off. |
| Working mode | Spoke | Hub; default: Spoke | Selects the role of this instance
|
| Hub address | ip | host; default: none | IP address or hostname of a DMVPN hub. |
| Field | Value | Description |
|---|---|---|
| Tunnel source | network interface; default: none | Network interface used to establish the GRE Tunnel. |
| Local GRE interface IP address | ip; default: none | IP address of the local GRE Tunnel instance. |
| Spoke: Remote GRE interface IP address | ip; default: none | IP address of the remote GRE Tunnel instance. |
| Hub: Local GRE interface netmask | netmask; default: none | Subnet mask of the local GRE Tunnel instance. |
| GRE MTU | integer; default: none | Sets the maximum transmission unit (MTU) size. It is the largest size of a protocol data unit (PDU) that can be transmitted in a single network layer transaction. |
| GRE keys | integer [0..65535]; default: none | A key used to identify incoming and outgoing GRE packets. |
| Field | Value | Description |
|---|---|---|
| Local identifier | ip | string; default: none | Defines how the user (IPsec instance) will be identified during authentication.
|
| Remote identifier | ip | string; default: none | Defines how the right participant will be identified during authentication.
|
| Pre-shared key | string; default: none | A shared password used for authentication between IPsec peers. |
| Encryption algorithm | 3DES | AES 128 | AES 192 | AES 256 | AES128 GCM8 | AES192 GCM8 | AES256 GCM8 | AES128 GCM12 | AES192 GCM12 | AES256 GCM12 | AES128 GCM16 | AES192 GCM16 | AES256 GCM16; default: AES 128 | Algorithm used for data encryption. |
| Authentication/Hash algorithm | MD5 | SHA1 | SHA256 | SHA384 | SHA512; default: SHA1 | Algorithm used for exchanging authentication and hash information. |
| DH/PFS group | MODP768 | MODP1024 | MODP1536 | MODP2048 | MODP3072 | MODP4096 | ECP192 | ECP224 | ECP256 | ECP384 | ECP521; default: MODP1536 | Diffie-Hellman (DH) group used in the key exchange process. Higher group numbers provide more security, but take longer and use more resources to compute the key. Must match with another incoming connection to establish IPSec. |
| Force crypto proposal | off | on; default: off | Only chosen proposals will be used when turned on. |
| IKE Lifetime | string; default: none | How long the keying channel of a connection (ISAKMP or IKE SA) should last before being renegotiated. The time is specified in seconds. The s, m, h and d suffixes explicitly define the units for seconds, minutes, hours and days, respectively. |
| Field | Value | Description |
|---|---|---|
| NHRP network ID | integer; default: 1 | An identifier used to define the NHRP domain. This is a local parameter and its value does not need to match the values specified on other domains. However, the NHRP ID is added to packets which arrive on the GRE interface; therefore, it may be helpful to use the same ID for troubleshooting purposes. |
| NHRP authentication key | string; default: none | A key used in NHRP authentication. |
| NHRP hold time | integer; default: 7200 | Specifies the holding time for NHRP Registration Requests and Resolution Replies sent from this interface or shortcut-target. The hold time is specified in seconds and defaults to two hours. |
L2TP
In computer networking, Layer 2 Tunneling Protocol (L2TP) is a tunneling protocol used to support virtual private networks (VPNs). It is more secure than PPTP but, because it encapsulates the transferred data twice, but it is slower and uses more CPU power.
L2TP client
An L2TP client is an entity that initiates a connection to an L2TP server. To create a new client instance, go to the Services → VPN → L2TP section, select Role: Client, enter a custom name and click the 'Add' button. An L2TP client instance with the given name will appear in the "L2TP Configuration" list.
To begin configuration, click the button that looks like a pencil next to the client instance. Refer to the figure and table below for information on the L2TP client's configuration fields:
| Field | Value | Description |
|---|---|---|
| Enable | off | on; default: off | Turns the L2TP instance on or off. |
| Server | ip | host; default: none | IP address or hostname of an L2TP server. |
| Username | string; default: none | Username used for authentication to the L2TP server. |
| Password | string; default: none | Password used for authentication to the L2TP server. |
| Default route | off | on; default: off | When turned on, this connection will become device default route. This means that all traffic directed to the Internet will go through the L2TP server and the server's IP address will be seen as this device's source IP to other hosts on the Internet. |
L2TP server
An L2TP server is an entity that waits for incoming connections from L2TP clients. To create a new server instance, go to the Services → VPN → L2TP section, select Role: Server, enter a custom name and click the 'Add' button. An L2TP server instance with the given name will appear in the "L2TP Configuration" list. Only one L2TP server instance is allowed to be added.
A server needs to have a public IP address in order to be available from the public network (the Internet).
To begin configuration, click the button that looks like a pencil next to the server instance. Refer to the figure and table below for information on the L2TP server's configuration fields:
| Field | Value | Description |
|---|---|---|
| Enable | off | on; default: off | Turns the L2TP instance on or off. |
| Local IP | ip; default: 192.168.0.1 | IP address of this L2TP network interface. |
| Remote IP range begin | ip; default: 192.168.0.20 | L2TP IP address leases will begin from the address specified in this field. |
| Remote IP range end | ip; default: 192.168.0.30 | L2TP IP address leases will end with the address specified in this field. |
| User name | string; default: user | Username used for authentication to this L2TP server. |
| Password | string; default: pass | Password used for authentication to this L2TP server. |
| L2TP Client's IP | ip; default: none | Assigns an IP address to the client that uses the adjacent authentication info. This field is optional and if left empty the client will simply receive an IP address from the IP pool defined above. |
L2TPv3
L2TPv3 (Layer Two Tunneling Protocol Version 3) is a point-to-point layer two over IP tunnel. This means you can tunnel L2 protocols like Ethernet, Frame-relay, ATM, HDLC, PPP, etc. over an IP network.
Local settings
| Field | Value | Description | |
|---|---|---|---|
| Enable | off | on; default: off | Turns the L2TPv3 instance on or off. | |
| Local address | ip; default: none | IP address of device's WAN. Note: If left empty, it will take IP address automatically from main WAN interface. | |
| Tunnel ID | integer [1..4294967295]; default: none | Uniquely identifies the tunnel. The value used must match the peer tunnel ID value being used at the peer. | |
| Session ID | integer [1..4294967295]; default: none | The value used must match the tunnel ID value being used at the peer. | |
| Cookie | string; default: none | Must be specified in hexidecimal form and be length of 8 or 16. eg.: 89ABCDEF. |
Peer settings
| Field | Value | Description | |
|---|---|---|---|
| Peer address | ip; default: none | Peer Endpoint IP address. | |
| Peer Tunnel ID | integer [1..4294967295]; default: none | ID of peer's tunnel is specified from 1 to 4294967295. It must match other end tunnel ID. | |
| Peer Session ID | integer [1..4294967295]; default: none | UID of peer's session is specified from 1 to 4294967295. It must match other end session ID. | |
| Peer Cookie | string; default: none | Must be specified in hexidecimal form and be length of 8 or 16. eg.: 89ABCDEF. It must match other end Cookie. |
Instance Settings
| Field | Value | Description | |
|---|---|---|---|
| Bridge to | None | LAN; default: None | Peer Endpoint IP address. | |
| IP Address | ip; default: none | IP address of standalone L2TPv3 interface. | |
| Netmask | netmask; default: none | Netmask of standalone L2TPv3 interface. | |
| MTU | integer [64..9000]; default: none | Sets the maximum transmission unit (MTU) size. It is the largest size of a protocol data unit (PDU) that can be transmitted in a single network layer transaction. | |
| Encapsulation | IP | UDP; default: IP | Specify technology to use when connecting to other end. | |
| Layer 2 specific header type | None | Linux Default; default: Linux Default | It might be neccessary to set this option to none when using other hardware. |
ZeroTier
ZeroTier One is an open source software which can establish Peer to Peer VPN (P2PVPN) connection between various devices running various operating systems. It also provides network management possibilities such as routing and creating firewall rules.
Note: ZeroTier is additional software that can be installed from the Services → [[{{{name}}} Package Manager|Package Manager]] page.
In order to create a new ZeroTier Instance, look to the Add New ZeroTier Configuration section; enter a custom name and click the 'Add' button:
You should be redirected to the configuration page for the newly added ZeroTier Instance which should look similar to this:
| Field | Value | Description |
|---|---|---|
| Enabled | off | on; default: off | Turns the ZeroTier Instance on or off. |
| Networks/td> | hex string; default: none | ZeroTier Network ID. Log in to your ZeroTier account in order to locate the ZeroTier Network ID, which should be a string of hexadecimal characters. |
| Port/td> | integer [0..65535]; default: none | ZeroTier Network port. |
WireGuard
WireGuard is simple, fast, lean, and modern VPN that utilizes secure and trusted cryptography. It intends to be more performant than OpenVPN. WireGuard is designed as general purpose VPN, fit for many different circumstances and while it is currently under heavy development, it already might be regarded as the most secure, easiest to use, and simplest VPN solution.
Note: WireGuard is additional software that can be installed from the Services → [[{{{name}}} Package Manager|Package Manager]] page.
WireGuard works by adding an interface which acts as a tunnel. To create one enter its name and click the Add button.
To configure it click the Edit ![]() button.
button.
General Instance Settings
This section contains General settings of created WireGuard Instance. Here you can find its Public and Private keys and generate them, specify Port and IP addresses for communication.
| Field | Value | Description |
|---|---|---|
| Enable | off | on; default: off | Turns WireGuard Instance on or off. |
| Private Key | string; default: none | Private Key used in authentication. |
| Public Key | string; default: - | Public Key used in authentication. |
| Generate | -(interactive button) | Click to generate Public Key and Private Key. |
| Listen Port | integer [0..65535]; default: none | Specify port to listen for incomming connections. It will be set to a random integer if left empty. |
| IP Addresses | ip; default: none | A single IP address or a list of them for this instance associated with public keys. |
Advanced Settings
Advanced Settings section contains Metric and MTU configuration for this WireGuard interface.
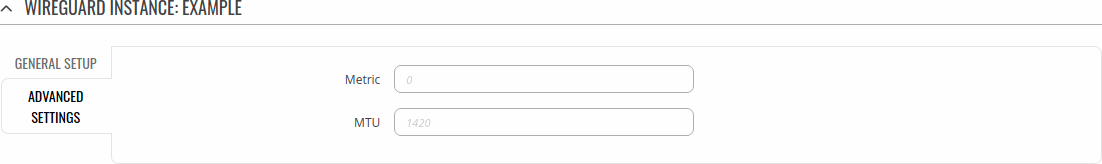
| Field | Value | Description |
|---|---|---|
| Metric | positive integer; default: none | Specify metric for this tunnel interface. Lower number means higher priority. |
| MTU | integer [1280..1420]; default: none | Maximum Transmission Unit for this tunnel interface. |
Peers
The Peers section is used to create and configure all the peers for this interface.
To create one enter its name and click the Add button.
To configure it click the Edit ![]() button.
button.
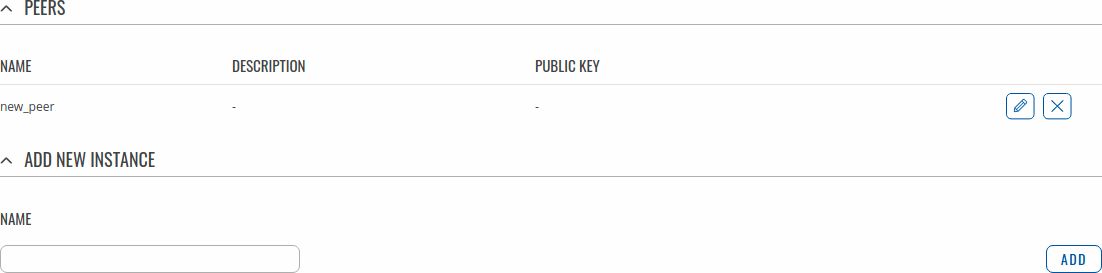
General Peer Settings
In the General section of Peer instance you can configure basic information about the endpoint to allow communications.
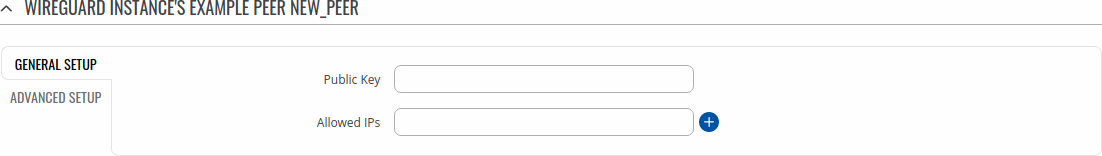
| Field | Value | Description |
|---|---|---|
| Public Key | string; default: none | Endpoint's Public Key. |
| Allowed IPs | ip; default: none | A single IP address or a list of them which are allowed to communicate with this peer. |
Advanced Peer Settings
In the Advanced section of Peer instance you are able to configure additional
settings such as its Description, Endpoint Host and Port, Preshared Key and other.
See more information below.
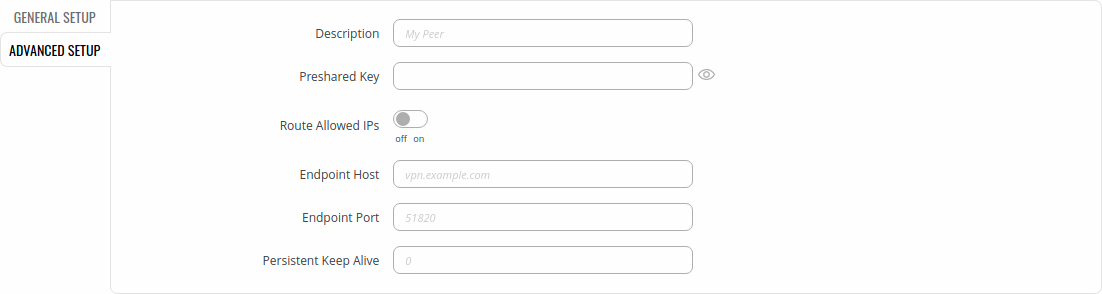
| Field | Value | Description |
|---|---|---|
| Description | string; default: none | Description of this peer. |
| Pre-Shared Key | string; default: none | Base64-encoded preshared key. Adds in an additional layer of symmetric-key cryptography for post-quantum resistance. |
| Route Allowed IPs | off | on; default: off | Enable to create routes for Allowed IPs for this peer. |
| Endpoint Host | ip | url; default: none | IP or URL of Remote Endpoint. |
| Endpoint Port | integer [0..65535]; default: none | Specify port to connect to Remote Endpoint. It will be set to 51820 if left empty. |
| Persistent Keep Alive | integer [0..65535]; default: none | Specify time amount in seconds between Keep Alive messages. By default this option is 0 which means it is disabled. Recommended value for a device behind NAT is 25. |
[[Category:{{{name}}} Services section]]