Difference between revisions of "Template:Networking rut configuration example openvpn bridge use case"
| Line 36: | Line 36: | ||
<tr> | <tr> | ||
<td style="border-bottom: 1px solid white> | <td style="border-bottom: 1px solid white> | ||
| − | Login to the router's WebUI | + | Login to the router's WebUI, navigate to the '''Services → CLI''' page and do the following: |
<ol> | <ol> | ||
<li>Enter username '''''root''''' .</li> | <li>Enter username '''''root''''' .</li> | ||
| Line 54: | Line 54: | ||
<tr> | <tr> | ||
<td style="border-bottom: 1px solid white> | <td style="border-bottom: 1px solid white> | ||
| − | Write the following commands to create and open '''Static key''': | + | Write the following commands to create and open OpenVPN '''Static key''': |
1) cd /etc/easy-rsa | 1) cd /etc/easy-rsa | ||
2) openvpn --genkey --secret static.key | 2) openvpn --genkey --secret static.key | ||
| Line 71: | Line 71: | ||
<tr> | <tr> | ||
<td style="border-bottom: 1px solid white> | <td style="border-bottom: 1px solid white> | ||
| − | Create '''txt''' file on your computer and copy '''Static key''' to it. Copy from the beginning to the end as in the example. | + | Create '''.txt''' file on your computer and copy '''Static key''' to it. Copy from the beginning to the end as in the example. |
</td> | </td> | ||
</tr> | </tr> | ||
| Line 107: | Line 107: | ||
<li>Select '''Authentication: Static key'''.</li> | <li>Select '''Authentication: Static key'''.</li> | ||
<li>Add '''Keep alive''' interval: '''10 120'''.</li> | <li>Add '''Keep alive''' interval: '''10 120'''.</li> | ||
| − | <li>Upload '''Static pre-shared key''' (use the txt file you created in previous steps).</li> | + | <li>Upload '''Static pre-shared key''' (use the .txt file you created in previous steps).</li> |
<li>'''Save''' the changes.</li> | <li>'''Save''' the changes.</li> | ||
</ol> | </ol> | ||
Revision as of 17:12, 4 May 2020
|
|
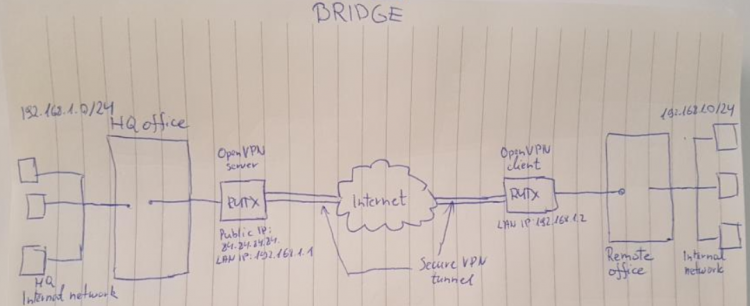
Configuration overview and prerequisites
Prerequisites:
- One RUTxxx router
- A Public Static or Public Dynamic IP addresses
- An end device to configure the router (PC, Laptop, Tablet, Smartphone)
The topology above depicts the OpenVPN scheme. The router with the Public IP address ({{{name}}}) acts as the OpenVPN server and other {{{name}}} acts as client. OpenVPN connects the networks of HQ Office and Remote Office.
When the scheme is realized, remote office workers will be able to reach HQ’s internal network with all internal systems, allowing working from remote office to be possible. All WAN and LAN traffic is going to travel through VPN tunnel.
Configuring HQ office router
OpenVPN
|
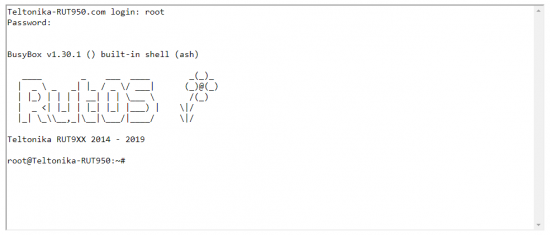
Login to the router's WebUI, navigate to the Services → CLI page and do the following:
|
|
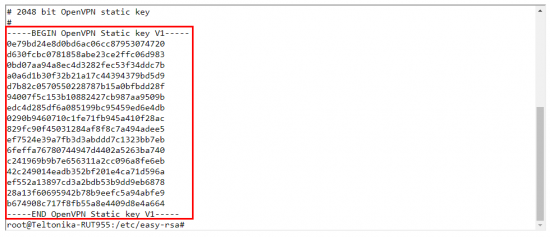
Write the following commands to create and open OpenVPN Static key: 1) cd /etc/easy-rsa 2) openvpn --genkey --secret static.key 3) cat static.key |
|
Create .txt file on your computer and copy Static key to it. Copy from the beginning to the end as in the example. |
|
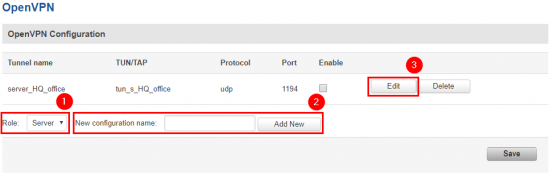
Now go to Services → VPN → OpenVPN. There create a new configuration by selecting role Server, writing New configuration name and pressing Add New button. It should appear after a few seconds. Then press Edit. |
|
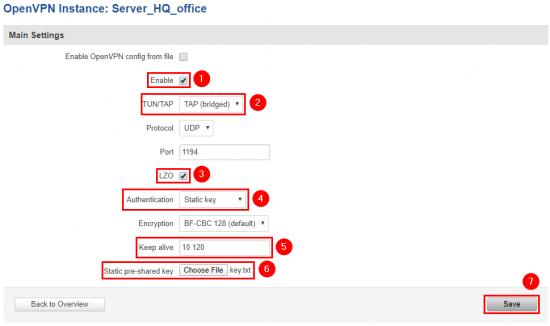
Now apply the following configuration:
|
Configuring remote office router
OpenVPN
|
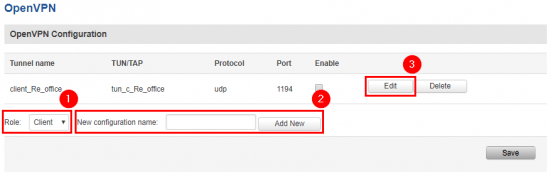
Go to Services → VPN → OpenVPN. There create a new configuration by selecting role Client, writing New configuration name and pressing Add New button. It should appear after a few seconds. Then press Edit. |
|
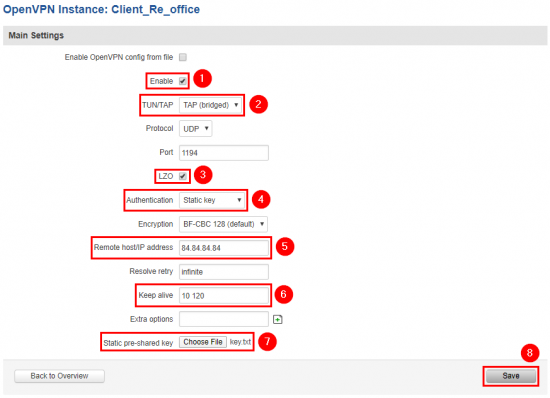
Now apply the following configuration:
|
LAN
|
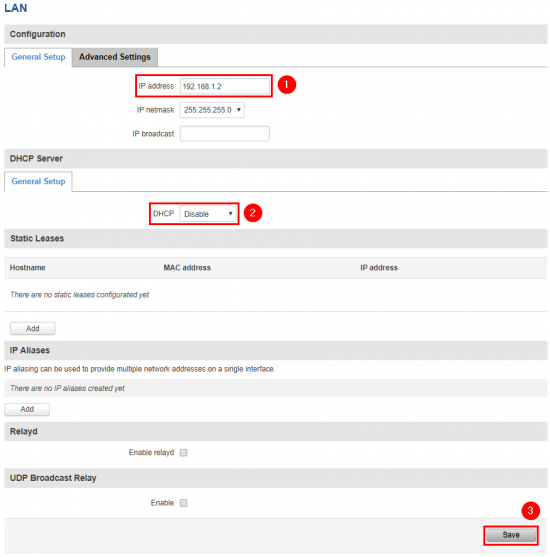
Now go to Network → LAN and apply the following steps:
|
Results
|
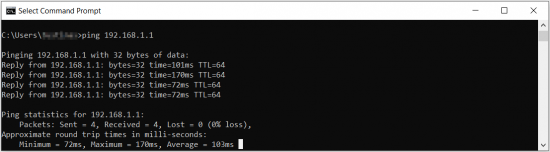
Remote office should now be able to access HQ network resources. To verify the connection you can ping remote RUT HQ server LAN IP and if you get a reply, you have successfully connected to HQ‘s internal network. Also, all LAN addresses should now be leased to the LAN devices by HQ router. |