Setting up a Site-to-Site IPsec Tunnel between Teltonika Networks and Microsoft Azure
Summary
This article will guide you through configuring a Site-to-Site IPsec Tunnel between Teltonika routers/gateways and Microsodt Azure VPN gateway.
Prerequisite
The user needs an Azure account with an active subscription.
Azure Platform
Create a VPN Gateway on the Azure Platform
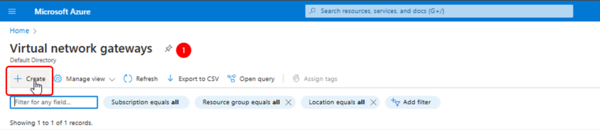
Log into the Azure portal, search for "Virtual Network Gateways" and click on "Create".
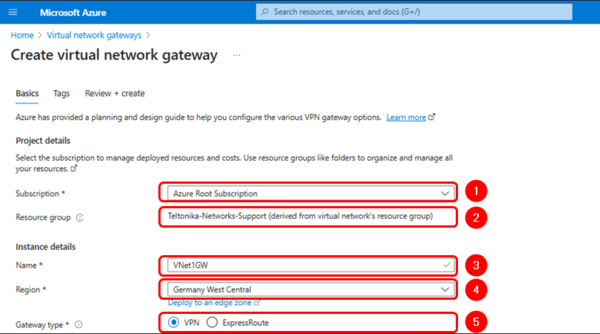
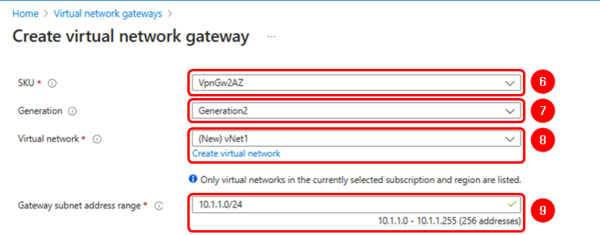
Use the information and images below as reference to complete the settings:
Projects details
- Suscription: Your suscription.
- Resource Group: Your resource group.
Instance details
- Name: VNet1GW.
- Region: Your prefered Region.
- Gateway type: VPN.
- SKU: VpnGW2AZ.
- Generation: Generation2 (mandatory).
- Virtual Network: Select or create a new one.
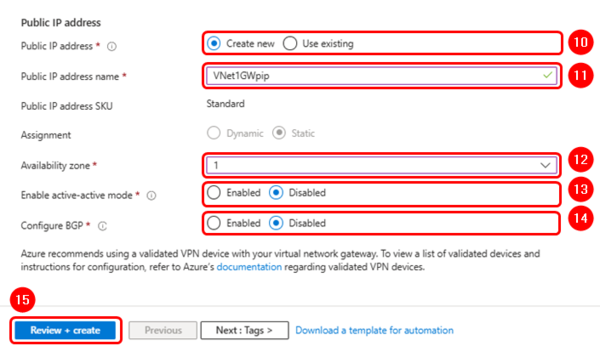
Public IP address
- Public IP address: Create new.
- Public IP address name: Vnet1GWpip.
- Assigment: Static.
- Enable active-active mode: Disabled.
- Configure BGP: Disabled.
Create a Virtual Network
In case you do not have previously created a virtual network, click on the blue URL link to create one and use the default settings as shown in the image below:
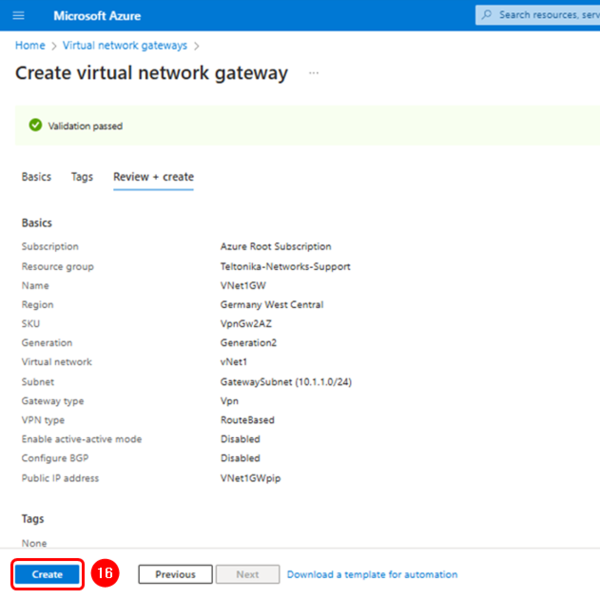
Finish the VPN gateway configuration
After finishing the previous configuration, you can continue with the tags. This section is not mandatory; therefore, we’ll leave it as default.
Click on "Review + create", check that the network gateway has the parameters as shown below, and click on the "Create" button to finish.
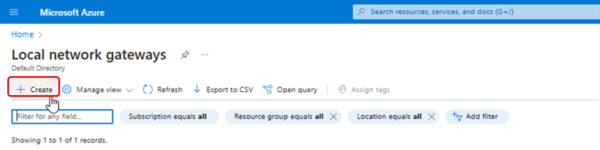
Create a local network Gateway
In the search bar, look for "Local Network Gateways" and click on "Create".
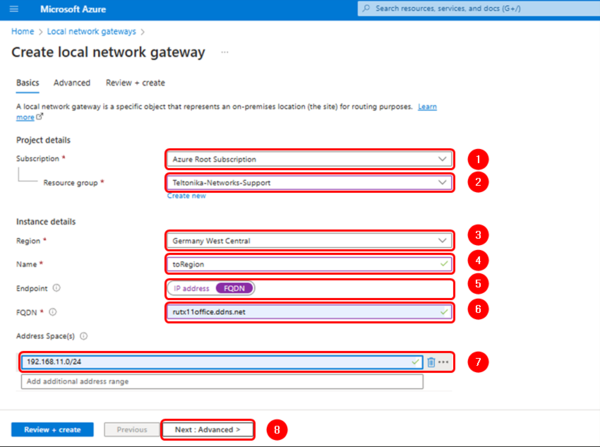
Fill in the configuration fields accordingly and add the remote router address space (LAN network) and the FQDN if the router does not have a public IP address on its WAN interface.
Projects details
- Suscription: Your suscription.
- Resource Group: Your resource group.
Instance details
- Region: Your prefered Region.
- Name: toRegion.
- Endpoint: FQDN.
- FQDN: the fully qualified domain name of the router's remote connection.
- Address Space: The router's LAN network(s)
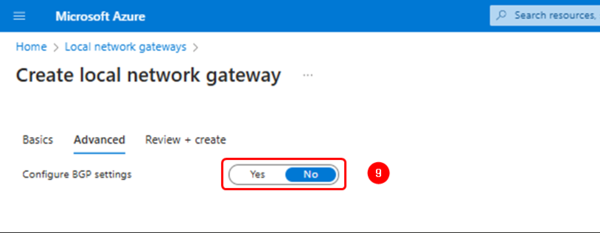
- Configure BGP settings: No.
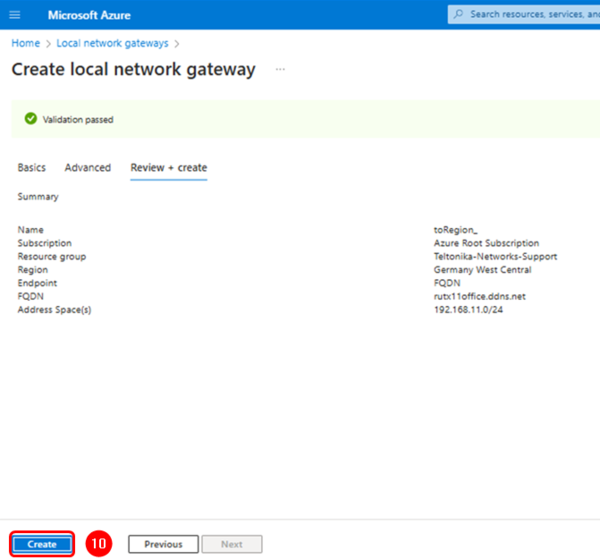
Verify the configuration and click on "Create" to finish.
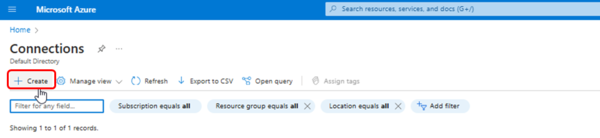
Create a connection
Search for "Connections" and create a new one:
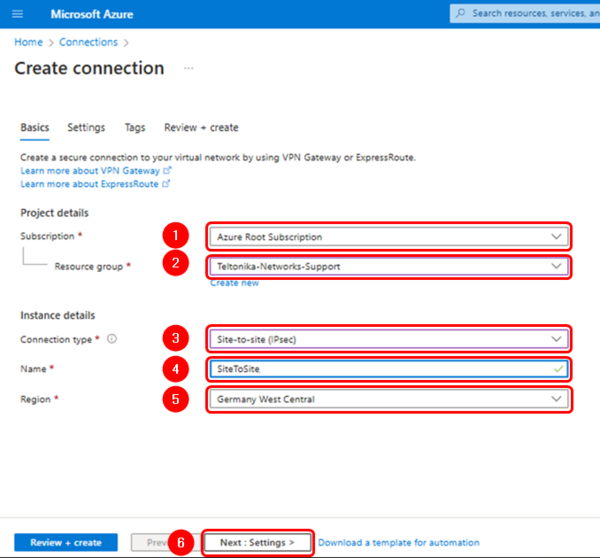
Complete the connection settings using the information and images below as reference:
Projects details
- Suscription: Your suscription.
- Resource Group: Your resource group.
Instance details
- Connection type: Site-to-Site (IPsec).
- Name: SiteToSite.
- Region: Your prefered Region (It must match the one selected above).
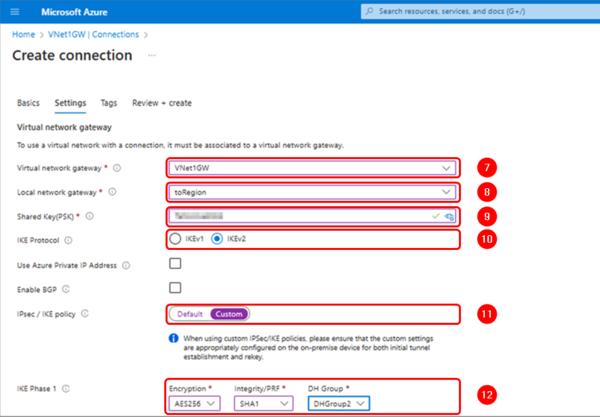
Virtual network Gateway
- Virtual network gateway: Vnet1GW.
- Local network gateway: toRegion.
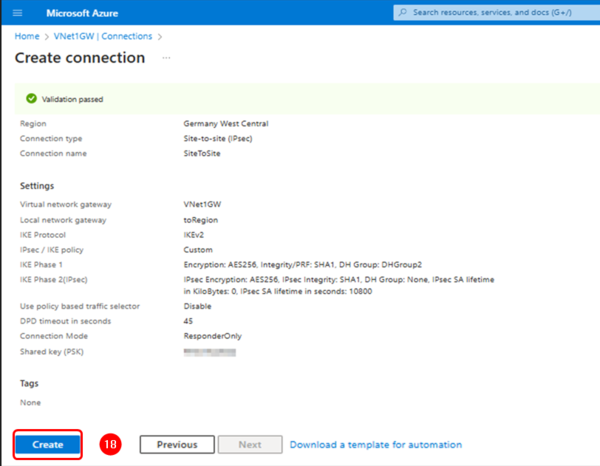
- IKE Protocol: IKEv2.
- Use Azure Private IP Address: Unchecked.
- IPsec/IKE policy: Custom.
- IKE Phase 1: Encryption: AES256 ; Integrity/PRF: SHA1 ; DH Group: DHGroup2
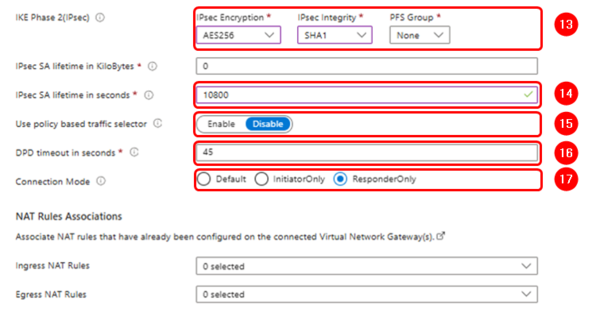
- IKE Phase 2: Encryption: AES256 ; IPsec Integrity: SHA1 ; PFS Group: None
- IPsec SA lifetime in KiloBytes: 0.
- IPsec SA lifetime in seconds: 10800.
- Use policy based traffic selector: Disable.
- DPD timeout in seconds: 45.
- Connection mode Default or ResponderOnly.
NAT Rules Associations
- Ingress NAT Rules: 0 selected.
- Egress NAT Rules: 0 selected.
Note: You can use different crypto proposals; however, you must ensure that they match on the router.
Note: the tag field can be leaved empty.
Check that the parameters match and click on "Create"
Teltonika device configuration
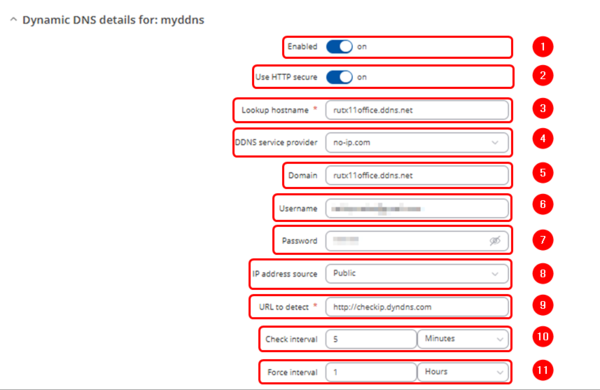
DDNS configuration
Log into the router via WebUI.
In case you don’t have a public IP address on the WAN interface, you can enable the Dynamic DNS service as explained here DDNS Configuration Examples
Path: WebUI > Services > Dynamic DNS.
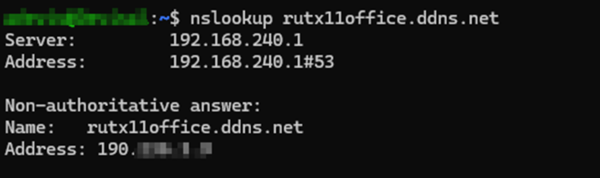
After finishing the configuration, you should get the public IP address of the created domain.