OpenVPN Access Control
Introduction
In this example, we will configure an OpenVPN server, will let Client1 and Client2 communicate, while isolating Client3 to only be able to communicate with OpenVPN server
Generating certificates for an OpenVPN server
1)Navigate to System -> Administration -> Certificates
2)Generate 2 certificates with a keysize 1024:
2.1) CA
2.2) Server
3) In Certificate Manager download Server certificate

For any OpenVPN clients, You will need to generate “Client” certificates, download certificate and key, and send them to the client
Creating an OpenVPN server
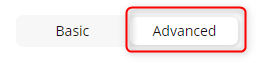
1) Connect to WebUI and enable Advanced mode
2) Navigate to Services -> VPN -> OpenVPN
3) Add a new OpenVPN instance with a Server role
4) Create an OpenVPN server with these settings
Virtual network IP address – 10.0.0.0
Virtual network netmask – 255.255.255.224
Client to client – disabled
Certificate files from device - on
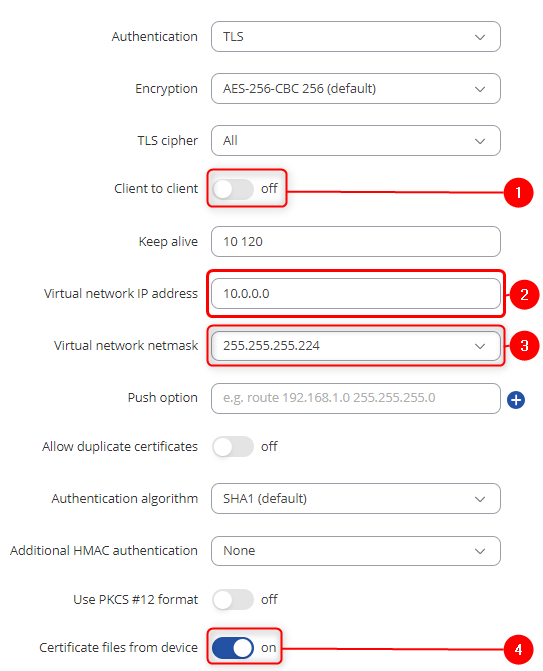
5) Press "Save & Apply", enable OpenVPN server and check if the server is online
Connecting clients to the OpenVPN server
1) Navigate to Services -> VPN -> OpenVPN
2) Add a new OpenVPN instance with a Client role
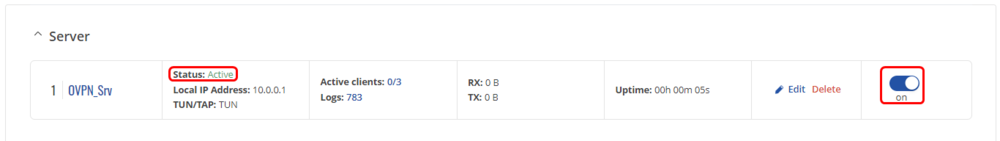
3) Create an OpenVPN client with these settings
Remote host/IP address - Public IP of the OpenVPN server's router . Remote network IP address - 10.0.0.0
Remote network netmask - 255.255.255.240
And add the certificates from the OpenVPN server - Certificate Authority, Client certificate and Client key which we downloaded in Certificate Generation step
4) Press "Save & Apply", enable OpenVPN client and check if the connection is made

5) Repeat this step for as many clients as You need. For this example, we will have 3 clients
Client to Client LAN network communication
1) On the OpenVPN server router, navigate to Services -> VPN -> OpenVPN, Press "Edit" on the server, scroll down and add TLS clients
Add clients which LAN address You want to have access to, in our case, we add all 3 clients
Common name - common name of the certificate which was generated previously
Virtual local endpoint - client’s local address in the virtual network.
Virtual remote endpoint - client’s remote address in the virtual network.
Private network - client's LAN subnet
Covered network - Which LAN subnet should clients be able to communicate with in the OpenVPN server
This step should be done on OpenVPN server and all clients that want their LAN subnets be accessible and to access other client's LAN subnets
1) Navigate to Network -> Firewall -> General settings -> Zones and set OpenVPN zone to forward traffic to LAN
This step should be done on all clients that want their LAN subnets be accessible and to access other client's LAN subnets
1) Create a route to other client LAN networks using WebUI or CLI. To create route from client 1's LAN to client 2's LAN using CLI use this command
ip route add 192.168.20.0/24 via 10.0.0.6
Controlling access with firewall
1) Navigate to Network -> Firewall -> Access Control
2) Create a new deny rule. In this example, we are denying Client 3 from accessing any other clients and their LAN networks
Source interface - OpenVPN
Destination interface - OpenVPN
Source IP - OpenVPN remote IP and LAN subnet of client 3
Destination IP - other client OpenVPN remote endpoints and LAN subnets
This rule will deny all traffic from Client 3 to other clients, but will not interact with traffic, if it's destination is OpenVPN server or it's LAN subnet
