Difference between revisions of "OpenVPN configuration examples"
| Line 48: | Line 48: | ||
===Configuration=== | ===Configuration=== | ||
---- | ---- | ||
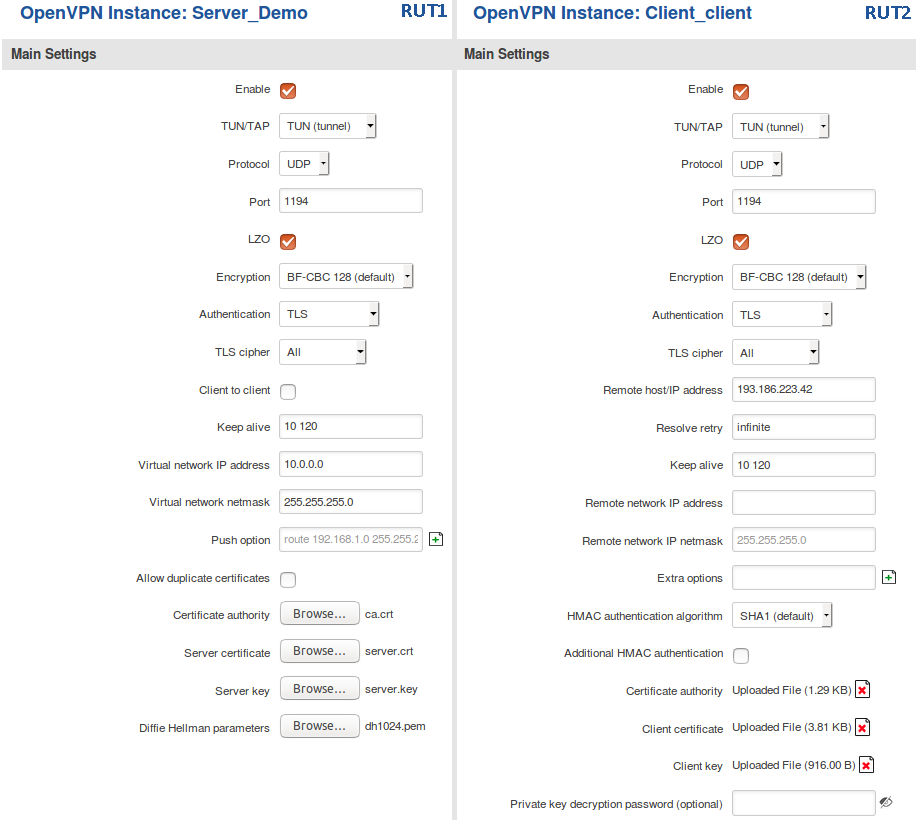
| − | Now we can start configuring OpenVPN Server and Client instances. For this example we will be creating a TUN (Tunnel) type connection that uses the UDP protocol for data transfer and TLS for Authentication. We will be using two RUT routers: '''RUT1''' (Server; LAN IP: 192.168.1.1; WAN (Public static) IP: 193.186.223.42) and '''RUT2''' (Client; LAN IP: 192.168.2.1): | + | Now we can start configuring OpenVPN Server and Client instances. For this example we will be creating a TUN (Tunnel) type connection that uses the UDP protocol for data transfer and TLS for Authentication. We will be using two RUT routers: '''RUT1''' ('''Server'''; LAN IP: '''192.168.1.1'''; WAN (Public static) IP: '''193.186.223.42''') and '''RUT2''' ('''Client'''; LAN IP: '''192.168.2.1'''); that will be connected into virtual network (with the virtual address: '''10.0.0.0'''): |
[[File:Tls client server.png]] | [[File:Tls client server.png]] | ||
| + | |||
| + | To sum up, just make sure the Server and the Clients use the same parameters (same authentication, same port, same protocol, etc.). Another important aspect is the '''Virtual network IP address''' (10.0.0.0 in this case). The Server and the connected Clients will be given IP address that belong to this network. If you're creating an exceptionally large network, you might want to change the '''Virtual network netmask'''. | ||
| + | |||
| + | From the Client side, make sure to enter the correct '''Remote host/IP address''' (193.186.223.42 in this case). This is the Server's Public IP address, not the virtual IP address. | ||
==Static key Authentication== | ==Static key Authentication== | ||
Revision as of 10:35, 9 March 2018
OpenVPN is an open-source software application that implements virtual private network (VPN) techniques for creating secure point-to-point or site-to-site connections in routed or bridged configurations and remote access facilities.
Summary
This article contains various OpenVPN configuration examples that require more in depth explanations in order to achieve a successful configuration. All of the examples given concern two or more RUT routers. For more basic explanations on the OpenVPN WebUI section, visit our VPN manual page.
OpenVPN configuration type
Before configuring anything you should first know what type of OpenVPN connection suits your needs the best. The key things to be considered here are the type of connection (TUN (tunnel) or TAP (bridged)), the data transfer protocol (User Datagram Protocol (UDP) or Transmission Control Protocol (TCP)) and authentication (TLS or Static key). Here is a short overview of the differences:
- Type
- TUN (tunnel) - simulates a network layer device and it operates with layer 3 packets like IP packets. TUN is used for routing and connecting multiple clients to a single server.
- TAP (bridged) - simulates a link layer device and it operates with layer 2 packets like Ethernet frames. TAP is used for creating a network bridge between 'two Ethernet segments in different locations.
- Protocol
- UDP - is used by apps to deliver a faster stream of information by doing away with error-checking.
- TCP - a suite of protocols used by devices to communicate over the Internet and most local networks. It provides apps a way to deliver (and receive) an ordered and error-checked stream of information packets over the network.
- Authentication
- TLS - uses SSL/TLS + certificates for authentication and key exchange.
- Static key - use a pre-shared Static key.
An overview of most of these types is provided in this article. Concerning TCP vs UDP, we will be using UDP for all examples. Choosing between TCP and UDP doesn't affect the rest of the configuration, so you can still follow the given examples no matter which protocol you are using. Simply choose the one that suits your purposes.
TLS Authentication
This section provides a guide on how to configure a successful OpenVPN connection between an OpenVPN Client and Server, using the TLS Authentication method on RUT routers.
Generating TLS certificates/keys
A connection that uses TLS requires multiple certificates and keys for authentication:
* Server ** The root certificate file (Cetificate Authority) ** Server certificate ** Server key ** Diffie Hellman Parameters
* Client ** The root certificate file (Cetificate Authority) ** Client certificate ** Client key
Detailed instruction on how to obtain these files can be found here.
Once you have all the required files, continue following this section of the guide.
Configuration
Now we can start configuring OpenVPN Server and Client instances. For this example we will be creating a TUN (Tunnel) type connection that uses the UDP protocol for data transfer and TLS for Authentication. We will be using two RUT routers: RUT1 (Server; LAN IP: 192.168.1.1; WAN (Public static) IP: 193.186.223.42) and RUT2 (Client; LAN IP: 192.168.2.1); that will be connected into virtual network (with the virtual address: 10.0.0.0):
To sum up, just make sure the Server and the Clients use the same parameters (same authentication, same port, same protocol, etc.). Another important aspect is the Virtual network IP address (10.0.0.0 in this case). The Server and the connected Clients will be given IP address that belong to this network. If you're creating an exceptionally large network, you might want to change the Virtual network netmask.
From the Client side, make sure to enter the correct Remote host/IP address (193.186.223.42 in this case). This is the Server's Public IP address, not the virtual IP address.
Static key Authentication
This section provides a guide on how to configure a successful OpenVPN connection between an OpenVPN Client and Server, using the Static key Authentication method on RUT routers.
Creating a Static key
First, lets create a Static key.