Difference between revisions of "Template:Networking rutos configuration example openvpn bridge wifi ap use case"
| (56 intermediate revisions by the same user not shown) | |||
| Line 3: | Line 3: | ||
<th width=325; style="border-bottom: 1px solid white;></th> | <th width=325; style="border-bottom: 1px solid white;></th> | ||
<th width=820; style="border-bottom: 1px solid white;" rowspan=2;> | <th width=820; style="border-bottom: 1px solid white;" rowspan=2;> | ||
| − | [[File: | + | [[File:Networking_rutos_configuration_example_openvpn_bridge_use_case_topology_v1.png|border|class=tlt-border|750px|right]]</th> |
</tr> | </tr> | ||
<tr> | <tr> | ||
| Line 17: | Line 17: | ||
'''Prerequisites''': | '''Prerequisites''': | ||
| − | * Two RUTX routers | + | * Two RUTX routers (only the versions, which have WiFi) |
| − | * A Public Static or Public Dynamic IP | + | * A Public Static or Public Dynamic IP address |
* An end device to configure the router (PC, Laptop, Tablet, Smartphone) | * An end device to configure the router (PC, Laptop, Tablet, Smartphone) | ||
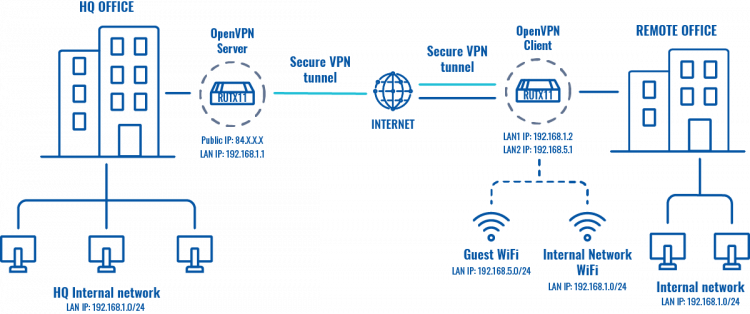
The topology above depicts the OpenVPN scheme. The router with the Public IP address ('''RUTX''') acts as the '''OpenVPN server''' and other '''RUTX''' acts as '''client'''. OpenVPN connects the networks of '''HQ Office''' and '''Remote Office'''. '''Remote Office''' will also have a separate WiFi AP for guests. | The topology above depicts the OpenVPN scheme. The router with the Public IP address ('''RUTX''') acts as the '''OpenVPN server''' and other '''RUTX''' acts as '''client'''. OpenVPN connects the networks of '''HQ Office''' and '''Remote Office'''. '''Remote Office''' will also have a separate WiFi AP for guests. | ||
| − | When the scheme is realized, remote office workers will be able to reach HQ’s internal network with all internal systems by connecting to the router via LAN port or by connecting to WiFi AP, which is used for work. All | + | When the scheme is realized, remote office workers will be able to reach HQ’s internal network with all internal systems by connecting to the router via LAN port or by connecting to a WiFi AP, which is used for work. All traffic apart guest WiFi is going to travel through VPN tunnel. Guest network traffic will go directly to WAN, it will give visitors access to the Internet connection, but nothing else making your company a lot more secure. |
==Configuring HQ office router== | ==Configuring HQ office router== | ||
| Line 40: | Line 40: | ||
<tr> | <tr> | ||
<th width=355; style="border-bottom: 1px solid white;></th> | <th width=355; style="border-bottom: 1px solid white;></th> | ||
| − | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File: | + | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:Networking_rutos_configuration_example_openvpn_bridge_wifi_ap_use_case_1_v1.png|border|class=tlt-border|728px|right]]</th> |
</tr> | </tr> | ||
<tr> | <tr> | ||
| Line 58: | Line 58: | ||
<tr> | <tr> | ||
<th width=355; style="border-bottom: 1px solid white;></th> | <th width=355; style="border-bottom: 1px solid white;></th> | ||
| − | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File: | + | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:Networking_rutos_configuration_example_openvpn_bridge_wifi_ap_use_case_2_v1.png|border|class=tlt-border|728px|right]]</th> |
</tr> | </tr> | ||
<tr> | <tr> | ||
| Line 86: | Line 86: | ||
<tr> | <tr> | ||
<th width=355; style="border-bottom: 1px solid white;></th> | <th width=355; style="border-bottom: 1px solid white;></th> | ||
| − | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:Winscp login instructions.PNG| | + | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:Winscp login instructions.PNG|border|class=tlt-border|728px|right]]</th> |
</tr> | </tr> | ||
<tr> | <tr> | ||
| Line 102: | Line 102: | ||
<tr> | <tr> | ||
<th width=355; style="border-bottom: 1px solid white;></th> | <th width=355; style="border-bottom: 1px solid white;></th> | ||
| − | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:Winscp interface example.PNG| | + | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:Winscp interface example.PNG|border|class=tlt-border|728px|right]]</th> |
</tr> | </tr> | ||
<tr> | <tr> | ||
| Line 117: | Line 117: | ||
<tr> | <tr> | ||
<th width=355; style="border-bottom: 1px solid white;></th> | <th width=355; style="border-bottom: 1px solid white;></th> | ||
| − | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File: | + | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:Networking_rutx_configuration_example_openvpn_bridge_use_case_4_v2.png|border|class=tlt-border|728px|right]]</th> |
</tr> | </tr> | ||
<tr> | <tr> | ||
<td style="border-bottom: 1px solid white> | <td style="border-bottom: 1px solid white> | ||
| − | + | Go to '''Services → VPN → OpenVPN'''. There create a new configuration by writing '''New configuration name''' (you can type anything you want), selecting role '''Server''' and pressing '''Add''' button. It should appear after a few seconds. Then press '''Edit'''. | |
</td> | </td> | ||
</tr> | </tr> | ||
| Line 131: | Line 131: | ||
<tr> | <tr> | ||
<th width=355; style="border-bottom: 1px solid white;></th> | <th width=355; style="border-bottom: 1px solid white;></th> | ||
| − | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File: | + | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:Networking_rutx_configuration_example_openvpn_bridge_use_case_5_v2.png|border|class=tlt-border|728px|right]]</th> |
</tr> | </tr> | ||
<tr> | <tr> | ||
| Line 143: | Line 143: | ||
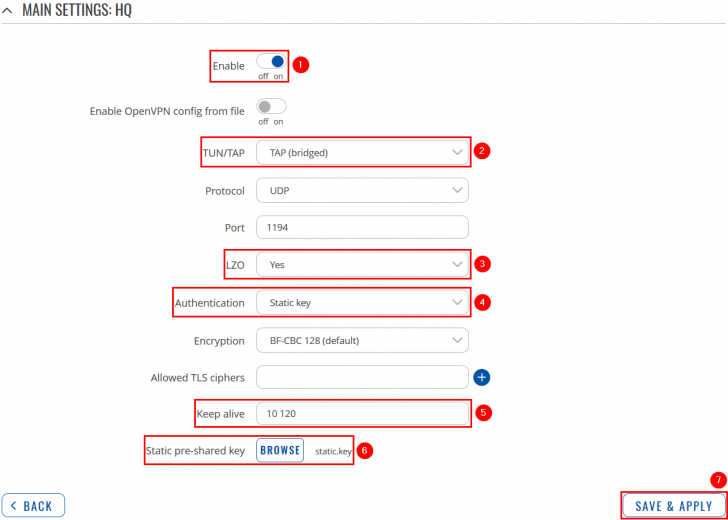
<li>Select '''Authentication: Static key'''.</li> | <li>Select '''Authentication: Static key'''.</li> | ||
<li>Add '''Keep alive''' interval: '''10 120'''.</li> | <li>Add '''Keep alive''' interval: '''10 120'''.</li> | ||
| − | <li>Upload '''Static pre-shared key''' | + | <li>Upload '''Static pre-shared key'''.</li> |
<li>'''Save''' the changes.</li> | <li>'''Save''' the changes.</li> | ||
</ol> | </ol> | ||
| Line 152: | Line 152: | ||
==Configuring remote office router== | ==Configuring remote office router== | ||
| − | ===LAN=== | + | Before you start configuring the remote office router, set a static IP address on the device you are configuring the router with (e.g. 192.168.1.10). You can find instructions on how to do that here: |
| + | |||
| + | [[Setting_up_a_Static_IP_address_on_a_Ubuntu_16.04_PC|Ubuntu]] | ||
| + | |||
| + | [[Setting up a Static IP address on a Windows 10 PC|Windows]] | ||
| + | |||
| + | <span style="color: red;">'''Note: make sure to switch back to automatic DNS and IP address obtaining when you are done configuring the router.'''</span> | ||
| + | |||
| + | ===OpenVPN=== | ||
| + | ---- | ||
| + | |||
| + | ====LAN==== | ||
---- | ---- | ||
| Line 158: | Line 169: | ||
<tr> | <tr> | ||
<th width=355; style="border-bottom: 1px solid white;></th> | <th width=355; style="border-bottom: 1px solid white;></th> | ||
| − | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File: | + | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:Networking_rutx_configuration_example_openvpn_bridge_use_case_8_v2.png|border|class=tlt-border|728px|right]]</th> |
</tr> | </tr> | ||
<tr> | <tr> | ||
<td style="border-bottom: 1px solid white> | <td style="border-bottom: 1px solid white> | ||
| − | Go to '''Network → | + | Go to '''Network → Interfaces''' and press '''Edit''' next to your LAN interface: |
</td> | </td> | ||
</tr> | </tr> | ||
| Line 172: | Line 183: | ||
<tr> | <tr> | ||
<th width=355; style="border-bottom: 1px solid white;></th> | <th width=355; style="border-bottom: 1px solid white;></th> | ||
| − | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File: | + | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:Networking_rutx_configuration_example_openvpn_bridge_use_case_9_v2.png|border|class=tlt-border|728px|right]]</th> |
</tr> | </tr> | ||
<tr> | <tr> | ||
| Line 187: | Line 198: | ||
</table> | </table> | ||
| − | |||
| − | |||
====Configuring OpenVPN client==== | ====Configuring OpenVPN client==== | ||
---- | ---- | ||
| Line 195: | Line 204: | ||
<tr> | <tr> | ||
<th width=355; style="border-bottom: 1px solid white;></th> | <th width=355; style="border-bottom: 1px solid white;></th> | ||
| − | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File: | + | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:Networking_rutx_configuration_example_openvpn_bridge_use_case_6_v2.png|border|class=tlt-border|728px|right]]</th> |
</tr> | </tr> | ||
<tr> | <tr> | ||
<td style="border-bottom: 1px solid white> | <td style="border-bottom: 1px solid white> | ||
| − | Go to '''Services → VPN → OpenVPN'''. There create a new configuration by | + | Go to '''Services → VPN → OpenVPN'''. There create a new configuration by writing '''New configuration name''' (you can type anything you want), selecting role '''Client''' and pressing '''Add''' button. It should appear after a few seconds. Then press '''Edit'''. |
</td> | </td> | ||
</tr> | </tr> | ||
| Line 209: | Line 218: | ||
<tr> | <tr> | ||
<th width=355; style="border-bottom: 1px solid white;></th> | <th width=355; style="border-bottom: 1px solid white;></th> | ||
| − | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File: | + | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:Networking_rutx_configuration_example_openvpn_bridge_use_case_7_v3.png|border|class=tlt-border|728px|right]]</th> |
</tr> | </tr> | ||
<tr> | <tr> | ||
| Line 222: | Line 231: | ||
<li>Write '''Remote host/IP address''' (RUTX OpenVPN server public IP).</li> | <li>Write '''Remote host/IP address''' (RUTX OpenVPN server public IP).</li> | ||
<li>Add '''Keep alive''' interval: '''10 120'''.</li> | <li>Add '''Keep alive''' interval: '''10 120'''.</li> | ||
| − | <li>Upload '''Static pre-shared key''' (use the . | + | <li>Upload '''Static pre-shared key'''.</li> |
| + | <li>'''Save''' the changes.</li> | ||
| + | </ol> | ||
| + | </td> | ||
| + | </tr> | ||
| + | </table> | ||
| + | |||
| + | ===Guest WiFi=== | ||
| + | ---- | ||
| + | |||
| + | ====Creating a new WiFi AP==== | ||
| + | ---- | ||
| + | |||
| + | <table class="nd-othertables_2"> | ||
| + | <tr> | ||
| + | <th width=355; style="border-bottom: 1px solid white;></th> | ||
| + | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:Networking_rutos_configuration_example_openvpn_bridge_use_case_10_v1.png|border|class=tlt-border|728px|right]]</th> | ||
| + | </tr> | ||
| + | <tr> | ||
| + | <td style="border-bottom: 1px solid white> | ||
| + | Go to '''Network → Wireless'''. There create a new '''WiFi Access Point''' by pressing '''Add''' button (you can use either, 2.4GHz or 5GHz WiFi). Then you will be forwarded to the configuration window. | ||
| + | </td> | ||
| + | </tr> | ||
| + | </table> | ||
| + | |||
| + | ---- | ||
| + | |||
| + | <table class="nd-othertables_2"> | ||
| + | <tr> | ||
| + | <th width=355; style="border-bottom: 1px solid white;></th> | ||
| + | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:Networking_rutos_configuration_example_openvpn_bridge_use_case_11_v1.png|border|class=tlt-border|728px|right]]</th> | ||
| + | </tr> | ||
| + | <tr> | ||
| + | <td style="border-bottom: 1px solid white> | ||
| + | Apply the following steps: | ||
| + | |||
| + | <ol> | ||
| + | <li>Disable '''LAN'''.</li> | ||
| + | <li>Create a new '''Network''' for guest WiFi.</li> | ||
| + | <li>'''Save''' the changes.</li> | ||
| + | </ol> | ||
| + | </td> | ||
| + | </tr> | ||
| + | </table> | ||
| + | |||
| + | ---- | ||
| + | |||
| + | <table class="nd-othertables_2"> | ||
| + | <tr> | ||
| + | <th width=355; style="border-bottom: 1px solid white;></th> | ||
| + | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:Networking_rutos_configuration_example_openvpn_bridge_use_case_12_v1.png|border|class=tlt-border|728px|right]]</th> | ||
| + | </tr> | ||
| + | <tr> | ||
| + | <td style="border-bottom: 1px solid white> | ||
| + | Now go to '''Network → Interfaces''' and press '''Edit''' next to your newly created LAN interface: | ||
| + | </td> | ||
| + | </tr> | ||
| + | </table> | ||
| + | |||
| + | ---- | ||
| + | |||
| + | <table class="nd-othertables_2"> | ||
| + | <tr> | ||
| + | <th width=355; style="border-bottom: 1px solid white;></th> | ||
| + | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:Networking_rutos_configuration_example_openvpn_bridge_use_case_13_v1.png|border|class=tlt-border|728px|right]]</th> | ||
| + | </tr> | ||
| + | <tr> | ||
| + | <td style="border-bottom: 1px solid white> | ||
| + | Apply the following steps: | ||
| + | |||
| + | <ol> | ||
| + | <li>Set '''Protocol''' to '''Static'''.</li> | ||
| + | <li>Press '''Switch Protocol''' and then more configuration options will appear.</li> | ||
| + | </ol> | ||
| + | </td> | ||
| + | </tr> | ||
| + | </table> | ||
| + | |||
| + | ---- | ||
| + | |||
| + | <table class="nd-othertables_2"> | ||
| + | <tr> | ||
| + | <th width=355; style="border-bottom: 1px solid white;></th> | ||
| + | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:Networking_rutos_configuration_example_openvpn_bridge_use_case_14_v1.png|border|class=tlt-border|728px|right]]</th> | ||
| + | </tr> | ||
| + | <tr> | ||
| + | <td style="border-bottom: 1px solid white> | ||
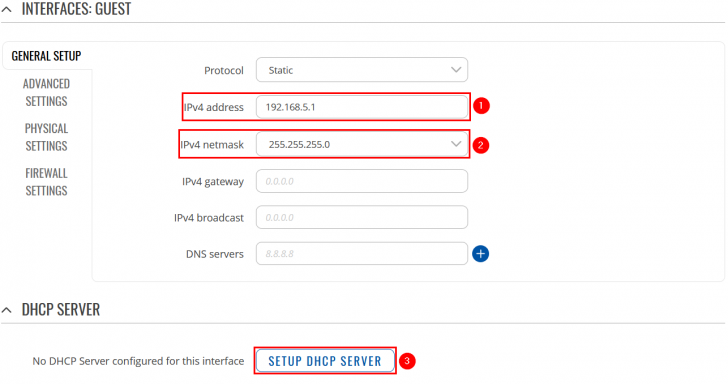
| + | Now apply the following steps: | ||
| + | |||
| + | <ol> | ||
| + | <li>Set '''IPv4 Address''' to '''192.168.5.1'''.</li> | ||
| + | <li>Select '''IPv4 netmask: 255.255.255.0'''.</li> | ||
| + | <li>Press '''Setup DHCP Server''', after that more configuration options will appear, but you can leave those as default or change it to your own liking.</li> | ||
| + | <li>'''Save''' the changes.</li> | ||
| + | </ol> | ||
| + | </td> | ||
| + | </tr> | ||
| + | </table> | ||
| + | |||
| + | ====Editing Firewall rules==== | ||
| + | ---- | ||
| + | |||
| + | <table class="nd-othertables_2"> | ||
| + | <tr> | ||
| + | <th width=355; style="border-bottom: 1px solid white;></th> | ||
| + | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:Networking_rutos_configuration_example_openvpn_bridge_use_case_15_v1.png|border|class=tlt-border|728px|right]]</th> | ||
| + | </tr> | ||
| + | <tr> | ||
| + | <td style="border-bottom: 1px solid white> | ||
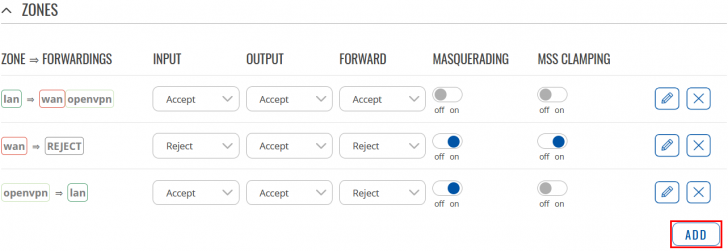
| + | Navigate to '''Network → Firewall → General Settings'''. There create a new '''Zone''' rule by pressing '''Add''' button. Then you will be forwarded to the configuration window. | ||
| + | </td> | ||
| + | </tr> | ||
| + | </table> | ||
| + | |||
| + | ---- | ||
| + | |||
| + | <table class="nd-othertables_2"> | ||
| + | <tr> | ||
| + | <th width=355; style="border-bottom: 1px solid white;></th> | ||
| + | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:Networking_rutos_configuration_example_openvpn_bridge_use_case_16_v1.png|border|class=tlt-border|728px|right]]</th> | ||
| + | </tr> | ||
| + | <tr> | ||
| + | <td style="border-bottom: 1px solid white> | ||
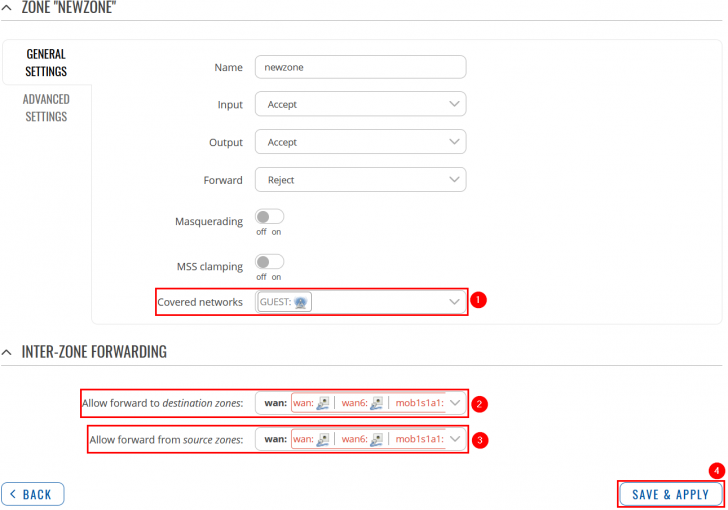
| + | Now apply the following steps: | ||
| + | <ol> | ||
| + | <li>At '''Covered Networks''' section select your newly created LAN interface.</li> | ||
| + | <li>Set WAN at '''Allow Forward To Destination Zones''' section.</li> | ||
| + | <li>Set WAN at '''Allow Forward From Destination Zones''' section.</li> | ||
| + | <li>'''Save''' the changes.</li> | ||
| + | </ol> | ||
| + | </td> | ||
| + | </tr> | ||
| + | </table> | ||
| + | |||
| + | ---- | ||
| + | |||
| + | <table class="nd-othertables_2"> | ||
| + | <tr> | ||
| + | <th width=355; style="border-bottom: 1px solid white;></th> | ||
| + | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:Networking_rutos_configuration_example_openvpn_bridge_use_case_17_v1.png|border|class=tlt-border|728px|right]]</th> | ||
| + | </tr> | ||
| + | <tr> | ||
| + | <td style="border-bottom: 1px solid white> | ||
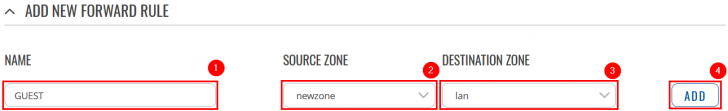
| + | Go to '''Network → Firewall → Traffic Rules'''. There create a new '''Forward''' rule by writing a '''Name''', selecting '''Source Zone (newzone)''', '''Destination Zone (lan)''' and pressing '''Add''' button. Then you will be forwarded to the configuration window. | ||
| + | </td> | ||
| + | </tr> | ||
| + | </table> | ||
| + | |||
| + | ---- | ||
| + | |||
| + | <table class="nd-othertables_2"> | ||
| + | <tr> | ||
| + | <th width=355; style="border-bottom: 1px solid white;></th> | ||
| + | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:Networking_rutos_configuration_example_openvpn_bridge_use_case_18_v1.png|border|class=tlt-border|728px|right]]</th> | ||
| + | </tr> | ||
| + | <tr> | ||
| + | <td style="border-bottom: 1px solid white> | ||
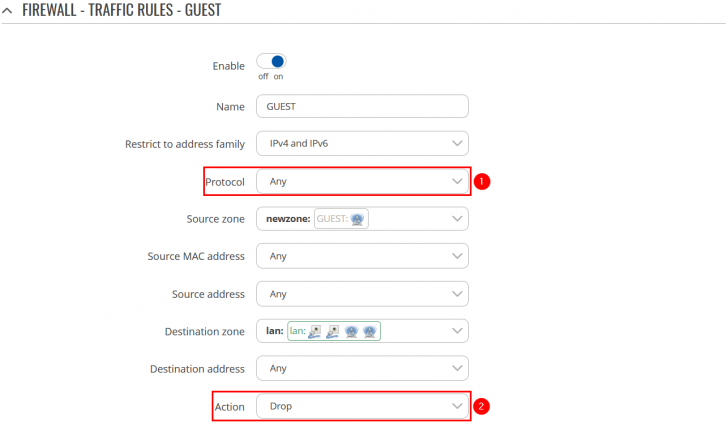
| + | Now apply the following steps: | ||
| + | <ol> | ||
| + | <li>Set '''Protocol''' to '''Any'''.</li> | ||
| + | <li>Select '''Action: Drop'''.</li> | ||
<li>'''Save''' the changes.</li> | <li>'''Save''' the changes.</li> | ||
</ol> | </ol> | ||
| Line 233: | Line 402: | ||
<table class="nd-othertables_2"> | <table class="nd-othertables_2"> | ||
<tr> | <tr> | ||
| − | <th width= | + | <th width=355; style="border-bottom: 1px solid white;></th> |
| − | <th width= | + | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:Networking_rut_configuration_example_openvpn_bridge_use_case_9_v2.png|border|class=tlt-border|728px|right]]</th> |
| + | </tr> | ||
| + | <tr> | ||
| + | <td style="border-bottom: 1px solid white> | ||
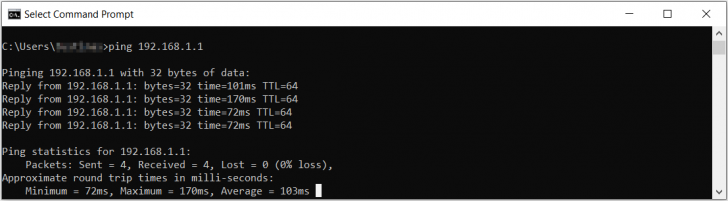
| + | Remote office should now be able to access HQ network resources. To verify the connection you can ping remote RUTX (HQ server) LAN IP and if you get a reply, you have successfully connected to HQ‘s internal network. Also, all LAN addresses, that belong to the work network (192.168.1.0/24), should now be leased to LAN devices by HQ router. | ||
| + | </td> | ||
| + | </tr> | ||
| + | </table> | ||
| + | |||
| + | ---- | ||
| + | <table class="nd-othertables_2"> | ||
| + | <tr> | ||
| + | <th width=355; style="border-bottom: 1px solid white;></th> | ||
| + | <th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:Networking_rutos_configuration_example_openvpn_bridge_use_case_19_v2.png|border|class=tlt-border|728px|right]]</th> | ||
</tr> | </tr> | ||
<tr> | <tr> | ||
<td style="border-bottom: 1px solid white> | <td style="border-bottom: 1px solid white> | ||
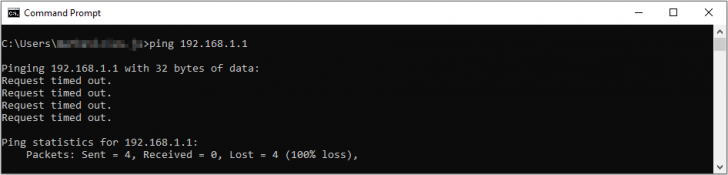
| − | + | In order to check the guest WiFi, you simply need to connect to the newly created WiFi AP, then check whether you have internet connectivity and try to ping OpenVPN server LAN IP - if everything is set up correctly, you should not be able to do that. | |
</td> | </td> | ||
</tr> | </tr> | ||
</table> | </table> | ||
Latest revision as of 17:31, 21 July 2020
|
|
Configuration overview and prerequisites
Prerequisites:
- Two RUTX routers (only the versions, which have WiFi)
- A Public Static or Public Dynamic IP address
- An end device to configure the router (PC, Laptop, Tablet, Smartphone)
The topology above depicts the OpenVPN scheme. The router with the Public IP address (RUTX) acts as the OpenVPN server and other RUTX acts as client. OpenVPN connects the networks of HQ Office and Remote Office. Remote Office will also have a separate WiFi AP for guests.
When the scheme is realized, remote office workers will be able to reach HQ’s internal network with all internal systems by connecting to the router via LAN port or by connecting to a WiFi AP, which is used for work. All traffic apart guest WiFi is going to travel through VPN tunnel. Guest network traffic will go directly to WAN, it will give visitors access to the Internet connection, but nothing else making your company a lot more secure.
Configuring HQ office router
Before you start configuring the router turn on "Advanced WebUI" mode. You can do that by clicking the "Basic" button under "Mode", which is located at the top-right corner of the WebUI.
Note: You will need to do that in both, HQ and remote office routers.
OpenVPN
Generating Static key
|
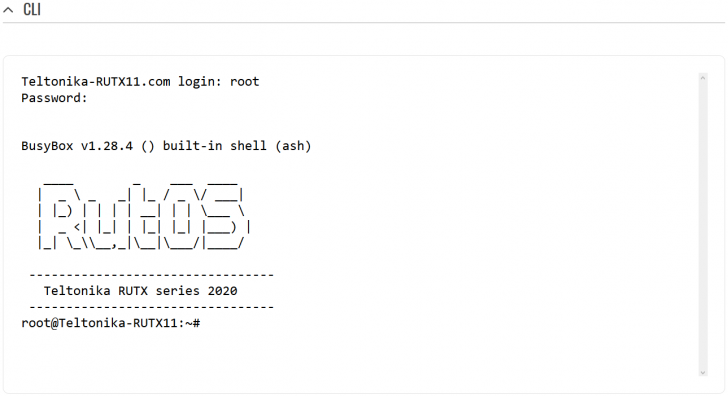
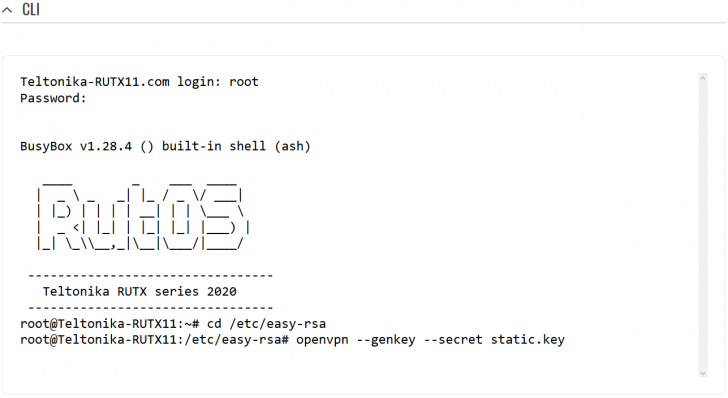
Login to the router's WebUI, navigate to the Services → CLI page and do the following:
|
|
Write the following commands to create OpenVPN Static key, which will be used for authentication: 1) cd /etc/easy-rsa 2) openvpn --genkey --secret static.key |
Extracting the key
Linux
If you are using a Linux-based OS, extracting files from the router is simple. Just go to the directory on your PC where you want to relocate the files, right click anywhere and choose the Open in Terminal option. In the Terminal command line use the Secure Copy (scp) command to copy the files from the router. The full command should look something like this:
$ scp [email protected]:/etc/easy-rsa/static.key ./
The [email protected]:/etc/easy-rsa/static.key specifies the path to where the Static key is located (replace the IP address with your router's LAN IP); the ./ denotes that you want to copy the contents to the directory you are in at the moment.
Windows
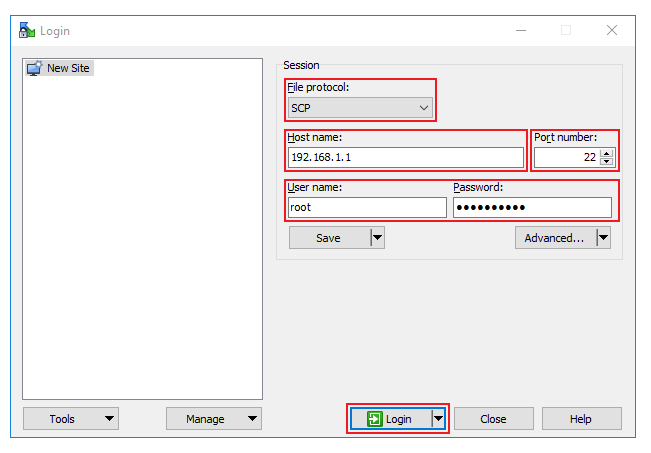
|
If you are using Windows, you can copy files from the router using WinSCP, an Open source freeware SFTP, SCP and FTP client for Windows OS. Use the same login information with WinSCP as with CLI or SSH. Please note: You must select SCP as File Protocol in WinSCP Session settings. |
|
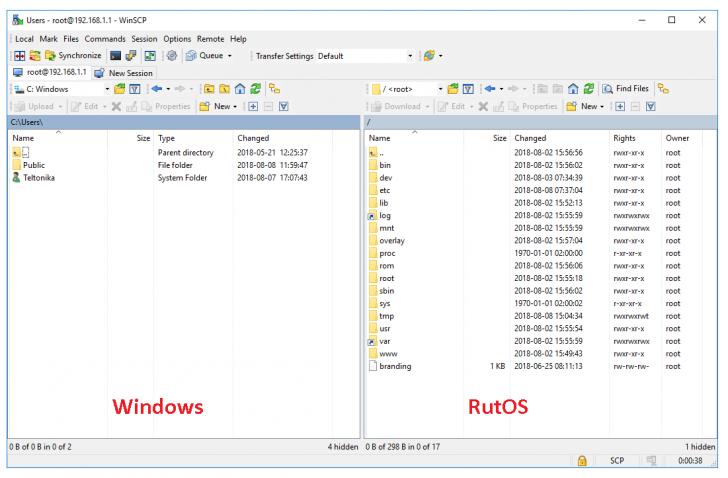
Once you've connected to the router with WinSCP, copying the files should be simple enough: just go to /etc/easy-rsa/, select the Static key file and drag it to directory on your PC where you would like to store it. |
Configuring OpenVPN server
|
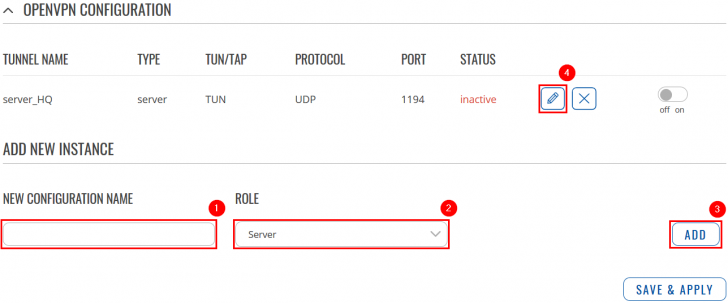
Go to Services → VPN → OpenVPN. There create a new configuration by writing New configuration name (you can type anything you want), selecting role Server and pressing Add button. It should appear after a few seconds. Then press Edit. |
|
Now apply the following configuration:
|
Configuring remote office router
Before you start configuring the remote office router, set a static IP address on the device you are configuring the router with (e.g. 192.168.1.10). You can find instructions on how to do that here:
Note: make sure to switch back to automatic DNS and IP address obtaining when you are done configuring the router.
OpenVPN
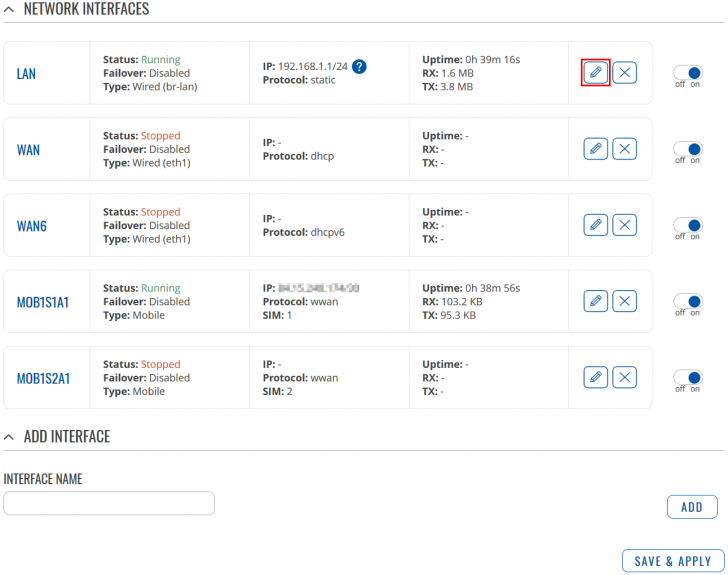
LAN
|
Go to Network → Interfaces and press Edit next to your LAN interface: |
|
Apply the following steps:
|
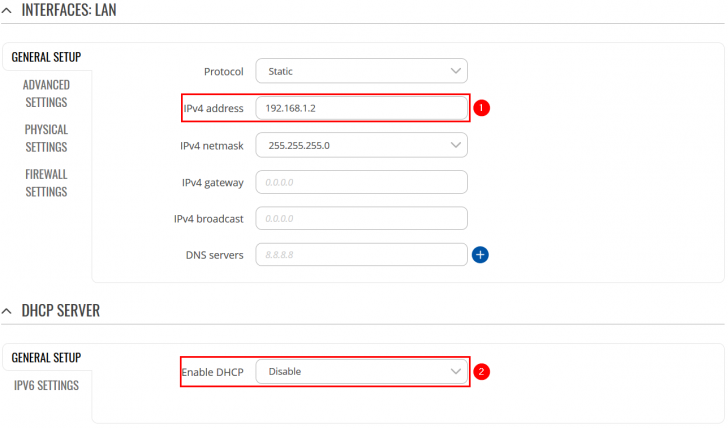
Configuring OpenVPN client
|
Go to Services → VPN → OpenVPN. There create a new configuration by writing New configuration name (you can type anything you want), selecting role Client and pressing Add button. It should appear after a few seconds. Then press Edit. |
|
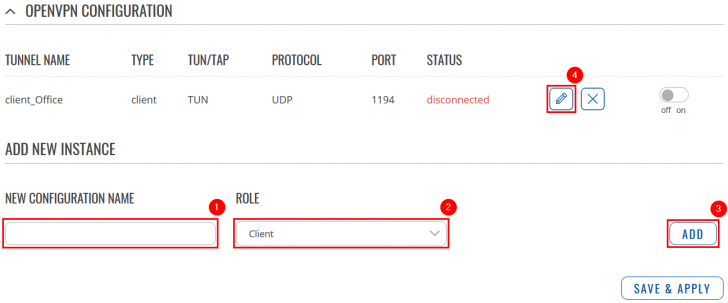
Now apply the following configuration:
|
Guest WiFi
Creating a new WiFi AP
|
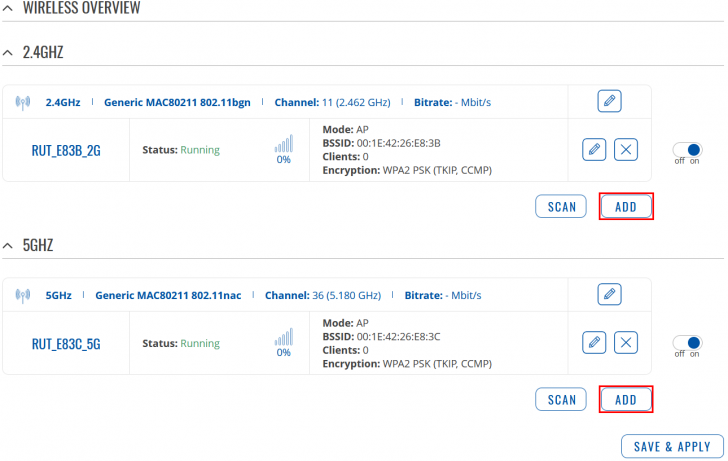
Go to Network → Wireless. There create a new WiFi Access Point by pressing Add button (you can use either, 2.4GHz or 5GHz WiFi). Then you will be forwarded to the configuration window. |
|
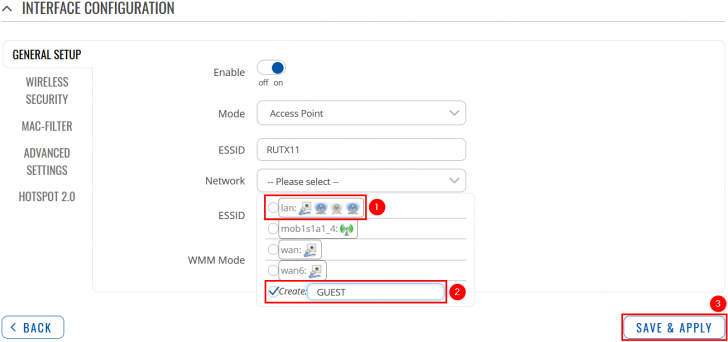
Apply the following steps:
|
|
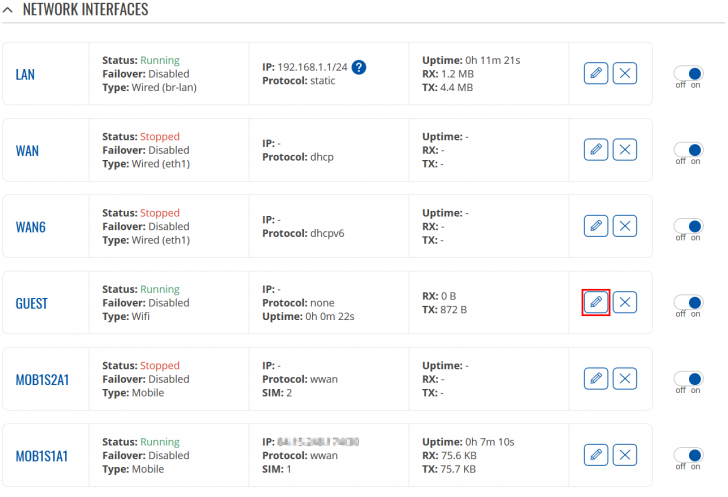
Now go to Network → Interfaces and press Edit next to your newly created LAN interface: |
|
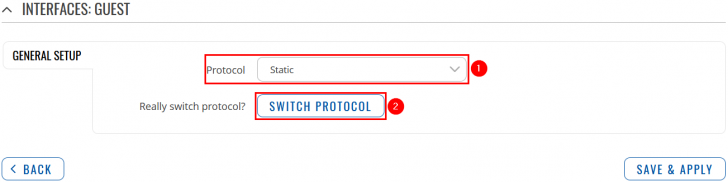
Apply the following steps:
|
|
Now apply the following steps:
|
Editing Firewall rules
|
Navigate to Network → Firewall → General Settings. There create a new Zone rule by pressing Add button. Then you will be forwarded to the configuration window. |
|
Now apply the following steps:
|
|
Go to Network → Firewall → Traffic Rules. There create a new Forward rule by writing a Name, selecting Source Zone (newzone), Destination Zone (lan) and pressing Add button. Then you will be forwarded to the configuration window. |
|
Now apply the following steps:
|
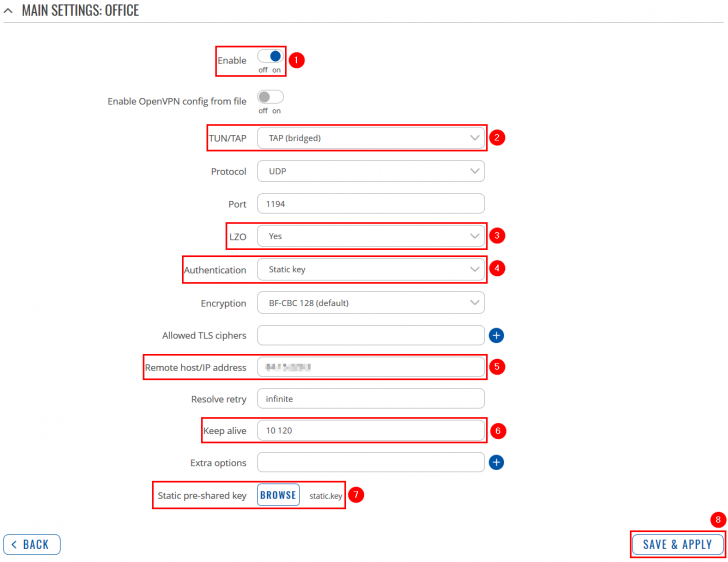
Results
|
Remote office should now be able to access HQ network resources. To verify the connection you can ping remote RUTX (HQ server) LAN IP and if you get a reply, you have successfully connected to HQ‘s internal network. Also, all LAN addresses, that belong to the work network (192.168.1.0/24), should now be leased to LAN devices by HQ router. |
|
In order to check the guest WiFi, you simply need to connect to the newly created WiFi AP, then check whether you have internet connectivity and try to ping OpenVPN server LAN IP - if everything is set up correctly, you should not be able to do that. |