Difference between revisions of "Domnev"
| Line 14: | Line 14: | ||
==Topology== | ==Topology== | ||
| + | |||
| + | [[File:IPsec TLT to TLT Topology.png|border|center|class=tlt-border|839x399px]] | ||
'''RUT1''' - RUTX12 as a '''hub'''. A hub is a server, to which our spoke will be connecting (IPsec responder). It will be our "default gateway" for the spoke device. RUTX12 has a LAN subnet of 192.168.11.0/24 configured on it, which should be reachable by the '''spoke'''. | '''RUT1''' - RUTX12 as a '''hub'''. A hub is a server, to which our spoke will be connecting (IPsec responder). It will be our "default gateway" for the spoke device. RUTX12 has a LAN subnet of 192.168.11.0/24 configured on it, which should be reachable by the '''spoke'''. | ||
| Line 173: | Line 175: | ||
==Testing the configuration== | ==Testing the configuration== | ||
| − | + | If you've followed all the steps presented above, your configuration should be finished. But as with any other configuration, it is always wise to test the setup in order to make sure that it works properly. | |
| − | + | ||
| − | + | Using the <code><span class="highlight">ipsec statusall</span></code> command we can see that IPsec tunnel is successfully established on both routers. The command output on a '''hub (RUT1)''' device: | |
| − | < | ||
<pre> | <pre> | ||
| Line 204: | Line 205: | ||
</pre> | </pre> | ||
| − | + | The same command output on '''spoke (RUT2)''' device: | |
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
<pre> | <pre> | ||
| Line 270: | Line 237: | ||
</pre> | </pre> | ||
| − | + | Also, as the hub should be reachable by spoke, we can try pinging the hub using <code><span class="highlight">ping 192.168.11.1</span></code>: | |
| − | < | ||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | </ | ||
| − | |||
== See also == | == See also == | ||
== External links == | == External links == | ||
Revision as of 12:36, 22 March 2023
The information on this page is updated in accordance with the 00.07.4 firmware version .
Introduction
Configuration overview and prerequisites
Before we begin, let's take a look at the configuration that we are attempting to achieve and the prerequisites that make it possible.
Prerequisites:
- Two RUT/RUTX series routers with RUTOS firmware;
- An end device (PC, Laptop) for configuration;
If you're having trouble finding any page or some of the parameters described here on your device's WebUI, you should turn on "Advanced WebUI" mode. You can do that by clicking the "Basic" button under "Mode," which is located at the top-right corner of the WebUI.
Topology
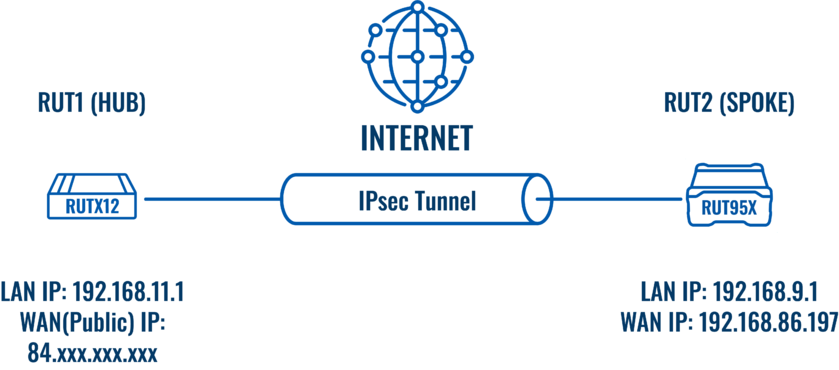
RUT1 - RUTX12 as a hub. A hub is a server, to which our spoke will be connecting (IPsec responder). It will be our "default gateway" for the spoke device. RUTX12 has a LAN subnet of 192.168.11.0/24 configured on it, which should be reachable by the spoke.
RUT2 - RUT955 as a spoke. A spoke is a client, that will be connected to the spoke (IPsec initiator). It will be connected to a hub for basic internet access. RUT955 has a LAN subnet of 192.168.9.0/24 configured on it.
RUT1 (Hub) configuration
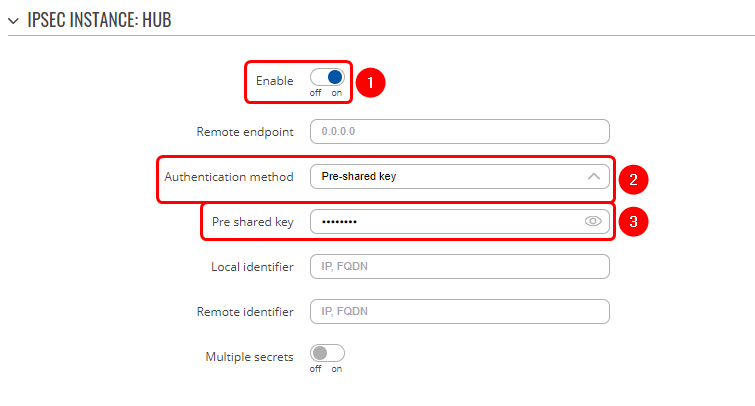
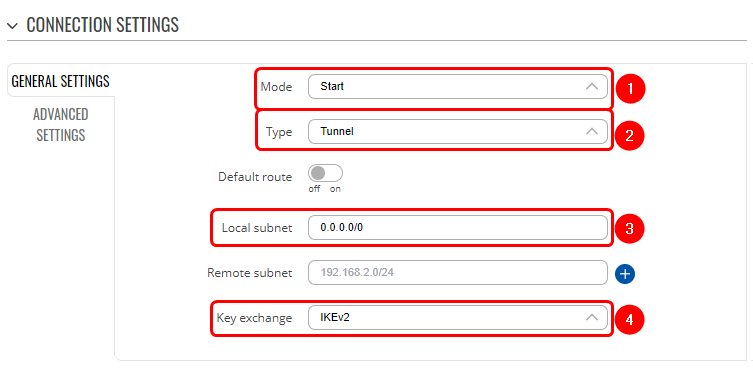
Start by configuring the hub (RUT1) device. Login to the WebUI, navigate to Services → VPN → IPsec and add a new IPsec instance. Configure everything as follows.
Note: Not specified fields can be left as is or changed according to your needs.
Instance configuration
|
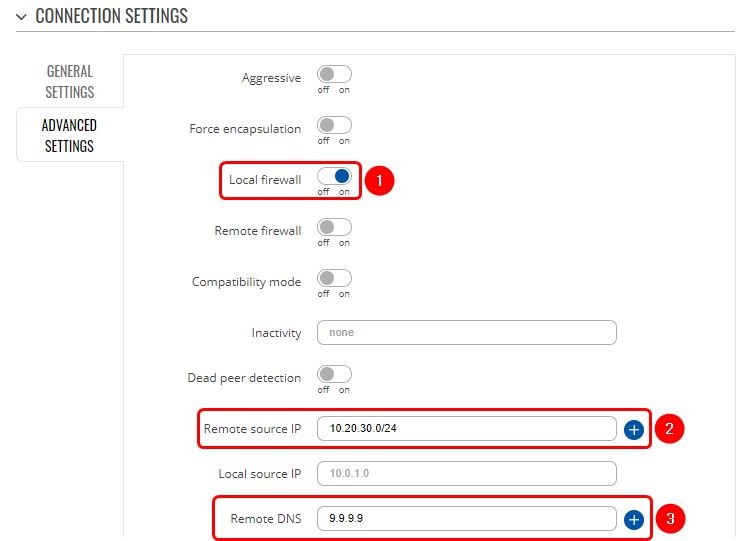
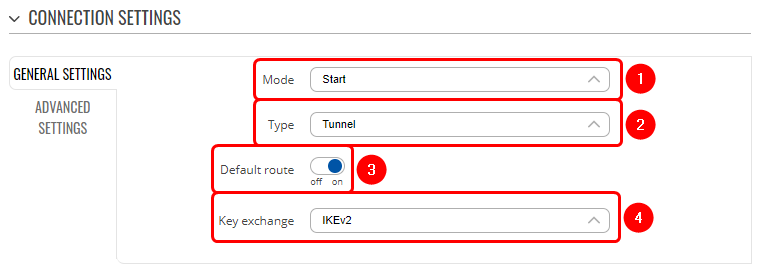
Connection configuration
|
|
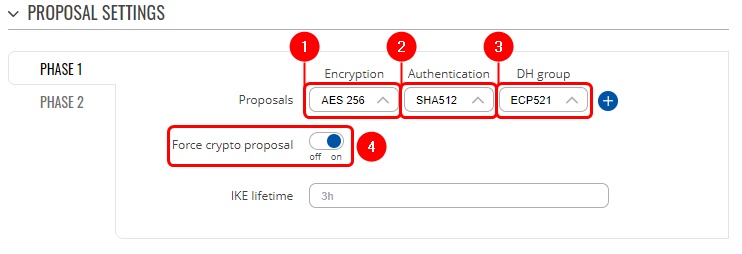
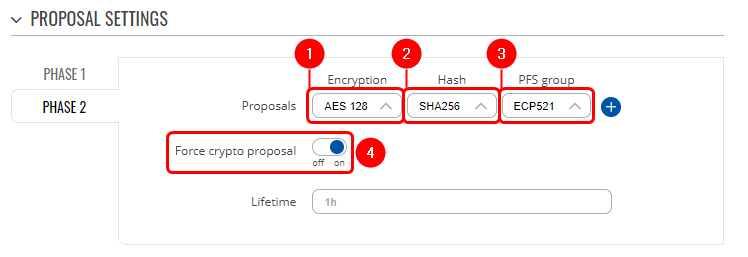
Proposal configuration
|
|
RUT2 (Spoke) configuration
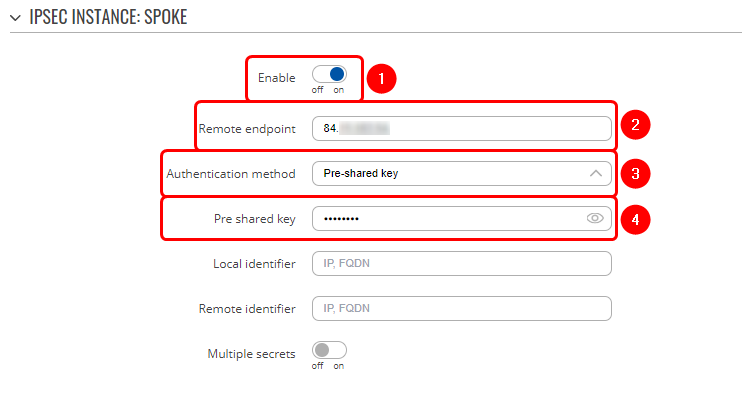
Login to the RUT2 WebUI, navigate to Services → VPN → IPsec and add a new IPsec instance. Configure everything as follows.
Instance configuration
|
Connection configuration
|
Proposal configuration
|
|
Testing the configuration
If you've followed all the steps presented above, your configuration should be finished. But as with any other configuration, it is always wise to test the setup in order to make sure that it works properly.
Using the ipsec statusall command we can see that IPsec tunnel is successfully established on both routers. The command output on a hub (RUT1) device:
root@Teltonika-RUTX12:~# ipsec statusall
Status of IKE charon daemon (strongSwan 5.9.2, Linux 5.4.231, armv7l):
uptime: 74 minutes, since Mar 21 08:52:39 2023
worker threads: 11 of 16 idle, 5/0/0/0 working, job queue: 0/0/0/0, scheduled: 2
loaded plugins: charon aes des sha2 sha1 md4 md5 random nonce x509 revocation constraints pubkey pkcs1 pkcs8 pgp pem openssl gmp xcbc hmac kernel-netlink socket-default stroke vici updown eap-identity eap-mschapv2 xauth-generic
Virtual IP pools (size/online/offline):
10.20.30.0/24: 254/1/0
Listening IP addresses:
84.xxx.xxx.xxx
192.168.11.1
fd93:51e6:6fe8::1
Connections:
HUB-HUB_c: %any...%any IKEv2
HUB-HUB_c: local: uses pre-shared key authentication
HUB-HUB_c: remote: uses pre-shared key authentication
HUB-HUB_c: child: 0.0.0.0/0 === dynamic TUNNEL
Security Associations (1 up, 0 connecting):
HUB-HUB_c[2]: ESTABLISHED 74 minutes ago, 84.xxx.xxx.xxx[84.xxx.xxx.xxx]...88.xxx.xxx.xxx[192.168.86.197]
HUB-HUB_c[2]: IKEv2 SPIs: ded11f31c20352dc_i 58ebc8d96264c21e_r*, pre-shared key reauthentication in 89 minutes
HUB-HUB_c[2]: IKE proposal: AES_CBC_256/HMAC_SHA2_512_256/PRF_HMAC_SHA2_512/ECP_521
HUB-HUB_c{3}: INSTALLED, TUNNEL, reqid 1, ESP in UDP SPIs: c27cb140_i c7382615_o
HUB-HUB_c{3}: AES_CBC_128/HMAC_SHA2_256_128/ECP_521, 215536 bytes_i (1981 pkts, 1s ago), 126021 bytes_o (499 pkts, 1s ago), rekeying in 14 minutes
HUB-HUB_c{3}: 0.0.0.0/0 === 10.20.30.1/32
The same command output on spoke (RUT2) device:
root@Teltonika-RUT955:~# ipsec statusall
Status of IKE charon daemon (strongSwan 5.9.2, Linux 5.4.229, mips):
uptime: 23 hours, since Mar 20 12:21:06 2023
worker threads: 11 of 16 idle, 5/0/0/0 working, job queue: 0/0/0/0, scheduled: 9
loaded plugins: charon aes des sha2 sha1 md4 md5 random nonce x509 revocation constraints pubkey pkcs1 pkcs8 pgp pem openssl gmp xcbc hmac kernel-netlink socket-default stroke vici updown eap-identity eap-mschapv2 xauth-generic
Listening IP addresses:
192.168.86.197
192.168.9.1
fd35:98cd:61f0::1
Connections:
passth_SPOKE_ph2_1_lan: %any...%any IKEv1/2
passth_SPOKE_ph2_1_lan: local: uses public key authentication
passth_SPOKE_ph2_1_lan: remote: uses public key authentication
passth_SPOKE_ph2_1_lan: child: 192.168.9.0/24 === 192.168.9.0/24 PASS
SPOKE-SPOKE_c: %any...84.xxx.xxx.xxx IKEv2
SPOKE-SPOKE_c: local: uses pre-shared key authentication
SPOKE-SPOKE_c: remote: [84.xxx.xxx.xxx] uses pre-shared key authentication
SPOKE-SPOKE_c: child: dynamic === 0.0.0.0/0 TUNNEL
Shunted Connections:
passth_SPOKE_ph2_1_lan: 192.168.9.0/24 === 192.168.9.0/24 PASS
Security Associations (1 up, 0 connecting):
SPOKE-SPOKE_c[431]: ESTABLISHED 77 minutes ago, 192.168.86.197[192.168.86.197]...84.xxx.xxx.xxx[84.xxx.xxx.xxx]
SPOKE-SPOKE_c[431]: IKEv2 SPIs: ded11f31c20352dc_i* 58ebc8d96264c21e_r, pre-shared key reauthentication in 77 minutes
SPOKE-SPOKE_c[431]: IKE proposal: AES_CBC_256/HMAC_SHA2_512_256/PRF_HMAC_SHA2_512/ECP_521
SPOKE-SPOKE_c{14}: INSTALLED, TUNNEL, reqid 1, ESP in UDP SPIs: c7382615_i c27cb140_o
SPOKE-SPOKE_c{14}: AES_CBC_128/HMAC_SHA2_256_128/ECP_521, 136768 bytes_i (536 pkts, 6s ago), 235975 bytes_o (2169 pkts, 1s ago), rekeying in 13 minutes
SPOKE-SPOKE_c{14}: 10.20.30.1/32 === 0.0.0.0/0
Also, as the hub should be reachable by spoke, we can try pinging the hub using ping 192.168.11.1: