RUTXR1 Firewall
The information in this page is updated in accordance with firmware version RUTX_R_00.07.20.1.
Summary
RUTXR1 devices use a standard Linux iptables package as its firewall, which uses routing chains and policies to facilitate control over inbound and outbound traffic.
This chapter of the user manual provides an overview of the Firewall page for RUTXR1 devices.
General Settings
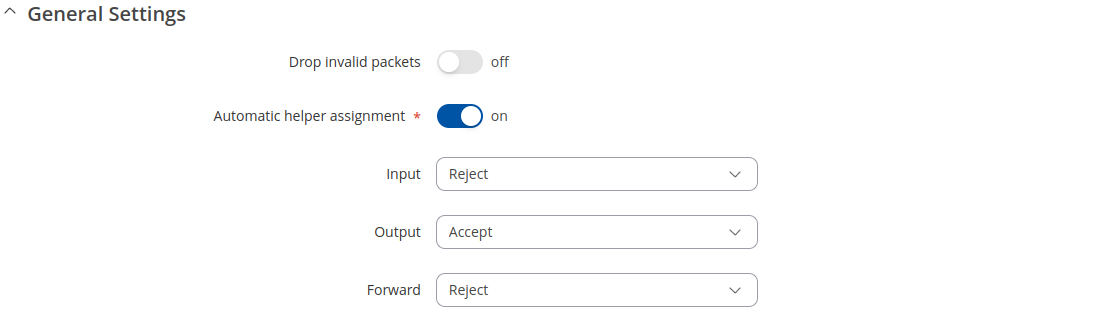
The General Settings section is used to configure the main policies of the device's firewall. The figure below is an example of the General Settings section and the table below provides information on the fields contained in that section:
| Field | Value | Description |
|---|---|---|
| Drop invalid packets | off | on; default: off | If enabled, a "Drop" action will be performed on packets that are determined to be invalid. |
| Automatic helper assignment | off | on; default: on | Automatically assigns conntrack helpers based on traffic protocol and port. If turned off, conntrack helpers can be selected for each zone. |
| Input | Reject | Drop | Accept; default: Reject | Default action* of the INPUT chain if a packet does not match any existing rule on that chain. |
| Output | Reject | Drop | Accept; default: Accept | Default action* of the OUTPUT chain if a packet does not match any existing rule on that chain. |
| Forward | Reject | Drop | Accept; default: Reject | Default action* of the FORWARD chain if a packet does not match any existing rule on that chain. |
* When a packet goes through a firewall chain it is matched against all the rules of that specific chain. If no rule matches said packet, an according Action (Drop, Reject or Accept) is performed:
- Accept – packet gets to continue to the next chain.
- Drop – packet is stopped and deleted.
- Reject – packet is stopped, deleted and, differently from Drop, a message of rejection is sent to the source from which the packet came.
Routing/NAT Offloading
The Routing/NAT Offloading is used to turn software flow offloading on or off.
The device checks whether the flow (sequence of related packets) is received and packed. Packets of unknown flow are forwarded to the networking stack. Meanwhile, if the flow is known, NAT is applied (if matched) and the packet is forwarded to the correct destination port (fast path) to bypass certain layers or packet processing process. As a result, we have a higher throughput and reduced the CPU load. This process is called software flow offloading. Hardware flow offloading is used to execute functions of the router using the hardware directly, instead of a process of software functions.
| Field | Value | Description |
|---|---|---|
| Software flow offloading | off | on; default: on | Software based offloading for routing/NAT. |
| IPsec software flow offload | off | on; default: off | Software based offloading for IPsec. |
Zones
The Zones section is used to manage default traffic forwarding policies between different device zones. The figure below is an example of the Zones section and the table below provides information on the fields contained in that section:
You can change a zone's settings from this page by interacting with entries in the zones table. For a more in-depth configuration click the edit button ![]() next to a zone.
next to a zone.
Zones: General Settings
| Field | Value | Description |
|---|---|---|
| Name | string; default: none | A custom name for the zone. Used for easier management purposes. |
| Input | Accept | Drop | Reject; default: Accept | Default policy for traffic entering the zone.
|
| Output | Accept | Drop | Reject; default: Accept | Default policy for traffic originating from and leaving the zone.
|
| Forwarding inside zone | Accept | Drop | Reject; default: Accept | Default policy for traffic forwarded between the networks belonging to the zone.
|
| Masquerading | off | on; default: off | Turns Masquerading off or on. MASQUERADE is an iptables target that can be used instead of the SNAT (source NAT) target when the external IP of the network interface is not known at the moment of writing the rule (when the interface gets the external IP dynamically). |
| MSS clamping | off | on; default: off | Turns MSS clamping off or on. MSS clamping is a workaround used to change the maximum segment size (MSS) of all TCP connections passing through links with an MTU lower than the Ethernet default of 1500. |
| Covered networks | network interface(s); default: depends on zone | Network or networks that belong to the zone. |
Zones: Advanced Settings
| Field | Value | Description |
|---|---|---|
| Restrict to address family | IPv4 and IPv6 | IPv4 only | IPv6 only; default: IPv4 and IPv6 | IP address family to which to zone will apply. |
| Restrict Masquerading to given source subnets | network/subnet; default: none | Applies Masquerading only to the specified source network/subnet. |
| Restrict Masquerading to given destinations subnets | network/subnet; default: none | Applies Masquerading only to the specified destination network/subnet. |
| Force connection tracking | off | on; default: off | Always maintains connection state (NEW, ESTABLISHED, RELATED) information. |
| Enable logging | off | on; default: off | Log dropped and rejected packets. |
| Limit log messages | integer/minute; default: none | Limit how many messages can be logged in the span of 1 minute. For example, to log 50 packets per minute use: 50/minute. |
| Conntrack helpers | Amanda backup and archiving proto (AMANDA) | FTP passive connection tracking (FTP) | RAS proto tracking (RAS) | Q.931 proto tracking (Q.931) | IRC DCC connection tracking (IRC) | PPTP VPN connection tracking (PPTP) | SIP VoIP connection tracking (SIP) | SNMP monitoring connection tracking (SNMP) | TFTP connection tracking (TFTP); default: none | Explicitly choses allowed connection tracking helpers for zone traffic. |
Forwarding between zones
The options below control the forwarding policies between this zone (lan) and other zones. Destination zones cover forwarded traffic originating from lan. Source zones match forwarded traffic from other zones targeted at lan. The forwarding rule is unidirectional e.g., a forward from lan to wan does not imply a permission to forwad from wan to lan as well.
| Field | Value | Description |
|---|---|---|
| Allow forward to destination zones | zone(s); default: none | Allows forward traffic to specified destination zones. Destination zones cover forwarded traffic originating from this source zone. |
| Allow forward from source zones | zone(s); default: none | Allows forward traffic to specified source zones. Source zones match forwarded traffic originating from other zones that is targeted at this zone. |
Port Forwards
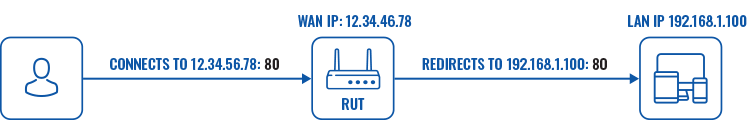
Port forwarding is a way of redirecting an incoming connection to another IP address, port or the combination of both:
The Port forwards table displays configured port forwarding rules currently configured on the device.
| Field | Value | Description |
|---|---|---|
| Name | string; default: none | The name of the rule. This is used for easier management purposes. |
| Match | Only match traffic using the given rules. | |
| Forward | Forward traffic to the given location. | |
| Status | Displays the status of NAT rule. | |
| Counter | Only the first packet of connection is usually counted due to stateful packet inspection (SPI). This also affects connectionless protocols. | |
| Enabled | off | on; default none | Enables port forward rule. |
| Actions | clone | Edit | Delete; default - | Performs the selected action. |
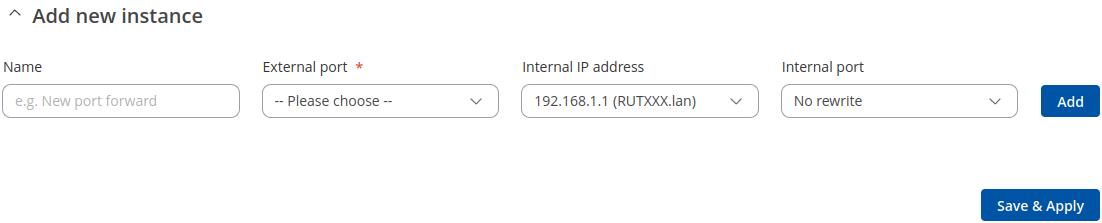
Add new instance
The Add new instance section is used to quickly add additional port forwarding rules.
| Field | Value | Description |
|---|---|---|
| Name | string; default: none | Name of the rule. This is used for easier management purposes. |
| External port | Any | FTP data (20) | FTP cmd (21) | SSH (22) | Old SMTP (25) | DNS (53) | HTTP (80) | NTP (123) | BGP (179) | HTTPS (443) | ISAKMP (500) | Modern SMTP (587) | RDP (3389) | + Add new; default: none | Only match traffic coming to the given port.
|
| Internal IP address | IP | + Add new; default: first IP from the list | Forward traffic to the given network address.
|
| Internal port | No rewrite | FTP data (20) | FTP cmd (21) | SSH (22) | Old SMTP (25) | DNS (53) | HTTP (80) | NTP (123) | BGP (179) | HTTPS (443) | ISAKMP (500) | Modern SMTP (587) | RDP (3389) | + Add new; default: No rewrite | Forward traffic to the given port.
|
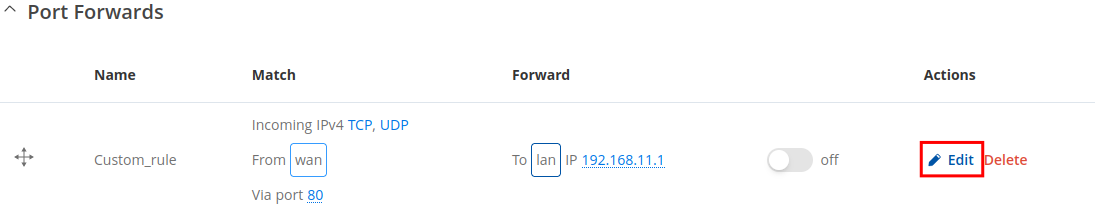
Port Forwards Configuration
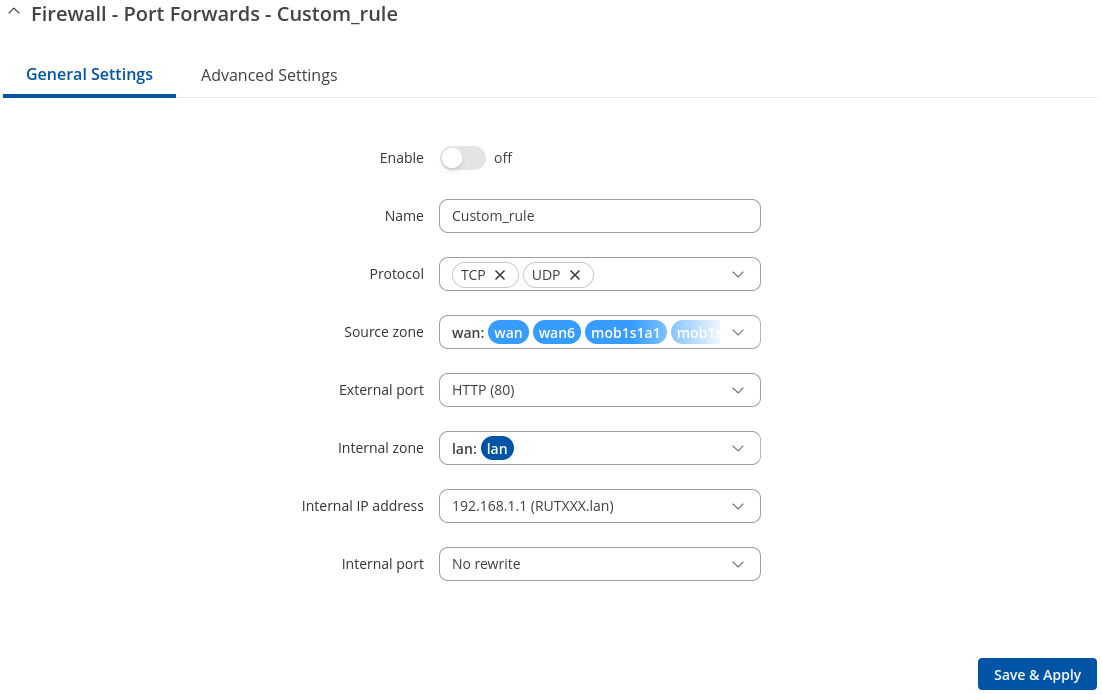
While the New port forward section provides the possibility to add port forwarding rules fast, it does not contain all possible configuration options to customize a rule. In order to create a more complicated rule, add one using the New port forward section and click the edit button ![]() next to it:
next to it:
You will be redirected to that rule's configuration general settings page:
| Field | Value | Description |
|---|---|---|
| Enable | off | on ; default: on | Turns the rule on or off |
| Name | string; default: none | Name of the rule. This is used for easier management purposes. |
| Protocol | TCP | UDP | ICMP | All | +Add new; default: TCP+UDP | Only match traffic using the given internet communication protocol.
|
| Source zone | Unspecified | firewall zone name | framed; default: wan | Only match traffic coming to the given firewall zone. |
| External port | Any | FTP data (20) | FTP cmd (21) | SSH (22) | Old SMTP (25) | DNS (53) | HTTP (80) | NTP (123) | BGP (179) | HTTPS (443) | ISAKMP (500) | Modern SMTP (587) | RDP (3389) | + Add new; default: none | Only match traffic coming to the given port.
|
| Internal zone | Unspecified | firewall zone name | framed; default: lan | Forward traffic to the given firewall zone. |
| Internal IP address | Any | IP | + Add new; default: first IP from the list | Forward traffic to the given network address.
|
| Internal port | No rewrite | FTP data (20) | FTP cmd (21) | SSH (22) | Old SMTP (25) | DNS (53) | HTTP (80) | NTP (123) | BGP (179) | HTTPS (443) | ISAKMP (500) | Modern SMTP (587) | RDP (3389) | + Add new; default: No rewrite | Forward traffic to the given port.
|
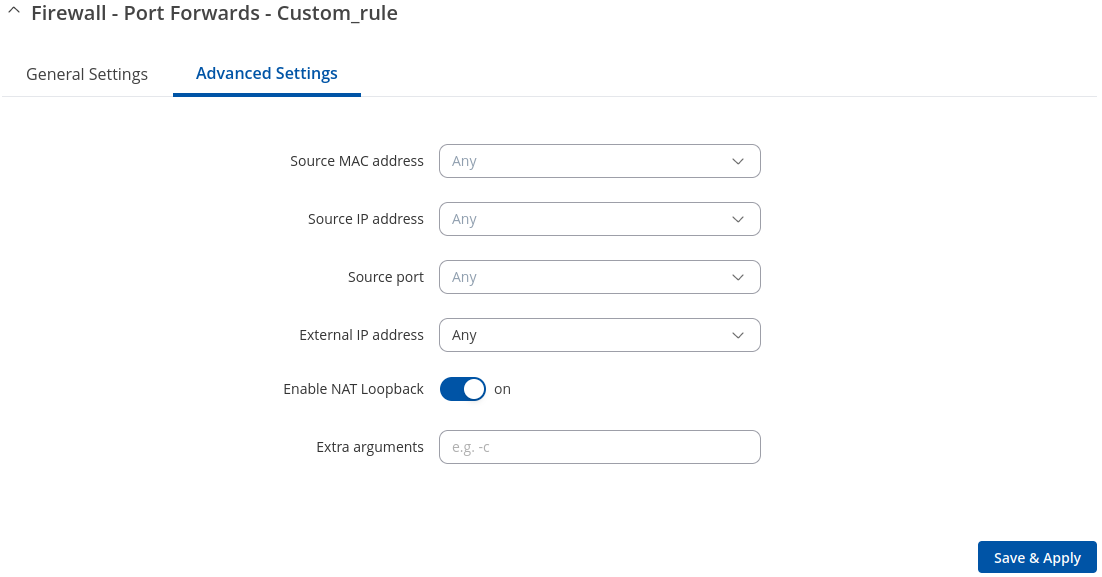
Advanced settings:
| Field | Value | Description |
|---|---|---|
| Source MAC address | mac | + Add new; default: Any | Only match traffic coming from the given MAC address.
|
| Source IP address | IP | + Add new; default: Any | Only match traffic coming from the given network address.
|
| Source port | FTP data (20) | FTP cmd (21) | SSH (22) | Old SMTP (25) | DNS (53) | HTTP (80) | NTP (123) | BGP (179) | HTTPS (443) | ISAKMP (500) | Modern SMTP (587) | RDP (3389) | + Add new; default: Any | Only match traffic coming from the given port.
|
| External IP address | Any | IP | + Add new; default: Any | Only match traffic coming to the given network address.
|
| Enable NAT loopback | off | on ; default: on | NAT loopback a.k.a. NAT reflection a.k.a. NAT hairpinning is a method of accessing an internal server using a public IP. NAT loopback enables your local network (i.e., behind your NAT device) to connect to a forward-facing IP address of a machine that it also on your local network. |
| Extra arguments | string; default: none | Passes additional arguments to iptables. Use with care! |
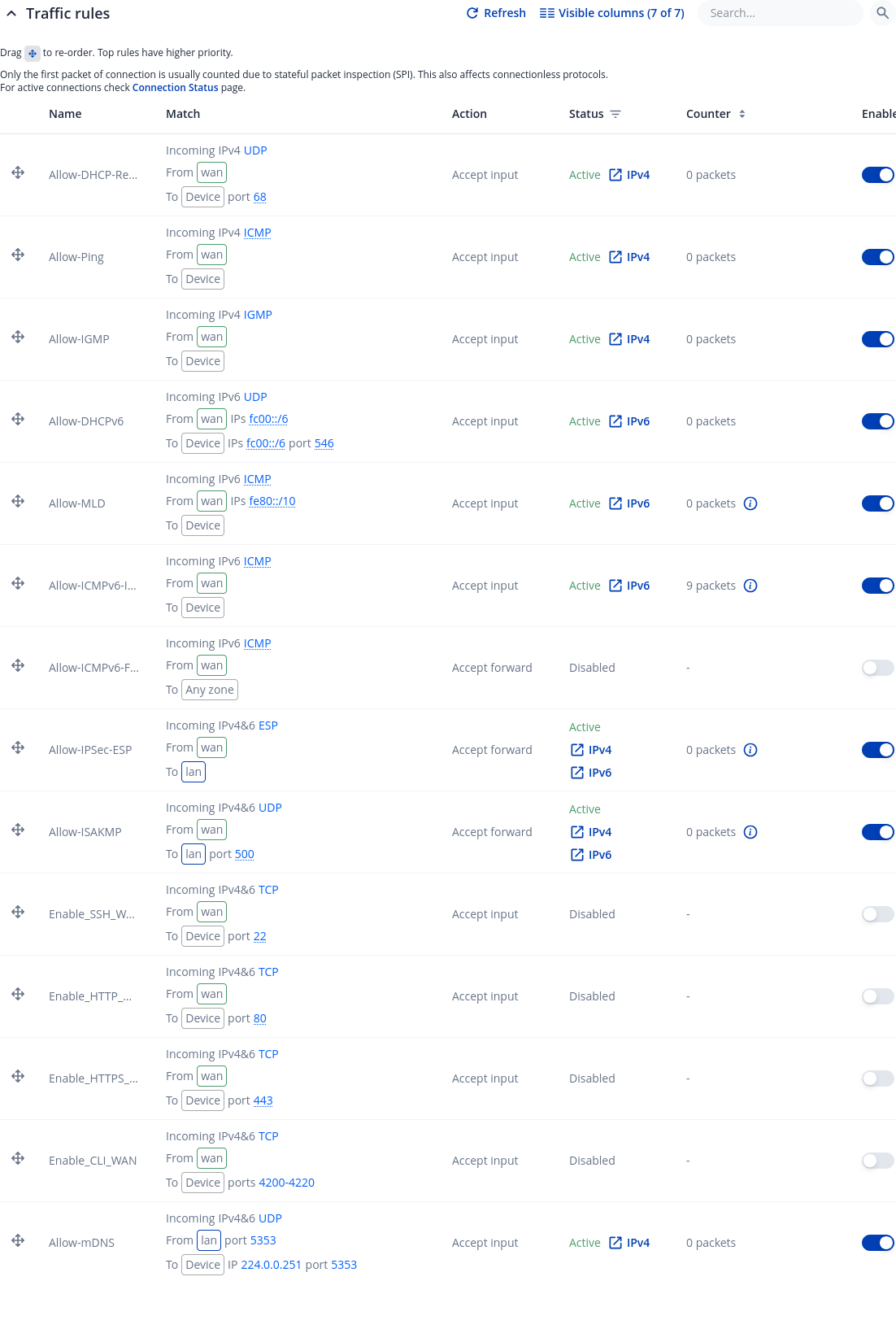
Traffic Rules
The Traffic rules tab is used to set firewall rules that filter traffic moving through the device. The figure below is an example of the Traffic rules table:
| Field | Value | Description |
|---|---|---|
| Name | string; default: - | The name of the rule. This is used for easier management purposes. |
| Match | Only match traffic using the given rules. | |
| Action | Take given action when traffic matches all conditions. | |
| Status | Displays the status of NAT rule. | |
| Counter | Only the first packet of connection is usually counted due to stateful packet inspection (SPI). This also affects connectionless protocols. | |
| Enabled | off | on; default none | Enables traffic rule. |
| Actions | clone | Edit | Delete; default - | Performs the selected action. |
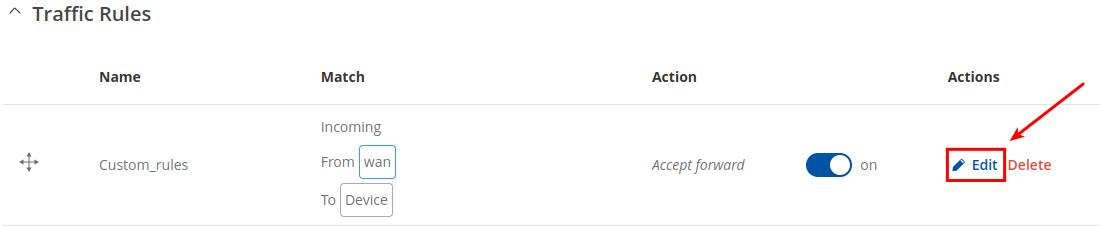
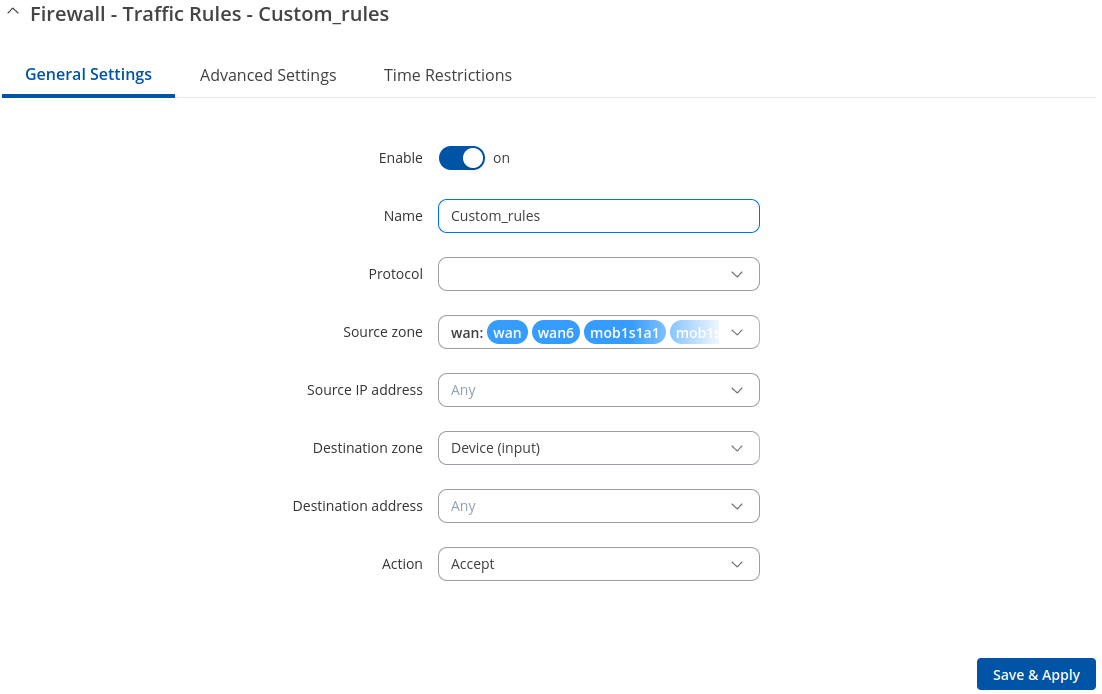
Traffic Rule Configuration
In order to begin editing a traffic rule, click the edit button ![]() next to it:
next to it:
You will be redirected to that rule's configuration page:
General settings
| Field | Value | Description |
|---|---|---|
| Enable | off | on; default on | Turns the rule on or off. |
| Name | string; default none | Name of the rule. This is used for easier management purposes. |
| Protocol | TCP | UDP | ICMP | All | +Add new; default: depends on the rule | Only match traffic using the given internet communication protocol.
|
| Match ICMP type | Any | ICMP-type (list) | + Add new; default: Any | Only match traffic having the given ICMP type. |
| Source zone | firewall zone; default: wan | Only match traffic coming to the given firewall zone. |
| Source IP address | ip address; default: Any | Only match traffic coming from the given network address.
|
| Source port | FTP data (20) | FTP cmd (21) | SSH (22) | Old SMTP (25) | DNS (53) | HTTP (80) | NTP (123) | BGP (179) | HTTPS (443) | ISAKMP (500) | Modern SMTP (587) | RDP (3389) | + Add new; default: Any | Only match traffic coming from the given port.
|
| Destination zone | firewall zone; default: Device (input) | Only match traffic being forwarded to to the given firewall zone. |
| Destination address | ip address; default: Any | Only match traffic being forwarded to the given network address.
|
| Destination port | FTP data (20) | FTP cmd (21) | SSH (22) | Old SMTP (25) | DNS (53) | HTTP (80) | NTP (123) | BGP (179) | HTTPS (443) | ISAKMP (500) | Modern SMTP (587) | RDP (3389) | + Add new; default: Any | Only match traffic being forwarded to the given port.
|
| Action | Drop | Accept | Reject | Do not track | Change DSCP | Mark | Change TTL; default: Accept | Take given action when traffic matches all conditions.
|
| DSCP value | Default | CS1 | AF11 | AF12 | AF13 | CS2 | AF21 | AF22 | AF23...; default: Default | DSCP value to use for actions. |
| Mark value | hexadecimal string; default: empty | Mark value to use for actions. |
| TTL action | Set | Increment | Decrement; default: Set | TTL action to apply to packets. |
| TTL value | integer [1..255]; default: none | TTL value to use for actions. |
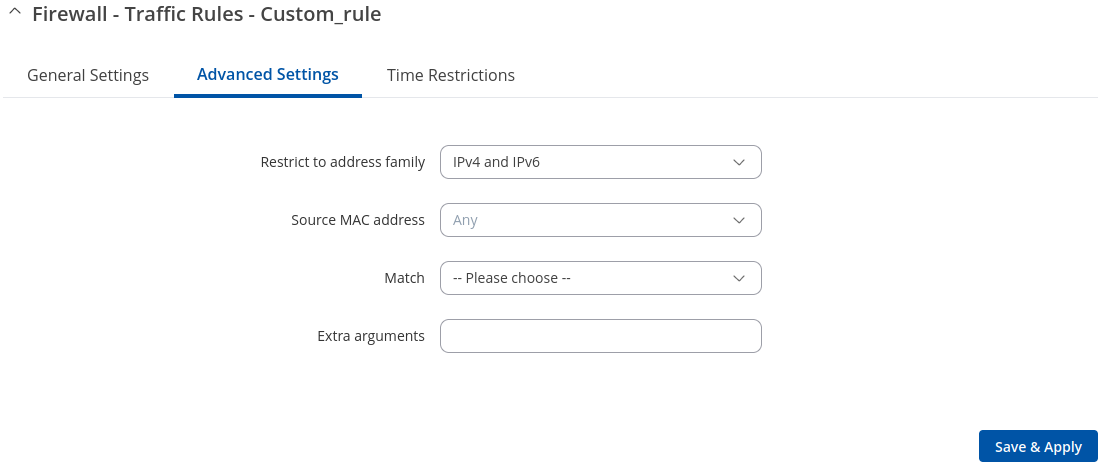
Advanced settings
| Restrict to address family | IPv4 and IPv6 | IPv4 only | IPv6 only; default: IPv4 and IPv6 | Only match traffic using the given IP family. |
| Source MAC address | mac | + Add new; default: Any | Only match traffic coming from the given MAC address.
|
| Match | DSCP | Mark; default: none | Match traffic against the given DSCP value or firewall mark |
| DSCP: Set Match value | Default | DSCP values; default: Default | Match traffic against the given firewall DSCP value. |
| Mark: Set Match value | hexadecimal string; default: none | If specified, match traffic against the given firewall mark, e.g. FF or ff to match mark 255. |
| Extra arguments | string; default: none | Adds extra .iptables options to the rule. |
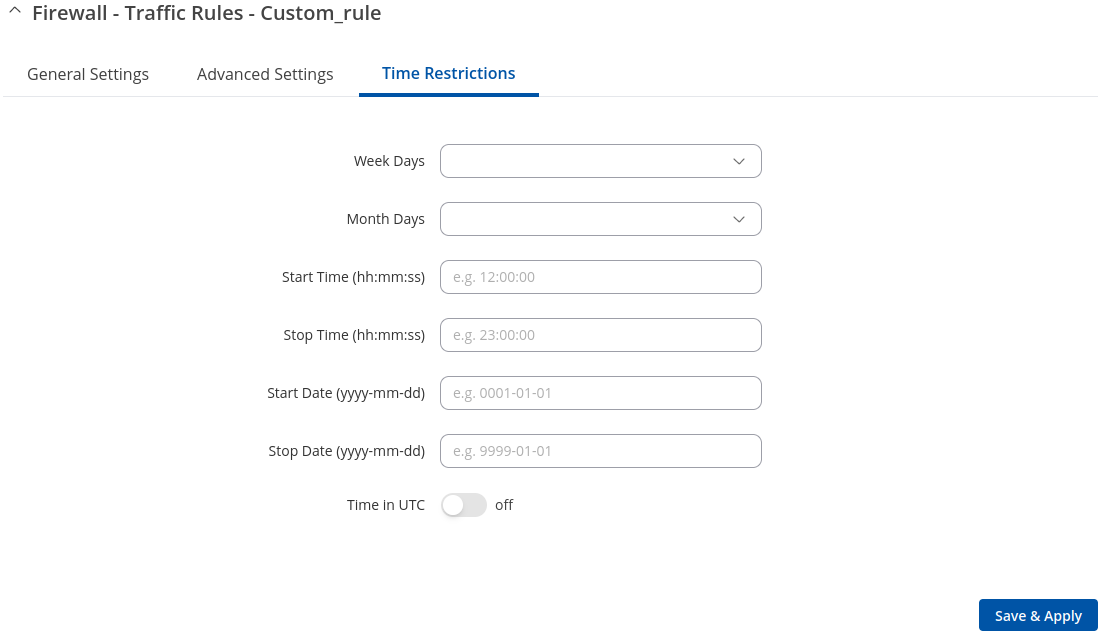
Time restrictions
| Week days | days of the week [Monday..Sunday]; default: none | Specifies on which days of the week the rule is valid. |
| Month days | days of the month [1..31]; default: none | Specifies on which days of the month the rule is valid. |
| Start Time (hh:mm:ss) | time [0..23:0..59:0..59]; default: none | Indicates the beginning of the time period during which the rule is valid. |
| Stop Time (hh:mm:ss) | time [0..23:0..59:0..59]; default: none | Indicates the end of the time period during which the rule is valid. |
| Start Date (yyyy-mm-dd) | date [0000..9999:1..12:1..31]; default: none | Indicates the first day of the date of the period during which the rule is valid. |
| Stop Date (yyyy-mm-dd) | date [0000..9999:1..12:1..31]; default: none | Indicates the last day of the date of the period during which the rule is valid. |
| Time in UTC | off | on; default: no | Specifies whether the device should use UTC time. If this is disabled, the time zone specified in the System → Administration → NTP page will be used. |
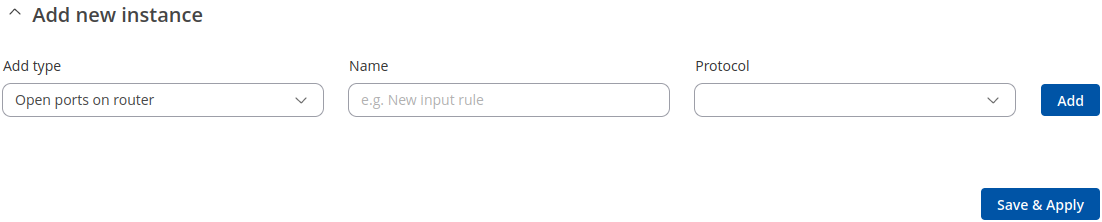
Open Ports on Router
In the Add new instance section, select Open ports on router. This provides a quick way to set simple rules that allow traffic on specified ports of the device. The figure below is an example of the Open ports on device section and the table below provides information on the fields contained in that section:
| Field | Value | Description |
|---|---|---|
| Name | string; default: none | Name of the rule. This is only used for easier management purposes. |
| Protocol | TCP | UDP | ICMP | All | +Add new; default: depends on the rule | Only match traffic using the given internet communication protocol.
|
Add New Forward Rule
In the Add new instance section, select Add new forward rule. This is used to create firewall rules that control traffic on the FORWARD chain. The figure below is an example of the Add New Forward Rule section and the table below provides information on the fields contained in that section:
| Field | Value | Description |
|---|---|---|
| Name | string; default: none | The name of the rule. This is used for easier management purposes. |
| Source zone | firewall zone; default: lan | Only match traffic coming to the given firewall zone. |
| Destination zone | firewall zone; default: lan | Only match traffic being forwarded to the given firewall zone. |
| Add | - (interactive button) | Creates the rule and redirects you to the rule's configuration page |
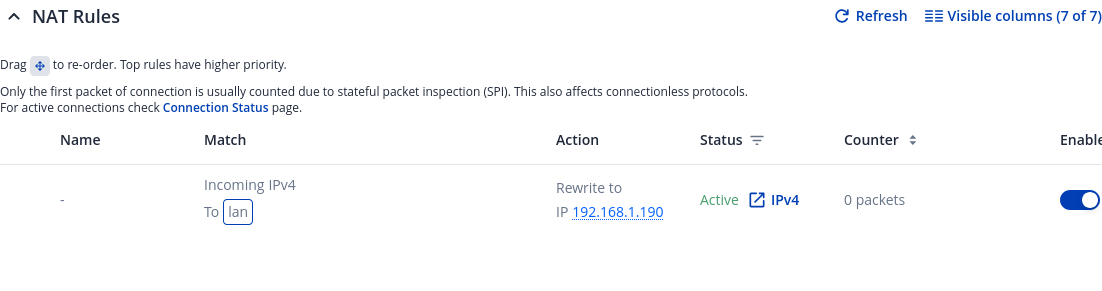
NAT Rules
NAT rules allow fine grained control over the source IP to use for outbound or forwarded traffic.
The NAT section displays currently existing NAT rules.
| Field | Value | Description |
|---|---|---|
| Name | string; default: none | The name of the rule. This is used for easier management purposes. |
| Match | Only match traffic using the given rules. | |
| Action | Modify traffic with the given rules. | |
| Status | Displays the status of NAT rule. | |
| Counter | Only the first packet of connection is usually counted due to stateful packet inspection (SPI). This also affects connectionless protocols. | |
| Enabled | off | on; default none | Enables NAT rule. |
| Actions | clone | Edit | Delete; default - | Performs the selected action. |
Add new instance
The Add new instance section is used to create new NAT rules.
| Field | Value | Description |
|---|---|---|
| Name | string; default: none | The name of the rule. This is used for easier management purposes. |
| Source zone | firewall zone; default: lan | Only match traffic coming to the given firewall zone. |
| Rewrite IP | IP | + Add new; default: first IP from the list | Rewrite matched traffic to the given source network address.
|
| Rewrite Port | integer [0..65335] | port inversion [!0..!65535] | do not rewrite; default: none | Rewrite matched traffic to the given source port.
|
| Add | - (interactive button) | Creates the rule in accordance with the given parameter and redirects you to the rule's configuration page. |
NAT Configuration
After adding new rule, you will be redirected to that rule's configuration page:
| Field | Value | Description |
|---|---|---|
| Enable | off | on; default on | Turns the rule on or off. |
| Name | string; default none | Name of the rule. This is used for easier management purposes. |
| Protocol | TCP | UDP | ICMP | All | +Add new; default: All | Only match traffic using the given internet communication protocol.
|
| Outband zone | firewall zone; default: lan | Only match traffic leaving the given firewall zone. |
| Source IP address | ip address; default: Any | Only match traffic coming from the given network address.
|
| Source port | FTP data (20) | FTP cmd (21) | SSH (22) | Old SMTP (25) | DNS (53) | HTTP (80) | NTP (123) | BGP (179) | HTTPS (443) | ISAKMP (500) | Modern SMTP (587) | RDP (3389) | + Add new; default: Any | Only match traffic coming from the given port.
|
| Destination IP address | ip address; default: Any | Only match traffic being forwarded to the given network address.
|
| Destination port | FTP data (20) | FTP cmd (21) | SSH (22) | Old SMTP (25) | DNS (53) | HTTP (80) | NTP (123) | BGP (179) | HTTPS (443) | ISAKMP (500) | Modern SMTP (587) | RDP (3389) | + Add new; default: Any | Only match traffic being forwarded to the given port.
|
| Action | SNAT | MASQUERADE | ACCEPT; default SNAT | NAT action to use on matched traffic.
|
| Rewrite IP address | ip address; default: Any | Only match traffic being forwarded to the given network address.
|
| Field | Value | Description |
|---|---|---|
| Extra arguments | string; default: none | Passes additional arguments to iptables. Use with care! |
| Field | Value | Description |
|---|---|---|
| Week days | days of the week [Monday..Sunday]; default: none | Specifies on which days of the week the rule is valid. |
| Month days | days of the month [1..31]; default: none | Specifies on which days of the month the rule is valid. |
| Start Time (hh:mm:ss) | time [0..23:0..59:0..59]; default: none | Indicates the beginning of the time period during which the rule is valid. |
| Stop Time (hh:mm:ss) | time [0..23:0..59:0..59]; default: none | Indicates the end of the time period during which the rule is valid. |
| Start Date (yyyy-mm-dd) | date [0000..9999:1..12:1..31]; default: none | Indicates the first day of the date of the period during which the rule is valid. |
| Stop Date (yyyy-mm-dd) | date [0000..9999:1..12:1..31]; default: none | Indicates the last day of the date of the period during which the rule is valid. |
| Time in UTC | off | on; default: no | Specifies whether the device should use UTC time. If this is disabled, the time zone specified in the System → Administration → NTP page will be used. |
Attack Prevention
The Attack Prevention menu tab provides the possibility to configure protections against certain types of online attacks.
| Field | Value | Description |
|---|---|---|
| Attack type | Name of attack prevention type. | |
| Enable | off | on | Enable attack from WAN zone prevention (except SYN flood which applies to all zones). |
| Advanced settings | -interactive button (Edit) | Opens attack prevention configuration window. |
Note: the individual attack prevention configuration windows are shown below.
SYN flood
SYN Flood attack prevention allows you to protect yourself from attacks that exploit part of the normal TCP three-way handshake to consume resources on the targeted server and render it unresponsive. Essentially, with SYN flood DDOS, the offender sends TCP connection requests faster than the targeted machine can process them, causing network over-saturation.
| Field | Value | Description |
|---|---|---|
| Enable attack prevention | off | on; default: on | Enable new connection throttle for the "SYN flood" to prevent flood attacks from all zones. It uses token bucket algorithm. |
| Limit | integer [1..10000]; default: 25 | The maximum theoretical rate. It represents how quickly the burst refills. |
| Burst | integer [1..10000]; default: 50 | Sets burst limit for SYN packets above which the traffic is considered flooded if it exceeds the allowed rate |
| TCP SYN cookies | off | on; default: on | Enables the use of SYN cookies (particular choices of initial TCP sequence numbers by TCP servers) |
Ping flood
Some attackers use ICMP echo request packets directed to IP broadcast addresses from remote locations to generate denial-of-service attacks. You can set up some custom restrictions to help protect your router from ICMP bursts.
| Field | Value | Description |
|---|---|---|
| Enable remote ping requests | off | on; default: on | Allows remote (WAN zone) ICMP echo-request type. |
| Enable attack prevention | off | on; default: off | Enable new connection throttle for the "Ping flood" to prevent flood attacks from WAN zone. It uses token bucket algorithm. |
| Limit | integer [1..10000]; default: 60 | The maximum theoretical rate. It represents how quickly the burst refills. |
| Limit period | Second | Minute | Hour | Day; default: Second | Period length for matching the conditions of the rule. |
| Burst | integer [1..10000]; default: 60 | The maximum number of new connections that can occur in a short time. This is the token bucket, which is depleted with each new connection. It refills at the rate defined by the limit, and if empty, new connections are blocked. |
| Enable logging | off | on; default: off | Flood detection events will be logged to System log. |
SSH flood
This protection prevent SSH attacks by limiting connections in a defined period.
| Field | Value | Description |
|---|---|---|
| Enable attack prevention | off | on; default: off | Enable new connection throttle for the "SSH flood" to prevent flood attacks from WAN zone. It uses token bucket algorithm. |
| Limit | integer [1..10000]; default: 100 | The maximum theoretical rate. It represents how quickly the burst refills. |
| Limit period | Second | Minute | Hour | Day; default: Second | Period length for matching the conditions of the rule. |
| Burst | integer [1..10000]; default: 100 | The maximum number of new connections that can occur in a short time. This is the token bucket, which is depleted with each new connection. It refills at the rate defined by the limit, and if empty, new connections are blocked. |
| Enable logging | off | on; default: off | Flood detection events will be logged to System log. |
HTTP flood
An HTTP attack sends a complete, legitimate HTTP header, which includes a 'Content-Length' field to specify the size of the message body to follow. However, the attacker then proceeds to send the actual message body at an extremely slow rate (e.g. 1 byte/100 seconds.) Due to the entire message being correct and complete, the target server will attempt to obey the 'Content-Length' field in the header, and wait for the entire body of the message to be transmitted, hence slowing it down.
| Field | Value | Description |
|---|---|---|
| Enable attack prevention | off | on; default: off | Enable new connection throttle for the "HTTP flood" to prevent flood attacks from WAN zone. It uses token bucket algorithm. |
| Limit | integer [1..10000]; default: 120 | The maximum theoretical rate. It represents how quickly the burst refills. |
| Limit period | Second | Minute | Hour | Day; default: Second | Period length for matching the conditions of the rule. |
| Burst | integer [1..10000]; default: 120 | The maximum number of new connections that can occur in a short time. This is the token bucket, which is depleted with each new connection. It refills at the rate defined by the limit, and if empty, new connections are blocked. |
| Enable logging | off | on; default: off | Flood detection events will be logged to System log. |
HTTPS flood
This section allows you to enable protection against HTTPS attacks, also known as "man-in-the-middle" attacks (MITM).
In cryptography and computer security, a man-in-the-middle attack (MITM) is an attack where the perpetrator secretly relays and possibly alters the communication between two parties who believe they are directly communicating with each other. One example of man-in-the-middle attacks is active eavesdropping, in which the attacker makes independent connections with the victims and relays messages between them to make them believe they are talking directly to each other over a private connection, when in fact the entire conversation is controlled by the attacker.
| Field | Value | Description |
|---|---|---|
| Enable attack prevention | off | on; default: off | Enable new connection throttle for the "HTTPS flood" to prevent flood attacks from WAN zone. It uses token bucket algorithm. |
| Limit | integer [1..10000]; default: 120 | The maximum theoretical rate. It represents how quickly the burst refills. |
| Limit period | Second | Minute | Hour | Day; default: Second | Period length for matching the conditions of the rule. |
| Burst | integer [1..10000]; default: 120 | The maximum number of new connections that can occur in a short time. This is the token bucket, which is depleted with each new connection. It refills at the rate defined by the limit, and if empty, new connections are blocked. |
| Enable logging | off | on; default: off | Flood detection events will be logged to System log. |
Port Scan
Port Scan attacks scan which of the targeted host's ports are open. Network ports are the entry points to a machine that is connected to the Internet. A service that listens on a port is able to receive data from a client application, process it and send a response back. Malicious clients can sometimes exploit vulnerabilities in the server code so they gain access to sensitive data or execute malicious code on the machine remotely. Port scanning is usually done in the initial phase of a penetration test in order to discover all network entry points into the target system. The Port Scan section provides you with the possibility to enable protection against port scanning software. The Defending Type section provides the possibility for the user to enable protections from certain types of online attacks. These include SYN-FIN, SYN-RST, X-Mas, FIN scan and NULLflags attacks.
| Field | Value | Description |
|---|---|---|
| Enable port scan prevention | off | on; default: off | Enable brute force port scan prevention from WAN zone. If there is too much TCP packets from same host without responses they start to be rejected. |
| Scan count | integer [5..255]; default: 5 | Port scan (TCP packet without response) count before packets are rejected. |
| Interval | integer [10..1000]; default: 10 | Time span (in seconds) in which 'scan count' has to be reached before packets are rejected. |
| SYN-FIN attack | off | on; default: off | Turns protection from SYN-FIN attacks on or off. |
| SYN-RST attack | off | on; default: off | Turns protection from SYN-RST attacks on or off. |
| X-Mas attack | off | on; default: off | Turns protection from X-Mas attacks on or off. |
| FIN scan | off | on; default: off | Protect from nmap FIN scan. |
| NULLflags attack | off | on; default: off | Turns protection from NULLflags attacks on or off. |
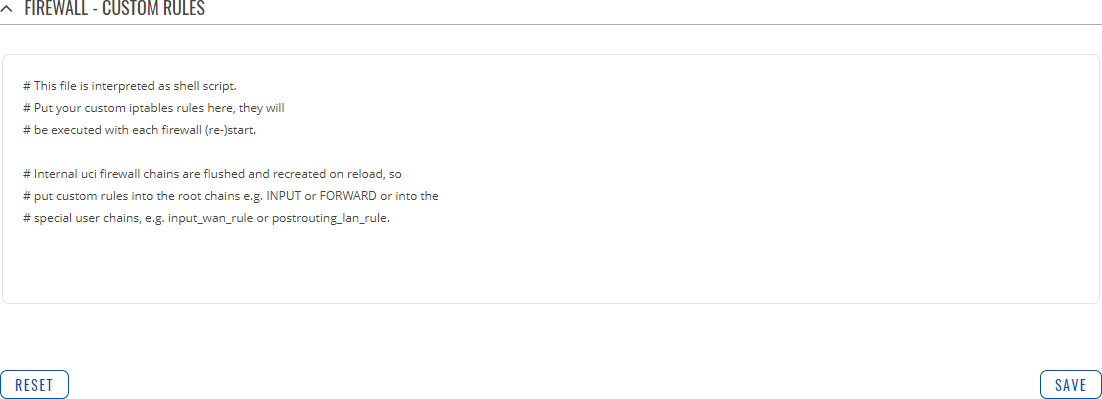
Custom Rules
The Custom rules tab provides you with the possibility to execute iptables commands which are not otherwise covered by the device's firewall framework. The commands are executed after each firewall restart, right after the default rule set has been loaded.
Note: Custom rules are not recommended to be used with hostnames. The rules will not remain active after reboot due to security reasons.
The figure below is an example of the Custom rules tab:
The rules added here are saved in the /etc/firewall.user file. Feel free to edit that file instead for the same effect in case you don't have access to the device's WebUI.
The Save button restarts the firewall service. Thus, adding the custom rules specified in this section to the device's list of firewall rules.
The Reset button resets the custom rules field to its default state.
DMZ
The DMZ is a security concept. It comprises the separation of the LAN-side network into at least two networks: the user LAN and the DMZ. Generally the DMZ is imprisoned: only access to certain ports from the Internet are allowed into the DMZ, while the DMZ is not allowed to establish new connections to the WAN-side or LAN-side networks. That way, if a server inside of the DMZ is hacked the potential damage that can be done remains restricted! The whole point of the DMZ is to cleanly create a unique firewall rule set that dramatically restricts access in to, and out of the, DMZ.
| Field | Value | Description |
|---|---|---|
| Enable | off | on; default: off | Enables the DMZ configuration. |
| Status | state; default: | Displays the status of the DMZ. |
| Counter | count of packets; default: | Only the first packet of connection is usually counted due to stateful packet inspection (SPI). This also affects connectionless protocols. |
| Host IP | ipv4; default: none | Specifies the IP address of the DMZ host. |
| Protocol | All | TCP | UDP | ICMP; default: None | Specifies for which protocols the DMZ will be used. |
| Ports | 0..65535 | port range | port negation; default: none | Match incoming traffic directed at the given destination port or port range on DMZ host IP. |