L2TP over IPsec PC: Difference between revisions
m (Žilvinas moved page Draft:L2TP over IPsec PC to L2TP over IPsec PC without leaving a redirect) |
No edit summary |
||
| (12 intermediate revisions by 3 users not shown) | |||
| Line 16: | Line 16: | ||
---- | ---- | ||
'''Configuration scheme''': | '''Configuration scheme''': | ||
[[File:Finaltopology.jpg|left|Finaltopology]] | |||
The figure above shows the L2TP/IPsec scheme. It is quite similar to the [[L2TP_configuration_examples#Configuration_overview_and_prerequisites|L2TP]] and [[IPsec_configuration_examples#Configuration_overview_and_prerequisites|IPsec]] configuration schemes - the router with the public IP address (''RUT'') acts as the L2TP/IPsec server and a ''PC'' acts as the client. L2TP connects the RUT and PC networks and IPsec provides the encryption for the L2TP tunnel. | The figure above shows the L2TP/IPsec scheme. It is quite similar to the [[L2TP_configuration_examples#Configuration_overview_and_prerequisites|L2TP]] and [[IPsec_configuration_examples#Configuration_overview_and_prerequisites|IPsec]] configuration schemes - the router with the public IP address (''RUT'') acts as the L2TP/IPsec server and a ''PC'' acts as the client. L2TP connects the RUT and PC networks and IPsec provides the encryption for the L2TP tunnel. | ||
| Line 23: | Line 24: | ||
==Router configuration== | ==Router configuration== | ||
If you have familiarized yourself with the configuration scheme and have all of the devices in order, we can start configuring the router using instructions provided in this section. To summarize, we'll be configuring an L2TP server and an IPsec Transport instance (server) on ''RUT''; an L2TP/IPsec client on ''PC''. | If you have familiarized yourself with the configuration scheme and have all of the devices in order, we can start configuring the router using instructions provided in this section. To summarize, we'll be configuring an L2TP server and an IPsec Transport instance (server) on ''RUT''; an L2TP/IPsec client on ''PC''. | ||
As mentioned in the prerequisites section, the router that acts as the server must have a Public Static or Public Dynamic IP address (more information on the subject can be found here). If that is in order, we should start configuring the server. | |||
===L2TP=== | |||
For more in-depth explanations about these parameters, you can visit the following wiki pages: '''[[VPN#IPsec|VPN manual page, IPsec section]]'''. | |||
<table class="nd-othertables_2"> | |||
<tr> | |||
<th width=355; style="border-bottom: 1px solid white;></th> | |||
<th width=790; style="border-bottom: 1px solid white;" rowspan=2> [[File:RutOS_L2TP_IPsec_VPN_7,8_add_L2TP_Server.png|770px|right]]</th> | |||
</tr> | |||
<tr> | |||
<td style="border-bottom: 1px solid white;> | |||
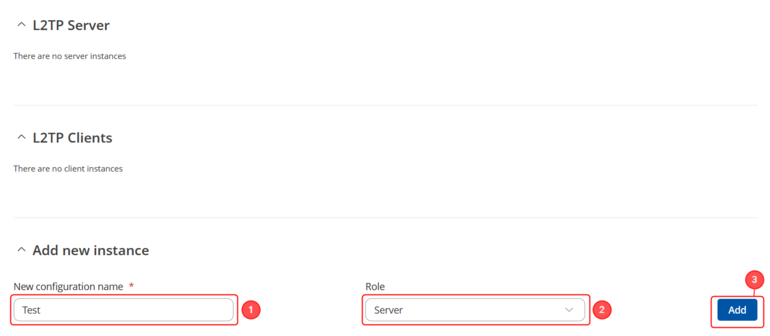
Login to the router's WebUI and navigate to the '''Services → VPN → L2TP''' page and do the following: | |||
<ol> | |||
<li>Select '''Role: Server'''.</li> | |||
<li>Enter a '''custom configuration name'''.</li> | |||
<li>Click the '''Add''' button. You will be prompted to the configuration window</li> | |||
</ol> | |||
</td> | |||
</tr> | |||
</table> | |||
---- | |||
<table class="nd-othertables_2"> | |||
<tr> | |||
<th width=355; style="border-bottom: 1px solid white;></th> | |||
<th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:RutOS_L2TP_IPsec_VPN_7,8_add_L2TP_Server_config.png|770px|right]]</th> | |||
</tr> | |||
<tr> | |||
<td style="border-bottom: 1px solid white> | |||
<ol> | |||
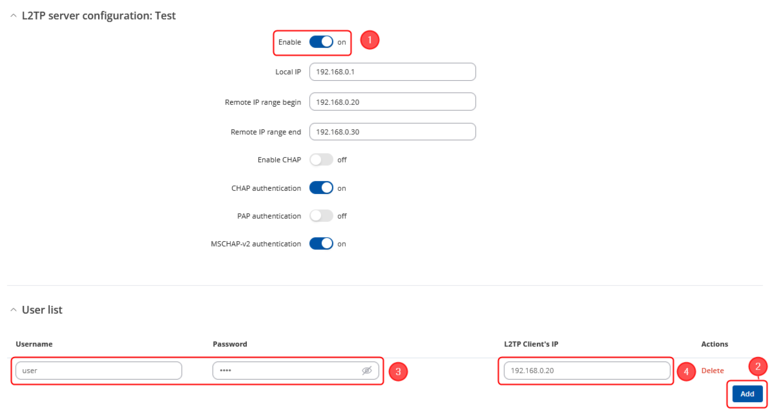
<li>'''Enable''' the L2TP instance.</li> | |||
<li>Click on the '''Add''' button to add a new user</li> | |||
<li>Enter a '''User name''' and '''Password''' for authentication for the client.</li> | |||
<li>Optionally, set a fixed IP for this client (if left empty, the client will receive the first free IP from the IP range).</li> | |||
<li>Don't forget to '''Save''' the changes.</li> | |||
</ol> | |||
</td> | |||
</tr> | |||
</table> | |||
=== | ===IPsec=== | ||
---- | ---- | ||
<table class="nd-othertables_2"> | |||
<tr> | |||
<th width=355; style="border-bottom: 1px solid white;></th> | |||
<th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:RutOS_L2TP_IPsec_VPN_7,8_add_Ipsec_Server.png|770px|right]]</th> | |||
</tr> | |||
<tr> | |||
<td style="border-bottom: 1px solid white> | |||
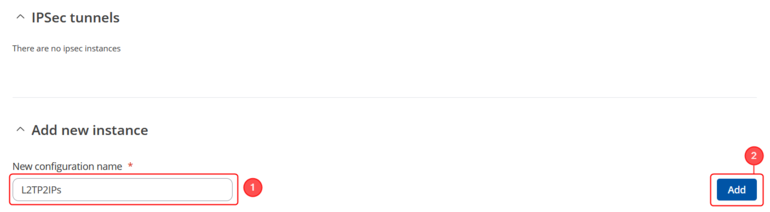
Go to the '''Services → VPN → IPsec''' page and do the following: | |||
<ol> | |||
<li>Enter a custom name for the IPsec instance.</li> | |||
<li>Click the '''Add''' button. You will be prompted to the configuration window</li> | |||
</ol> | |||
</td> | |||
</tr> | |||
</table> | |||
---- | ---- | ||
<table class="nd-othertables_2"> | |||
<tr> | |||
<th width=355; style="border-bottom: 1px solid white;></th> | |||
<th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:RutOS_L2TP_IPsec_VPN_7,8_add_Ipsec_Server_config_instnace222.png|770px|right]]</th> | |||
</tr> | |||
<tr> | |||
<td style="border-bottom: 1px solid white> | |||
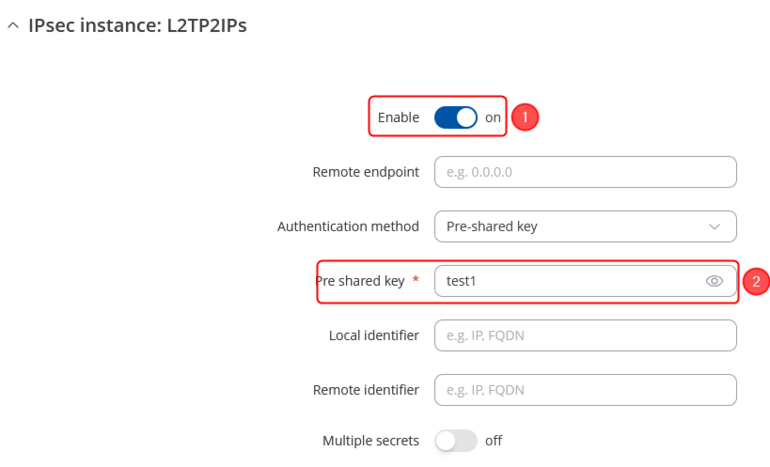
In the '''IPsec Configuration''' page, do the following (and leave the rest as defaults, unless your specific configuration requires otherwise): | |||
<ol> | |||
<li>'''Enable''' the instance.</li> | |||
<li>Enter your '''Pre-shared key'''.</li> | |||
</ol> | |||
</td> | |||
</tr> | |||
</table> | |||
<table class="nd-othertables_2"> | |||
<tr> | |||
<th width=355; style="border-bottom: 1px solid white;></th> | |||
<th width=790; style="border-bottom: 1px solid white;" rowspan=2>[[File:RutOS_L2TP_IPsec_PC_7.8_1.png|770px|right]]</th> | |||
</tr> | |||
<tr> | |||
<td style="border-bottom: 1px solid white> | |||
<ol> | |||
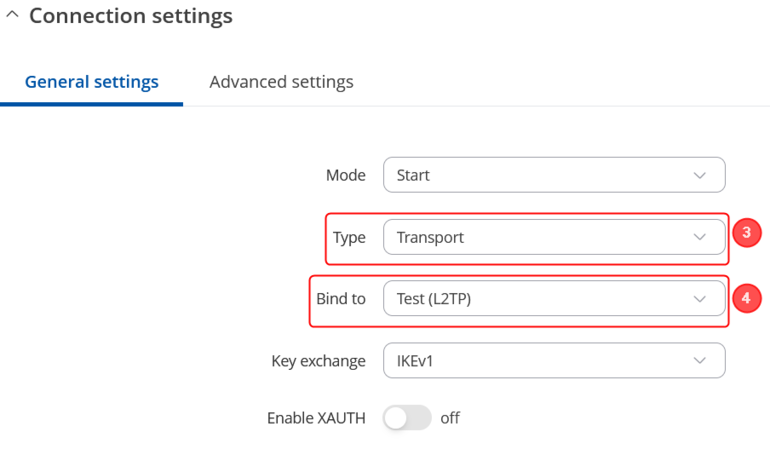
'''3.''' Select '''Type: Transport'''.<br> | |||
'''4.''' Select '''Bind to: Test(L2TP)'''. | |||
<br> | |||
</ol> | |||
</td> | |||
</tr> | |||
</table> | |||
---- | ---- | ||
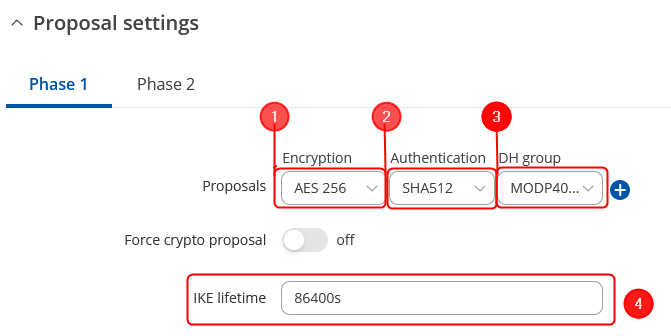
'''Note:''' ''This is only an example of a secure configuration. Other algorithms or even combinations of them could be used. However, we strongly recommend refraining from using older encryption and hashing algorithms unless support for certain legacy systems is required.'' | |||
Make the following changes: | |||
<table class="nd-othertables_2"> | |||
<tr> | |||
<th width=330; style="border-bottom: 1px solid white;></th> | |||
<th width=800; style="border-bottom: 1px solid white;" rowspan=2>[[File:Networking_webui_manual_IPsec_configuration_proposal_phase1_settings_v1.png|border|class=tlt-border|671x336px|center]]</th> | |||
</tr> | |||
<tr> | |||
<td style="border-bottom: 4px solid white> | |||
# Encryption - '''''AES256;''''' | |||
# Authentication - '''''SHA512;''''' | |||
# DH group - '''''MODP4096;''''' | |||
# IKE lifetime - '''86400s'''. | |||
</td> | |||
</tr> | |||
</table> | |||
[[File: | ---- | ||
<table class="nd-othertables_2"> | |||
<tr> | |||
<th width=330; style="border-bottom: 1px solid white;></th> | |||
<th width=800; style="border-bottom: 1px solid white;" rowspan=2>[[File:Networking_webui_manual_IPsec_configuration_proposal_phase2_settings_v1.png|border|class=tlt-border|644x331px|center]]</th> | |||
</tr> | |||
<tr> | |||
<td style="border-bottom: 4px solid white> | |||
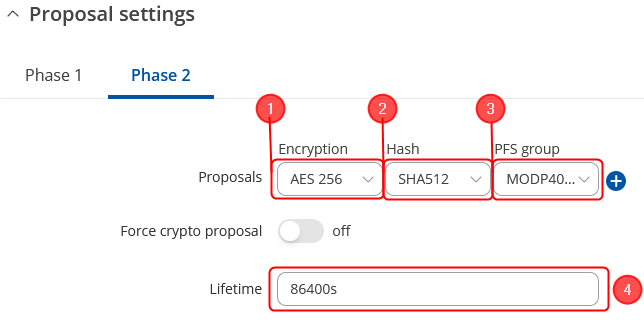
# Encryption - '''''AES256;''''' | |||
# Authentication - '''''SHA512;''''' | |||
# PFS group - '''''MODP4096;''''' | |||
# Lifetime – '''''86400s;''''' | |||
</td> | |||
</tr> | |||
</table> | |||
===PC Client=== | ===PC Client=== | ||
| Line 60: | Line 158: | ||
To configure a windows PC as a client, you can use the already developed VPN function. To do this, select the search bar and type "Add a VPN connection". Then select the "Add VPN" option. | To configure a windows PC as a client, you can use the already developed VPN function. To do this, select the search bar and type "Add a VPN connection". Then select the "Add VPN" option. | ||
*'''Client configuration''': | *'''Client configuration''': | ||
[[File: | [[File:WindowsVPNconfigf.png|left|WindowsVPNconfig|border|class=tlt-border|1100px]] | ||
*'''VPN provider''' - VPN provider to be configured. In our case we select the "Windows (build-in)" option. | *'''VPN provider''' - VPN provider to be configured. In our case we select the "Windows (build-in)" option. | ||
*'''Connection name''' - enter a custom name. | *'''Connection name''' - enter a custom name. | ||
| Line 74: | Line 172: | ||
If you've followed all the steps presented above, your configuration should be finished. But as with any other configuration, it is always wise to test the setup in order to make sure that it works properly. The simplest way to test an IPsec connection is using the ipsec status command. You can execute this command via a command line interface (CLI). A CLI is present in all RUTxxx routers' WebUIs. To access it, login to the routers' WebUI and navigate to ''' Services''' → ''' CLI''' . Login to CLI with the user name root and the router's admin password. Then simply the ipsec status and press the "Enter" key: | If you've followed all the steps presented above, your configuration should be finished. But as with any other configuration, it is always wise to test the setup in order to make sure that it works properly. The simplest way to test an IPsec connection is using the ipsec status command. You can execute this command via a command line interface (CLI). A CLI is present in all RUTxxx routers' WebUIs. To access it, login to the routers' WebUI and navigate to ''' Services''' → ''' CLI''' . Login to CLI with the user name root and the router's admin password. Then simply the ipsec status and press the "Enter" key: | ||
[[File: | [[File:Ipseccorrectlyfinal2.png|left|Ipseccorrectlyfinal2|border|class=tlt-border|1100px]] | ||
As you can see, executing ipsec status displays the number of active/inactive IPsec connections. If the connection you just configured is the only IPsec connection that you're using, you should a 1 up indication next to Security Associations. | As you can see, executing ipsec status displays the number of active/inactive IPsec connections. If the connection you just configured is the only IPsec connection that you're using, you should a 1 up indication next to Security Associations. | ||
| Line 80: | Line 178: | ||
To test an L2TP connection. You should then be able to ping the opposite instance, i.e., if you logged in to the server's CLI, you should be able to ping the client's virtual IP address, and vice versa. To use a ping command, type ''' ping <ip_address>''' and press the ''' Enter''' key on your keyboard: | To test an L2TP connection. You should then be able to ping the opposite instance, i.e., if you logged in to the server's CLI, you should be able to ping the client's virtual IP address, and vice versa. To use a ping command, type ''' ping <ip_address>''' and press the ''' Enter''' key on your keyboard: | ||
[[File: | [[File:L2tpcorrectlyfinal.png|left|L2tpcorrectly|border|class=tlt-border|1100px]] | ||
If the ping requests are successful, congratulations, your setup works! If not, we suggest that you review all steps once more. | If the ping requests are successful, congratulations, your setup works! If not, we suggest that you review all steps once more. | ||
| Line 87: | Line 185: | ||
*Other types of VPNs suported by RUTxxx devices: | *Other types of VPNs suported by RUTxxx devices: | ||
**[[L2TP configuration examples]] | **[[L2TP configuration examples RutOS|L2TP configuration examples]] | ||
**[[IPsec configuration examples]] | **[[IPsec RUTOS configuration example|IPsec configuration examples]] | ||
**[[GRE Tunnel configuration examples]] | **[[GRE Tunnel configuration examples RutOS|GRE Tunnel configuration examples]] | ||
**[[OpenVPN configuration examples]] | **[[OpenVPN configuration examples|OpenVPN configuration examples]] | ||
**[[PPTP configuration examples]] | **[[PPTP configuration examples RutOS|PPTP configuration examples]] | ||
[[Category:VPN]] | |||
Latest revision as of 10:29, 22 August 2024
Main Page > General Information > Configuration Examples > VPN > L2TP over IPsec PCIntroduction
Because of the lack of confidentiality inherent in the Layer 2 Networking Protocol (L2TP), Internet Protocol Security (IPsec) is often used to secure L2TP packets by providing confidentiality, authentication and integrity. The combination of these two protocols is generally known as L2TP over IPsec (or simply L2TP/IPsec).
This article provides a guide on how to configure L2TP/IPsec on RUTxxx routers, to establish a connection with clients on their personal computers. It should also be noted that this guide is aimed at more advanced users and, therefore, skips some of the more self-explanatory steps in order to preserve the overall coherence of the article. For example, instead of showing how to add new instances step by step, it is only mentioned in a short sentence. If you feel this lack of information impedes your ability to configure the setup, we suggest you check out our separate configuration guides on IPsec and L2TP for reference.
Click Here for a user's manual based on the old style WebUI (FW version RUT9XX_R_00.06.08.6 and earlier).
Configuration overview and prerequisites
Before we begin, let's overview the configuration that we are attempting to achieve and the prerequisites that make it possible.
Prerequisites:
- One RUTxxx router of any type (excluding RUT850) with a Public Static or Public Dynamic IP addresses
- At least one end device (PC, Laptop, Tablet, Smartphone) to configure the routers and connect to the VPN.
Configuration scheme:
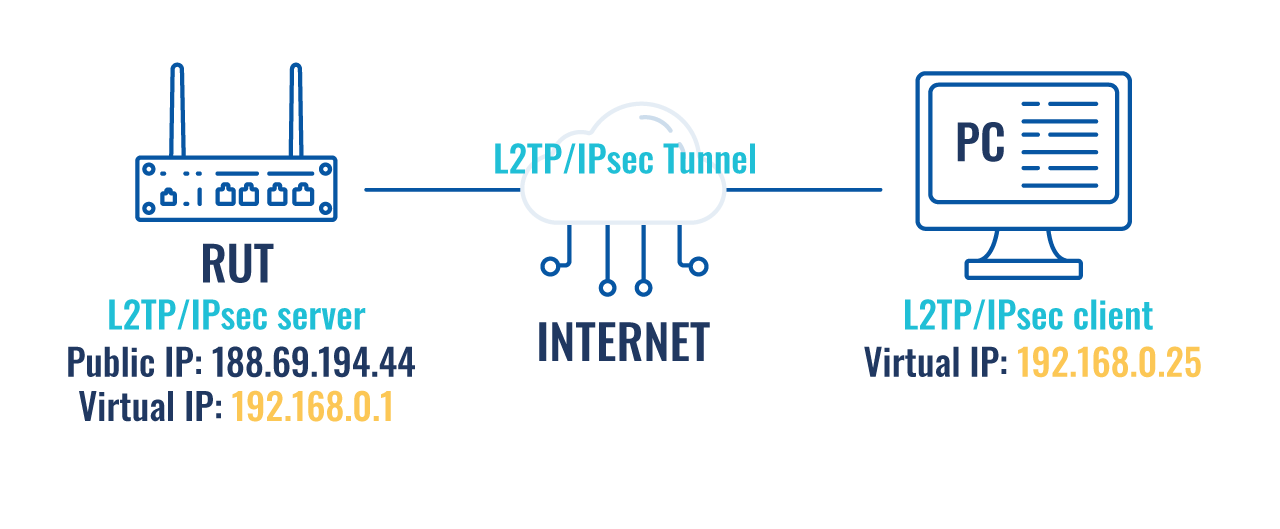
The figure above shows the L2TP/IPsec scheme. It is quite similar to the L2TP and IPsec configuration schemes - the router with the public IP address (RUT) acts as the L2TP/IPsec server and a PC acts as the client. L2TP connects the RUT and PC networks and IPsec provides the encryption for the L2TP tunnel.
When tunnel connection is established, the L2TP packets between the endpoints are encapsulated by IPsec. Since the L2TP packet itself is wrapped and hidden inside the IPsec packet, the original source and destination IP address is encrypted inside the packet.
Router configuration
If you have familiarized yourself with the configuration scheme and have all of the devices in order, we can start configuring the router using instructions provided in this section. To summarize, we'll be configuring an L2TP server and an IPsec Transport instance (server) on RUT; an L2TP/IPsec client on PC. As mentioned in the prerequisites section, the router that acts as the server must have a Public Static or Public Dynamic IP address (more information on the subject can be found here). If that is in order, we should start configuring the server.
L2TP
For more in-depth explanations about these parameters, you can visit the following wiki pages: VPN manual page, IPsec section.
IPsec
 |
|
|---|---|
|
Go to the Services → VPN → IPsec page and do the following:
|
 |
|
|---|---|
|
In the IPsec Configuration page, do the following (and leave the rest as defaults, unless your specific configuration requires otherwise):
|
 |
|
|---|---|
4. Select Bind to: Test(L2TP). |
Note: This is only an example of a secure configuration. Other algorithms or even combinations of them could be used. However, we strongly recommend refraining from using older encryption and hashing algorithms unless support for certain legacy systems is required.
Make the following changes:
 |
|
|---|---|
|
 |
|
|---|---|
|
PC Client
Finally, you need to configure a PC to connect to the VPN configuration. This subsection contains instructions on how to do just that. The relevant parameters will be encapsulated in red rectangles. Explanations about these parameters will be provided under each example.
To configure a windows PC as a client, you can use the already developed VPN function. To do this, select the search bar and type "Add a VPN connection". Then select the "Add VPN" option.
- Client configuration:

- VPN provider - VPN provider to be configured. In our case we select the "Windows (build-in)" option.
- Connection name - enter a custom name.
- Server name or address - The server with the VPN configuration to which we are going to connect. In this case, the public IP of the server is entered.
- VPN Type - Type of VPN to be configured. In our case we select "L2TP/IPsec with pre-shared key".
- Pre shared key - a shared password used for authentication between the peers. The value of this field must match the other instance.
- Type of sign-in info - VPN authentication configuration. In our case we select "Username and password".
- User name and Password - authentication information used to authenticate connecting clients. The value of this field must match the other instance.
After the configuration is done, save and select connect. After a few seconds our VPN should be connected.
Testing the setup
If you've followed all the steps presented above, your configuration should be finished. But as with any other configuration, it is always wise to test the setup in order to make sure that it works properly. The simplest way to test an IPsec connection is using the ipsec status command. You can execute this command via a command line interface (CLI). A CLI is present in all RUTxxx routers' WebUIs. To access it, login to the routers' WebUI and navigate to Services → CLI . Login to CLI with the user name root and the router's admin password. Then simply the ipsec status and press the "Enter" key:
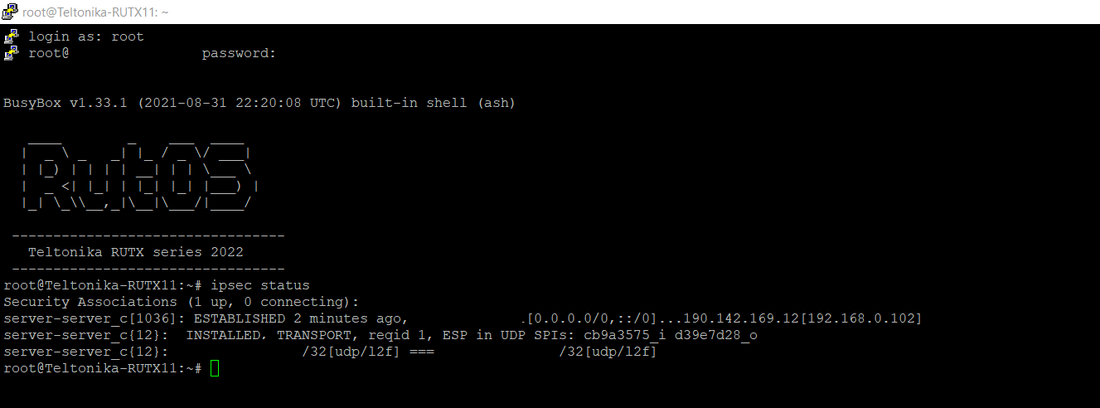
As you can see, executing ipsec status displays the number of active/inactive IPsec connections. If the connection you just configured is the only IPsec connection that you're using, you should a 1 up indication next to Security Associations.
To test an L2TP connection. You should then be able to ping the opposite instance, i.e., if you logged in to the server's CLI, you should be able to ping the client's virtual IP address, and vice versa. To use a ping command, type ping <ip_address> and press the Enter key on your keyboard:
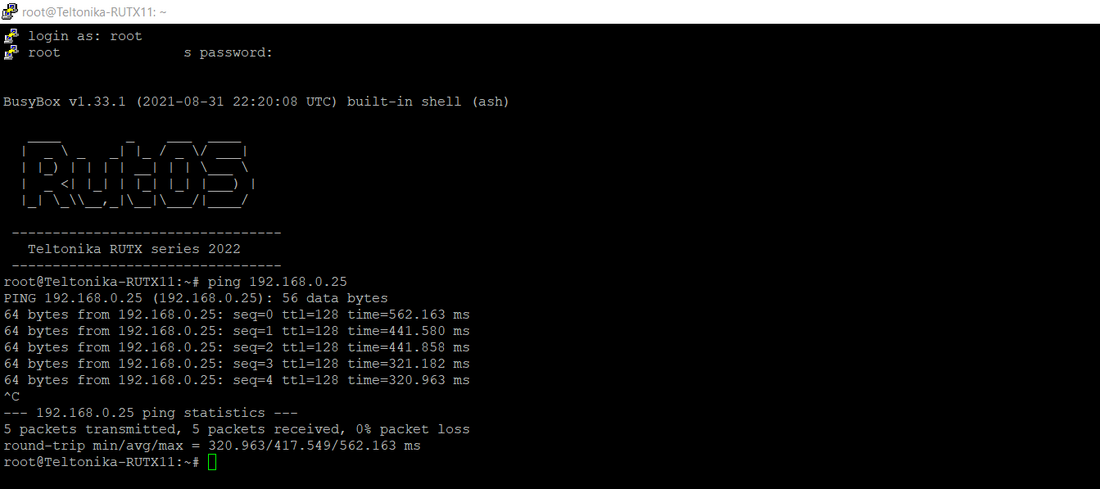
If the ping requests are successful, congratulations, your setup works! If not, we suggest that you review all steps once more.
See also
- Other types of VPNs suported by RUTxxx devices: