L2TPv3 over IPsec configuration example
The information on this page is updated in accordance with firmware version 00.07.11.3.
Introduction
Due to the inherent lack of confidentiality in the Layer 2 Tunneling Protocol (L2TP), it is commonly secured by pairing it with Internet Protocol Security (IPsec). IPsec provides essential features such as confidentiality, authentication, and integrity for L2TP packets. This combination is widely referred to as L2TP over IPsec (or simply L2TP/IPsec) and is a standard approach for secure VPN implementations.
This article provides instructions on configuring L2TPv3 over IPsec on Teltonika routers and gateway devices. Please note that the guide is designed for advanced users and skips some of the more straightforward steps to maintain overall clarity. For instance, adding new instances is only briefly mentioned rather than described in detail. If this level of information feels insufficient for your setup, consider referring to our dedicated configuration guides IPsec and L2TP for reference.
Prerequisites
- Two routers with configured VLANs, will refer to these as RUT1 and RUT2
- At least one router with a Public IP addresses (for L2TPv3/IPsec over mobile)
- Two PC devices for testing
L2TPv3/IPsec Over Wired WAN network
As mentioned in Prerequisites, two VLANs must be configured on both RUT devices. Detailed instructions for this process can be found on this page: VLAN Set Up. The remaining configuration steps are provided in this configuration example.
Topology

IPsec configuration
IPsec will be set up to ensure encrypted communication between two routers. The steps provided will guide through configuring the necessary parameters, such as authentication methods, encryption algorithms, and connection endpoints, starting with RUT1.
IPsec RUT1 Config
- Access the router's WebUI, go to Services > VPN > IPsec, and input the desired name for the new instance.
- Click the
 button
button
Instance configuration
Connection general section configuration
 |
|
|---|---|
|
Proposal configuration
Important: Both the RUT1 and RUT2 Encryptions must match in order for this configuration to work.
Phase 1:
 |
|
|---|---|
|
Phase 2:
 |
|
|---|---|
|
Note: This is only an example of a secure configuration. Other algorithms or even combinations of them could be used. However, we strongly recommend refraining from using older encryption and hashing algorithms unless support for certain legacy systems is required.
IPsec RUT2 Config
- Access the router's WebUI, go to Services > VPN > IPsec, and input the desired name for the new instance.
- Click the
 button
button
Instance configuration
Connection general section configuration
 |
|
|---|---|
|
Proposal configuration
Important: Both the RUT1 and RUT2 Encryptions must match in order for this configuration to work.
Phase 1:
 |
|
|---|---|
|
Phase 2:
 |
|
|---|---|
|
Note: This is only an example of a secure configuration. Other algorithms or even combinations of them could be used. However, we strongly recommend refraining from using older encryption and hashing algorithms unless support for certain legacy systems is required.
Testing IPsec connection
After completing the configuration, it is essential to test its functionality before proceeding further. The simplest method to test an IPsec connection is by using the swanctl -l command. This command can be executed via the command line interface (CLI)and to access the CLI, log in to the WebUI of any router (either one can be used), navigate to Services → CLI, log in to the CLI using the username root and the router's admin password. More details on accessing the CLI can be found here.
Enter the command swanctl -l and press the "Enter" key:
If "established" appears in the output along with other connection details, it indicates that the IPsec connection was successful.
L2TPv3 configuration
L2TPv3 is an enhanced version of L2TP, providing support for Layer 3 (IP) and Layer 2 (Ethernet) tunneling. It is typically used in scenarios where the need for secure data transmission across an untrusted network exists, such as remote access or site-to-site VPNs.
New L2TPv3 instances can be created from the Services > VPN > L2TPv3 section of the router's WebUI. Enter a custom name and click the "Add" button to create a new instance. Then click the "Edit" button located next to the newly created instance to enter its configuration page.
L2TPv3 RUT1 Config
- Access the router's WebUI, go to Services > VPN > L2TPv3, and input the desired name for the new instance.
- Click the
 button
button
Instance Settings
L2TPv3 RUT2 Config
- Access the router's WebUI, go to Services > VPN > L2TPv3, and input the desired name for the new instance.
- Click the
 button
button
Instance Settings
Testing L2TPv3 configuration
The simplest way to test an L2TPv3 connection is using the ip l2tp show tunnel command. You can execute this command via a command line interface (CLI). A CLI is present in all RUTxxx routers' WebUIs. To access it, login to one of the routers' WebUI (doesn't matter which one) and navigate to Services → CLI. Log in to CLI with the user name root and the router's admin password. Then simply the ip l2tp show tunnel and press the "Enter" key. If everything was configurated correctly you should see L2TPv3 tunnel information:
L2TPv3/IPsec Over Mobile Network
The configuration will be nearly identical to the L2TPv3/IPsec over Wired WAN setup, with only a few slight adjustments to the IPsec settings.
The steps for the L2TPv3 configuration will be identical to those outlined in the wired WAN configuration.
Topology

IPsec configuration
Set up IPsec following the same steps as in the wired WAN configuration, but in the RUT1 settings, leave the Remote endpoint field empty, and in the RUT2 settings, specify the RUT1 Public IP address in the Remote endpoint field.
Testing full configuration
To begin testing the setup, the first step is to verify if the traffic between RUT1 and RUT2 devices is encrypted. This can be achieved by using tcpdump, a tool that allows capturing traffic. In this example, tcpdump will be installed on RUT2, and then data passing through the device will be captured for analysis.
Installing TCP Dump
Firstly, you will need to connect to the RUT2 device's CLI/SSH. You can connect the RUT2 device CLI via WebUI by navigating to Services → CLI. Log in to CLI with the user name root and the router's admin password.
Now execute these commands one at a time:
opkg update
opkg install tcpdump
To test if TCP Dump has been installed on your device execute the command tcpdump
Installing Wireshark
To analyze the captured data from tcpdump, Wireshark will be used. While the data can be viewed directly through CLI/SSH, Wireshark provides a more detailed view and makes it easier to interpret the tcpdump output. You can download Wireshark: here.
Capturing TCP Dump
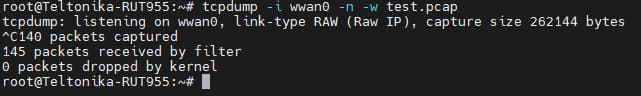
Log in to the RUT2 CLI/SSH and execute the following command:
tcpdump -i eth0.2 -vv -w test.pcap
This command captures all traffic on the wired wan interface and saves it to the test.pcap file. Leave this command running throughout the test.
Initiate a ping from PC1, connected to the RUT1 VLAN1 network, to PC2, connected to the RUT2 VLAN1 network.

Stop tcpdump command by pressing Ctrl + C.
On the RUT2 device (in the directory where the tcpdump command was executed, such as /root/ in this example), locate the test.pcap file. Extract the file to your computer. For instructions, refer to Upload & Download Files from RutOS and open this file with Wireshark. You should see similar output:
If ESP (Encapsulating Security Payload) packets are present, the configuration is functioning correctly.
If traffic is captured directly on PC2 using Wireshark, the same data will be visible, but in a decrypted format:

To summarize:
- Traffic between the IPSec routers (RUT1 and RUT2) will be encrypted while it is passing through the IPSec tunnel.
- Once the traffic reaches RUT2 (the destination router), it will be decrypted before being sent to the VLAN1 network, which includes PC2.
See also
Other types of VPNs supported by RUTxxx devices: