RUT900 VPN: Difference between revisions
No edit summary |
No edit summary |
||
| Line 4: | Line 4: | ||
| series = RUT9xx | | series = RUT9xx | ||
<!--------------------------------OPENVPN-------------------------------> | <!--------------------------------OPENVPN-------------------------------> | ||
| file_openvpn_client_config = | | file_openvpn_client_config = Networking_rutxxx_vpn_openvpn_client_configuration_v2.png | ||
| file_openvpn_server_config = | | file_openvpn_server_config = Networking_rutxxx_vpn_openvpn_server_configuration_v2.png | ||
| file_openvpn_tls_clients_config = | | file_openvpn_tls_clients_config = Networking_rutxxx_vpn_openvpn_tls_clients_configuration_v2.png | ||
<!---------------------------------IPsec--------------------------------> | <!---------------------------------IPsec--------------------------------> | ||
| file_ipsec_config = | | file_ipsec_config = Networking_rutxxx_vpn_ipsec_ipsec_configuration_v2.png | ||
| file_ipsec_phase = | | file_ipsec_phase = Networking_rutxxx_vpn_ipsec_ipsec_configuration_phase_v2.png | ||
| file_ipsec_psk = Networking_rutxxx_vpn_ipsec_pre- | | file_ipsec_psk = Networking_rutxxx_vpn_ipsec_pre-shared_keys_v2.png | ||
| file_ipsec_main_mode = Networking_device_vpn_ipsec_main_mode_scheme_v3.png | | file_ipsec_main_mode = Networking_device_vpn_ipsec_main_mode_scheme_v3.png | ||
| file_ipsec_aggressive_mode = Networking_device_vpn_ipsec_aggressive_mode_scheme_v4.png | | file_ipsec_aggressive_mode = Networking_device_vpn_ipsec_aggressive_mode_scheme_v4.png | ||
<!-------------------------------GRE Tunnel-----------------------------> | |||
| file_gre_config_main = Networking_rutxxx_vpn_gre_gre_configuration_main_settings_v1.png | |||
| file_gre_config_routing = Networking_rutxxx_vpn_gre_gre_configuration_routing_settings_v1.png | |||
<!---------------------------------PPTP---------------------------------> | |||
| file_pptp_client_config = Networking_rutxxx_vpn_pptp_client_configuration_v1.png | |||
| file_pptp_server_config = Networking_rutxxx_vpn_pptp_server_configuration_v1.png | |||
<!---------------------------------L2TP---------------------------------> | |||
| file_l2tp_client_config = Networking_rutxxx_vpn_l2tp_client_configuration_v1.png | |||
| file_l2tp_server_config = Networking_rutxxx_vpn_l2tp_server_configuration_v1.png | |||
<!---------------------------------DMVPN--------------------------------> | |||
| file_dmvpn_config = Networking_rutx_vpn_dmvpn_dmvpn_parameters_configuration_v1.png | |||
| file_dmvpn_gre_config = Networking_rutxxx_vpn_dmvpn_gre_parameters_configuration_v1.png | |||
| file_dmvpn_ipsec_config = Networking_rutxxx_vpn_dmvpn_ipsec_parameters_configuration_v1.png | |||
| file_dmvpn_nhrp_config = Networking_rutxxx_vpn_dmvpn_nhrp_parameters_configuration_v1.png | |||
}} | }} | ||
==Stunnel Configuration== | |||
Default Stunnel configuration: | Default Stunnel configuration: | ||
| Line 476: | Line 187: | ||
===Stunnel Global Configuration=== | ===Stunnel Global Configuration=== | ||
---- | |||
Default Stunnel global configuration: | Default Stunnel global configuration: | ||
| Line 525: | Line 236: | ||
Also, you must mark the global "Enabled" flag to actually enable all the individually marked configurations. | Also, you must mark the global "Enabled" flag to actually enable all the individually marked configurations. | ||
==See also== | ==See also== | ||
| Line 537: | Line 245: | ||
** [[PPTP configuration examples]] | ** [[PPTP configuration examples]] | ||
** [[L2TP configuration examples]] | ** [[L2TP configuration examples]] | ||
** [[ | ** [[DMVPN configuration]] | ||
* Configuration examples for third party VPN services | * Configuration examples for third party VPN services | ||
** [[expressvpn.com VPN configuration|expressvpn.com]] | ** [[expressvpn.com VPN configuration|expressvpn.com]] | ||
| Line 548: | Line 256: | ||
** [[OpenVPN traffic split]] | ** [[OpenVPN traffic split]] | ||
** [[OpenVPN client on Windows]] | ** [[OpenVPN client on Windows]] | ||
Revision as of 13:42, 3 July 2019
Main Page > EOL Products > RUT900 > RUT900 Manual > RUT900 WebUI > RUT900 Services section > RUT900 VPNTemplate:Networking rutxxx manual vpn
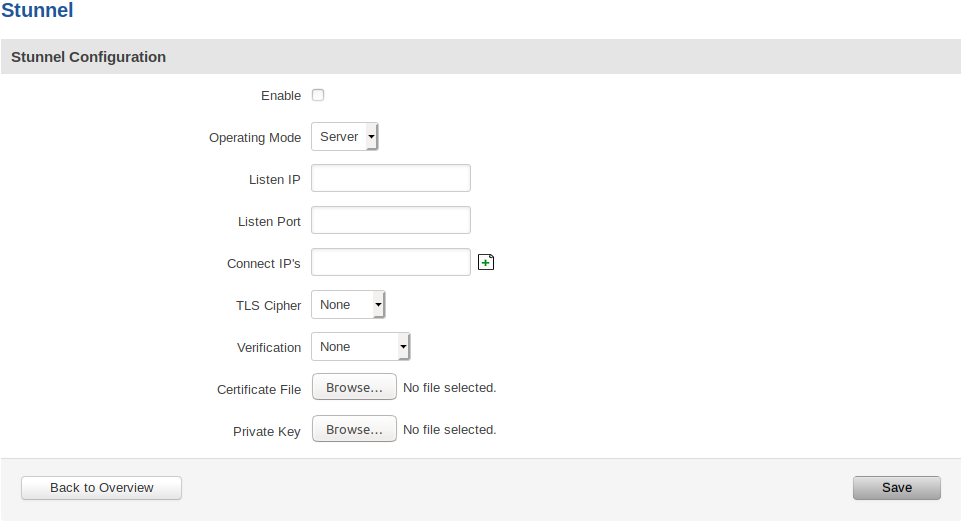
Stunnel Configuration
Default Stunnel configuration:
Stunnel configuration field explanation table:
| Field Name | Value | Description |
|---|---|---|
| Enabled | yes | no; Default: no | Enables the Stunnel configuration. |
| Operating Mode | Client | Server; Default: "" | Specifies whether this configuration will be used for Stunnel client or server. |
| Listen IP | ip | host; Default: "" | OPTIONAL Specifies which IP address or host should Stunnel listen to. If left empty, defaults to localhost. |
| Listen Port | port (integer [0..65535]); Default: "" | Specifies TCP port which Stunnel should listen to. Port cannot be taken by another service! |
| Connect IP's | [host:]port; Default: "" | Uses the standard host:port convetion (e.g. 127.0.0.1:6001; localhost:6001). Host part can be emmited - empty host part defaults to localhost. Must contain at least one item. If multiple options are specified, remote address is chosen using a round-robin algorithm. |
| TLS Cipher | None | Secure | Custom | Select permitted TLS ciphers (TLSv1.2 and below). If custom is selected, a new field appears to enter custom ciphers. |
| Allowed TLS Ciphers | Cipher[:Cipher]..; Default: "" | Only appears if a Custom TLS Cipher is selected A colon-delimited TLS cipher list (e.g. DES-CBC3-SHA:IDEA-CBC-MD5) |
| Application Protocol | Not specified | Connect | SMTP; Default: Not specified | CLIENT SIDE ONLY
This option enables initial, protocol-specific negotiation of the TLS encryption. The protocol option should not be used with TLS encryption on a separate port. If Connect or SMTP is selected, more customization fields appear. |
| Protocol Authentication | Connect: Basic | NTLM; Default: Basic SMTP: Plain | Login; Default: Plain | CLIENT SIDE ONLY
Options depend on the selected protocol Authentication type for the protocol negotiations. |
| Protocol Domain | domain (text); Default: "" | CLIENT SIDE ONLY
Only appears if a Connect protocol is selected Domain for the protocol negotiations. |
| Protocol Host | host:port; Default: "" | CLIENT SIDE ONLY
Only appears if a Connect protocol is selected Destination address for the protocol negotiations. Specifies the final TLS server to be connected to by the proxy, and not the proxy server directly connected by Stunnel. The proxy server should be specified with the connect option. |
| Protocol Username | username (text); Default: "" | CLIENT SIDE ONLY
Only appears if a protocol is selected Username for the protocol negotiations. |
| Protocol Password | password (text); Default: "" | CLIENT SIDE ONLY
Only appears if a protocol is selected Password for the protocol negotiations. |
| Verification | None | Verify Chain | Verify Peer; Default: None | Verification type. Verify Chain verifies connections against a Certificate Authority (CA) file, while Verify Peer verifies connections against a list of approved certificates. |
| Verification file | file; Default: "" | Only appears if a verification type is selected
File which is used to verify peer(s) or a peer chain. A different type of file is expected depending on the verification type selected: Verify Chain: Expects a CA (Certificate Authority) file. Verify Peer: Expects a file with one (or more, concatenated) peer certificate(s). |
| Certificate File | file; Default: "" | Mandatory for a server configuration. Optional for a client configuration
The parameter specifies the file containing certificates used by stunnel to authenticate itself against the remote client or server. The file should contain the whole certificate chain starting from the actual server/client certificate, and ending with the self-signed root CA certificate. Can be a certificate only, or both certificate and private key concatenated into a single file. |
| Private Key | file; Default: Certificate File | Can be skipped if the Certificate File is appended with the private key
Must be uploaded if the Certificate File does not contain the private key A private key, required to authenticate the certificate owner. |
After setting the parameters, click the Save button; otherwise, changes will not be saved. Some parameters will be shown in the configuration list table.
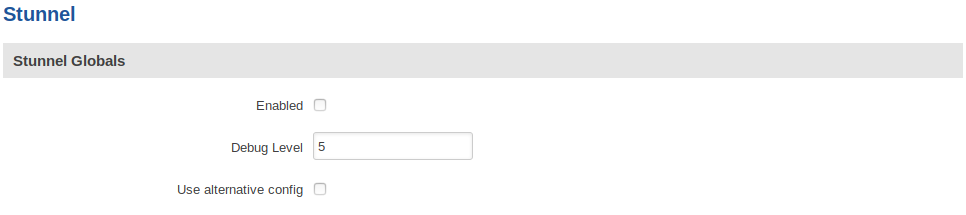
Stunnel Global Configuration
Default Stunnel global configuration:
Stunnel global configuration field explanation table:
| Field Name | Value | Description |
|---|---|---|
| Enabled | yes | no; Default: no | Enables/activates all the enabled Stunnel configurations. |
| Debug Level | integer [0..7]; Default: 5 | Debugging level. Level is one of the syslog level names or numbers emerg (0), alert (1), crit (2), err (3), warning (4), notice (5), info (6), or debug (7). All logs for the specified level and all levels numerically less than it will be shown. Use 7 for greatest debugging output. |
| Use alternative config | yes | no; Default: no | Enable alternative configuration option (Config upload). Be aware that when using alternative configuration, all configurations in Stunnel Configuration section will be skipped. |
| Upload alternative config | file; Default: "" | Only appears if the "Use alternative config" is enabled Upload the alternative Stunnel configuration file. |
IMPORTANT:
The router can have multiple configurations set up and enabled at the same time. Note that if at least one configuration is not set correctly, none of them will be enabled, despite the "Enabled" flag being marked.
Also, you must mark the global "Enabled" flag to actually enable all the individually marked configurations.
See also
- Configuration examples for RUTxxx VPN services:
- Configuration examples for third party VPN services
- Other related examples: