Difference between revisions of "OpenVPN traffic split"
PauliusRug (talk | contribs) |
|||
| (20 intermediate revisions by 7 users not shown) | |||
| Line 1: | Line 1: | ||
==Introduction== | ==Introduction== | ||
| − | + | OpenVPN is an open-source software application that implements virtual private network (VPN) techniques for creating secure point-to-point or site-to-site connections in routed or bridged configurations and remote access facilities. | |
| − | This article provides a guide on how to configure an OpenVPN client on a RUTxxx router in such a way that a part of the router's LAN clients reach the Internet through the OpenVPN server (web proxy) and the other part reaches the Internet through the router's WAN (mobile, wired or WiFi connection). It should also be noted that this guide is aimed at more advanced users and, therefore, skips some of the more self-explanatory steps in order to preserve the overall coherence of the article. For example, the step-by-step configuration of the OpenVPN client instance will be left out and only comments on certain relevant parameters will be provided. If you feel this lack of information impedes your ability to configure the setup, we suggest you check out our '''[[ | + | This article provides a guide on how to configure an OpenVPN client on a RUTxxx router in such a way that a part of the router's LAN clients reach the Internet through the OpenVPN server (web proxy) and the other part reaches the Internet through the router's WAN (mobile, wired or WiFi connection). It should also be noted that this guide is aimed at more advanced users and, therefore, skips some of the more self-explanatory steps in order to preserve the overall coherence of the article. For example, the step-by-step configuration of the OpenVPN client instance will be left out and only comments on certain relevant parameters will be provided. If you feel this lack of information impedes your ability to configure the setup, we suggest you check out our configuration guides on '''[[How to generate TLS certificates?|how to generate TLS sertificates]]''' and '''[[OpenVPN configuration examples]]''' for reference. |
==Configuration overview and prerequisites== | ==Configuration overview and prerequisites== | ||
| Line 10: | Line 10: | ||
'''Prerequisites''': | '''Prerequisites''': | ||
| − | * | + | * A single RUTxxx router (excluding [[RUT850]]) with an active internet connection that will act as the OpenVPN client |
* At least one end device (PC, Laptop) to configure the routers and test the set up | * At least one end device (PC, Laptop) to configure the routers and test the set up | ||
---- | ---- | ||
| − | ''' | + | '''Configuration scheme''': |
| − | [[File: | + | [[File:Openvpn traffic split configuration scheme.jpg|1200px]] |
| − | The figure above depicts the OpenVPN traffic split scheme. A RUTxxx router acts as an OpenVPN client (virtual IP: ''' | + | The figure above depicts the OpenVPN traffic split scheme. A RUTxxx router acts as an OpenVPN client (virtual IP: '''10.0.0.6'''; P-t-P: '''10.0.0.5''') that is connected to a remote OpenVPN server. The routers LAN IP addresses range from 192.168.1.1 to 192.168.1.254. |
| − | When the scheme is realized, Devices in the | + | When the scheme is realized, Devices in the 192.168.1.1 to 192.168.1.127 IP range reach the Internet via the router's WAN and devices in the 192.168.1.128 to 192.168.1.254 IP range reach the Internet via the OpenVPN server effectively "adopting" the server's Public IP address. |
==Router configuration== | ==Router configuration== | ||
| Line 25: | Line 25: | ||
Most of the router's configuration will be done via a command line interface. You can find detailed instruction on all command line interfaces supported by RUTxxx routers '''[[Command line interfaces|here]]'''. Choose one that is available or most preferred by you and you will still be able to follow the guide step-by-step regardless of which method you chose as the commands used will remain identical. | Most of the router's configuration will be done via a command line interface. You can find detailed instruction on all command line interfaces supported by RUTxxx routers '''[[Command line interfaces|here]]'''. Choose one that is available or most preferred by you and you will still be able to follow the guide step-by-step regardless of which method you chose as the commands used will remain identical. | ||
| − | === OpenVPN client=== | + | ===OpenVPN client=== |
---- | ---- | ||
| − | *First, you must create an OpenVPN client instance on your router. You can do this either via command line or from the router's WebUI, '''Services → VPN → OpenVPN''' section. We will not go into further detail on this because the client's configuration will depend on the OpenVPN server that you are connecting to. You can find detailed instructions on how to create and configure an OpenVPN client instance in our '''[[OpenVPN configuration examples]]''' article, which also contains information on how to configure an OpenVPN server on a RUTxxx router, if that is what you are using for this configuration. | + | * First, you must create an OpenVPN client instance on your router. You can do this either via command line or from the router's WebUI, '''Services → VPN → OpenVPN''' section. We will not go into further detail on this because the client's configuration will depend on the OpenVPN server that you are connecting to. You can find detailed instructions on how to create and configure an OpenVPN client instance in our '''[[OpenVPN configuration examples]]''' article, which also contains information on how to configure an OpenVPN server on a RUTxxx router, if that is what you are using for this configuration. |
---- | ---- | ||
| − | *Once you have configured your OpenVPN client, you should probably test whether the OpenVPN connection is operational as this will make troubleshooting easier later on. The easiest way to do so is to login to the router's WebUI and check OpenVPN status in '''Status → | + | * Once you have configured your OpenVPN client, you should probably test whether the OpenVPN connection is operational as this will make troubleshooting easier later on. The easiest way to do so is to login to the router's WebUI and check OpenVPN status in '''Status → Network → OpenVPN''': |
| − | [[File: | + | [[File:How to check openvpn status.png]] |
---- | ---- | ||
| − | *If the connection was successful, we can start the traffic split configuration. First, we'll need to | + | * If the connection was successful, we can start the traffic split configuration. First, we'll need to add an additional routing table. This can be done by issuing the following command: |
| − | == | + | echo "<span style="color:red>5 rt</span>" >> <span style="color:red>/etc/iproute2/rt_tables</span> |
| + | |||
| + | This adds a new routing table called ''rt''. ''/etc/iproute2/rt_tables'' is a file used by the ''iproute2'' utilities which translate user friendly names given on the command line into integer values used by the kernel. So the number ''5'' is just the way for the ''iproute2'' to identify the table. | ||
---- | ---- | ||
| − | *Next, we'll need to | + | * Next, we'll need to add some entries to the network configuration file ''/etc/config/network''. You can edit the file with the ''vi'' command. Type '''vi /etc/config/network''' and press the "I" button on your keyboard to begin editing. Add the following lines: |
| − | |||
| + | config interface 'vpnas' | ||
| + | option proto 'none' | ||
| + | option ifname '<span style="color:red>tun_c_MyClient</span>' | ||
| + | |||
| + | config route | ||
| + | option interface 'vpnas' | ||
| + | option target '0.0.0.0' | ||
| + | option netmask '0.0.0.0' | ||
| + | option table 'rt' | ||
| + | option gateway '<span style="color:red>10.0.0.5</span>' | ||
| + | |||
| + | config rule | ||
| + | option in 'lan' | ||
| + | option src '<span style="color:red>192.168.1.128/25</span>' | ||
| + | option lookup 'rt' | ||
| + | option priority '10' | ||
<ul> | <ul> | ||
<li> | <li> | ||
| − | + | When you're finished, press the "Esc" button and type ''':wq''' to save the changes and exit the editor (''Control + Z'' to exit without saving). The values highlighted in red are dependent on your configuration and will most likely need to be changed: | |
</li> | </li> | ||
| − | < | + | <ul> |
| − | + | <li> | |
| − | + | option ifname '<span style="color:red">tun_c_MyClient</span>' - your OpenVPN interface's name. You can check it with this command: '''ifconfig | grep tun'''. The response should look something like this: | |
| − | + | <pre> | |
| − | + | tun_c_MyClient Link encap:UNSPEC HWaddr 00-00-00-00-00-00-00-00-00-00-00-00-00-00-00-00 | |
| − | + | </pre> | |
| + | '''NOTE''': if the response is empty, your OpenVPN connection might be down. | ||
| + | </li> | ||
| + | <li> option gateway '<span style="color:red">10.0.0.5</span>' - your virtual remote endpoint (or ''P-t-P''). You can check it with this command: '''ifconfig tun_c_MyClient'''. Replace the ''MyClient'' part with your own OpenVPN interface name. The response should look something like this: | ||
| + | <pre> | ||
| + | tun_c_MyClient Link encap:UNSPEC HWaddr 00-00-00-00-00-00-00-00-00-00-00-00-00-00-00-00 | ||
| + | inet addr:10.0.0.6 P-t-P:10.0.0.5 Mask:255.255.255.255 | ||
| + | UP POINTOPOINT RUNNING NOARP MULTICAST MTU:1500 Metric:1 | ||
| + | RX packets:62249 errors:0 dropped:0 overruns:0 frame:0 | ||
| + | TX packets:62698 errors:0 dropped:1 overruns:0 carrier:0 | ||
| + | collisions:0 txqueuelen:100 | ||
| + | RX bytes:53341014 (50.8 MiB) TX bytes:11974147 (11.4 MiB) | ||
| + | </pre> | ||
| + | </li> | ||
| + | <li> | ||
| + | option src '<span style="color:red">192.168.1.128/25</span>' - devices from this IP range will use the OpenVPN server as the default gateway to the Internet. | ||
| + | </li> | ||
| + | </ul> | ||
| + | </ul> | ||
---- | ---- | ||
| − | * | + | * Finally, we'll need to add a short custom script to ''/etc/hotplug.d/iface/55-vpn'' that adds a route which makes the specified LAN range reach the Internet via the OpenVPN server: |
| − | |||
| + | echo '[ "$ACTION" = "ifup" ] && { ip route add default via 10.0.0.5 table rt }' > /etc/hotplug.d/iface/55-vpn | ||
| − | + | ==Testing the setup== | |
| − | |||
| − | + | If you've followed the steps presented above, your configuration should be finished. But as with any other configuration, it is always wise to test the setup in order to make sure that it works properly. In order to test this particular configuration, a few steps have to be taken: | |
| − | * | + | * Check the newly created routing table with the '''ip route show table rt''' command (where ''rt'' is table's name). If everything is in order, the response should contain this line (values highlighted in red should be from your own configuration): |
| − | + | default via <span style="color:red">10.0.0.5</span> dev <span style="color:red">tun_c_MyClient</span> proto static | |
| + | ---- | ||
| + | * Check whether the correct IP rule has been added. You can do this with the '''ip rule'''. The response should look something like this (the rule from our configuration is highlighted in red): | ||
| − | + | 0: from all lookup local | |
| − | + | <span style="color:red">10: from 192.168.1.128/25 iif br-lan lookup rt</span> | |
| − | + | 32766: from all lookup main | |
| − | + | 32767: from all lookup default | |
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
---- | ---- | ||
| − | + | * Check whether devices with IPs from different ranges reach the Internet through the default gateway. If you only have one device at your disposal at the time, you can configure a static IP address (guide for Linux users '''[[Setting up a Static IP address on a Ubuntu 16.04 PC|here]]'''; for Windows '''[[Setting up a Static IP address on a Windows 10 PC|here]]''') for that device in one range and later in the other. According to our configuration, if a device's IP falls in the range of 192.168.1.1 - 192.168.1.127, its Public IP should be that of the router's; if the IP falls in the range of 192.168.1.128 - 192.168.1.254, its Public IP should be that of the OpenVPN server. You can check the Public IP address in '''[http://www.whatsmyip.org/ this website]. | |
| − | |||
| − | If you' | ||
| − | |||
| − | |||
If all of the above is in order, congratulations, your configuration works! | If all of the above is in order, congratulations, your configuration works! | ||
| − | == See also== | + | ==See also== |
| − | + | * [[How to generate TLS certificates?]] | |
| − | + | * [[OpenVPN configuration examples]] | |
| − | + | * [[VPN#OpenVPN|OpenVPN manual section]] | |
| − | |||
| − | |||
| − | |||
==External links== | ==External links== | ||
| − | *http://www.whatsmyip.org/ - for checking your Public IP address | + | * http://www.whatsmyip.org/ - for checking your Public IP address |
| − | |||
Revision as of 08:53, 19 June 2018
Main Page > General Information > Configuration Examples > VPN > OpenVPN traffic splitIntroduction
OpenVPN is an open-source software application that implements virtual private network (VPN) techniques for creating secure point-to-point or site-to-site connections in routed or bridged configurations and remote access facilities.
This article provides a guide on how to configure an OpenVPN client on a RUTxxx router in such a way that a part of the router's LAN clients reach the Internet through the OpenVPN server (web proxy) and the other part reaches the Internet through the router's WAN (mobile, wired or WiFi connection). It should also be noted that this guide is aimed at more advanced users and, therefore, skips some of the more self-explanatory steps in order to preserve the overall coherence of the article. For example, the step-by-step configuration of the OpenVPN client instance will be left out and only comments on certain relevant parameters will be provided. If you feel this lack of information impedes your ability to configure the setup, we suggest you check out our configuration guides on how to generate TLS sertificates and OpenVPN configuration examples for reference.
Configuration overview and prerequisites
Before we begin, let's overview the configuration that we are attempting to achieve and the prerequisites that make it possible.
Prerequisites:
- A single RUTxxx router (excluding RUT850) with an active internet connection that will act as the OpenVPN client
- At least one end device (PC, Laptop) to configure the routers and test the set up
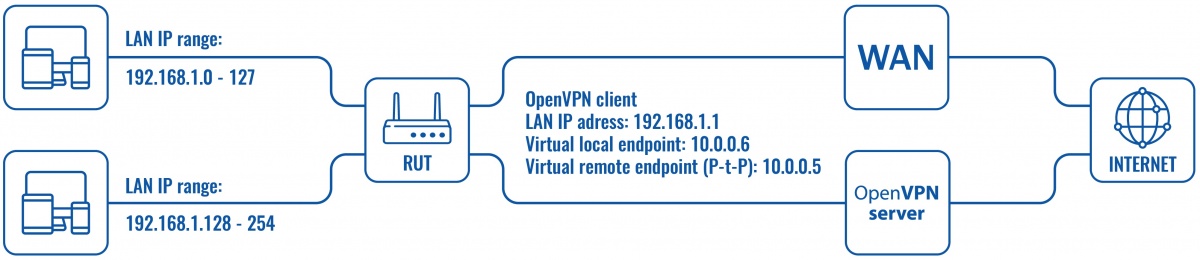
Configuration scheme:
The figure above depicts the OpenVPN traffic split scheme. A RUTxxx router acts as an OpenVPN client (virtual IP: 10.0.0.6; P-t-P: 10.0.0.5) that is connected to a remote OpenVPN server. The routers LAN IP addresses range from 192.168.1.1 to 192.168.1.254.
When the scheme is realized, Devices in the 192.168.1.1 to 192.168.1.127 IP range reach the Internet via the router's WAN and devices in the 192.168.1.128 to 192.168.1.254 IP range reach the Internet via the OpenVPN server effectively "adopting" the server's Public IP address.
Router configuration
Most of the router's configuration will be done via a command line interface. You can find detailed instruction on all command line interfaces supported by RUTxxx routers here. Choose one that is available or most preferred by you and you will still be able to follow the guide step-by-step regardless of which method you chose as the commands used will remain identical.
OpenVPN client
- First, you must create an OpenVPN client instance on your router. You can do this either via command line or from the router's WebUI, Services → VPN → OpenVPN section. We will not go into further detail on this because the client's configuration will depend on the OpenVPN server that you are connecting to. You can find detailed instructions on how to create and configure an OpenVPN client instance in our OpenVPN configuration examples article, which also contains information on how to configure an OpenVPN server on a RUTxxx router, if that is what you are using for this configuration.
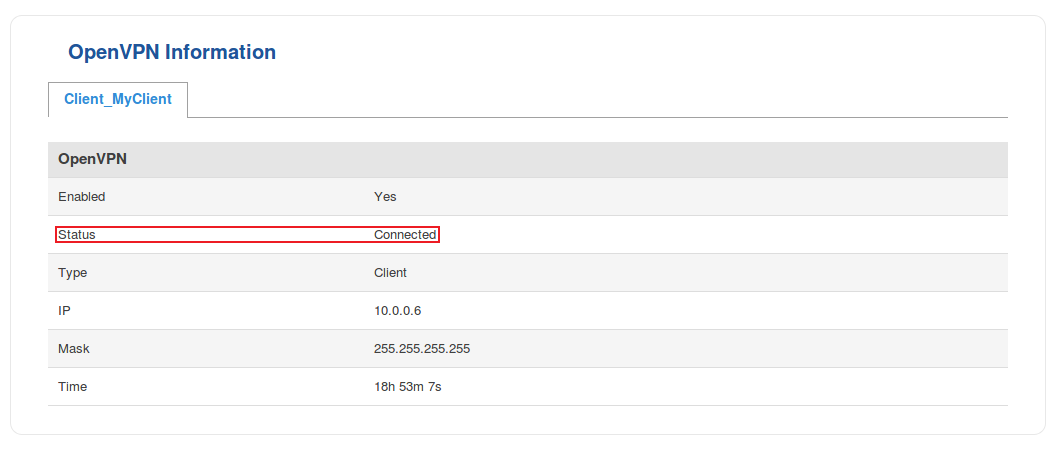
- Once you have configured your OpenVPN client, you should probably test whether the OpenVPN connection is operational as this will make troubleshooting easier later on. The easiest way to do so is to login to the router's WebUI and check OpenVPN status in Status → Network → OpenVPN:
- If the connection was successful, we can start the traffic split configuration. First, we'll need to add an additional routing table. This can be done by issuing the following command:
echo "5 rt" >> /etc/iproute2/rt_tables
This adds a new routing table called rt. /etc/iproute2/rt_tables is a file used by the iproute2 utilities which translate user friendly names given on the command line into integer values used by the kernel. So the number 5 is just the way for the iproute2 to identify the table.
- Next, we'll need to add some entries to the network configuration file /etc/config/network. You can edit the file with the vi command. Type vi /etc/config/network and press the "I" button on your keyboard to begin editing. Add the following lines:
config interface 'vpnas'
option proto 'none'
option ifname 'tun_c_MyClient'
config route
option interface 'vpnas'
option target '0.0.0.0'
option netmask '0.0.0.0'
option table 'rt'
option gateway '10.0.0.5'
config rule
option in 'lan'
option src '192.168.1.128/25'
option lookup 'rt'
option priority '10'
- When you're finished, press the "Esc" button and type :wq to save the changes and exit the editor (Control + Z to exit without saving). The values highlighted in red are dependent on your configuration and will most likely need to be changed:
-
option ifname 'tun_c_MyClient' - your OpenVPN interface's name. You can check it with this command: ifconfig | grep tun. The response should look something like this:
tun_c_MyClient Link encap:UNSPEC HWaddr 00-00-00-00-00-00-00-00-00-00-00-00-00-00-00-00
NOTE: if the response is empty, your OpenVPN connection might be down.
- option gateway '10.0.0.5' - your virtual remote endpoint (or P-t-P). You can check it with this command: ifconfig tun_c_MyClient. Replace the MyClient part with your own OpenVPN interface name. The response should look something like this:
tun_c_MyClient Link encap:UNSPEC HWaddr 00-00-00-00-00-00-00-00-00-00-00-00-00-00-00-00 inet addr:10.0.0.6 P-t-P:10.0.0.5 Mask:255.255.255.255 UP POINTOPOINT RUNNING NOARP MULTICAST MTU:1500 Metric:1 RX packets:62249 errors:0 dropped:0 overruns:0 frame:0 TX packets:62698 errors:0 dropped:1 overruns:0 carrier:0 collisions:0 txqueuelen:100 RX bytes:53341014 (50.8 MiB) TX bytes:11974147 (11.4 MiB) - option src '192.168.1.128/25' - devices from this IP range will use the OpenVPN server as the default gateway to the Internet.
- Finally, we'll need to add a short custom script to /etc/hotplug.d/iface/55-vpn that adds a route which makes the specified LAN range reach the Internet via the OpenVPN server:
echo '[ "$ACTION" = "ifup" ] && { ip route add default via 10.0.0.5 table rt }' > /etc/hotplug.d/iface/55-vpn
Testing the setup
If you've followed the steps presented above, your configuration should be finished. But as with any other configuration, it is always wise to test the setup in order to make sure that it works properly. In order to test this particular configuration, a few steps have to be taken:
- Check the newly created routing table with the ip route show table rt command (where rt is table's name). If everything is in order, the response should contain this line (values highlighted in red should be from your own configuration):
default via 10.0.0.5 dev tun_c_MyClient proto static
- Check whether the correct IP rule has been added. You can do this with the ip rule. The response should look something like this (the rule from our configuration is highlighted in red):
0: from all lookup local
10: from 192.168.1.128/25 iif br-lan lookup rt
32766: from all lookup main
32767: from all lookup default
- Check whether devices with IPs from different ranges reach the Internet through the default gateway. If you only have one device at your disposal at the time, you can configure a static IP address (guide for Linux users here; for Windows here) for that device in one range and later in the other. According to our configuration, if a device's IP falls in the range of 192.168.1.1 - 192.168.1.127, its Public IP should be that of the router's; if the IP falls in the range of 192.168.1.128 - 192.168.1.254, its Public IP should be that of the OpenVPN server. You can check the Public IP address in this website.
If all of the above is in order, congratulations, your configuration works!
See also
External links
- http://www.whatsmyip.org/ - for checking your Public IP address